H12-841_V1.5 HCIP-Datacom-Campus Network Planning and Deployment V1.5 Questions and Answers
(Traffic of a traditional network is transmitted to the VXLAN network through the edge node. A VXLAN network accesses an external network through the ______ node.)
(When access authentication is deployed on a network, which of the following servers typically reside in the pre-authentication domain?)
(iMaster NCE-Campus provides independent working interfaces on different planes: management plane and service plane. You can log in to each plane through a specific IP address and port number. The port number of the service plane is _____.)
(Which of the following statements about static VXLAN tunnel configuration are true?Choose all that apply.)
(In the Huawei CloudCampus Solution, which of the following deployment modes are supported by Huawei switches?)
(The Huawei CloudCampus Solution supports various rate limiting modes for wireless users in small- and medium-sized campus scenarios. Which of the following modes is suitable for refined traffic control of each user?)
(On a small- or medium-sized campus network, multi-carrier links can be deployed at the egress for backup to ensure egress reliability.)
(When you configure a virtualized campus network on iMaster NCE-Campus, creating a virtual network is equivalent to creating a VPN instance to isolate different services.)
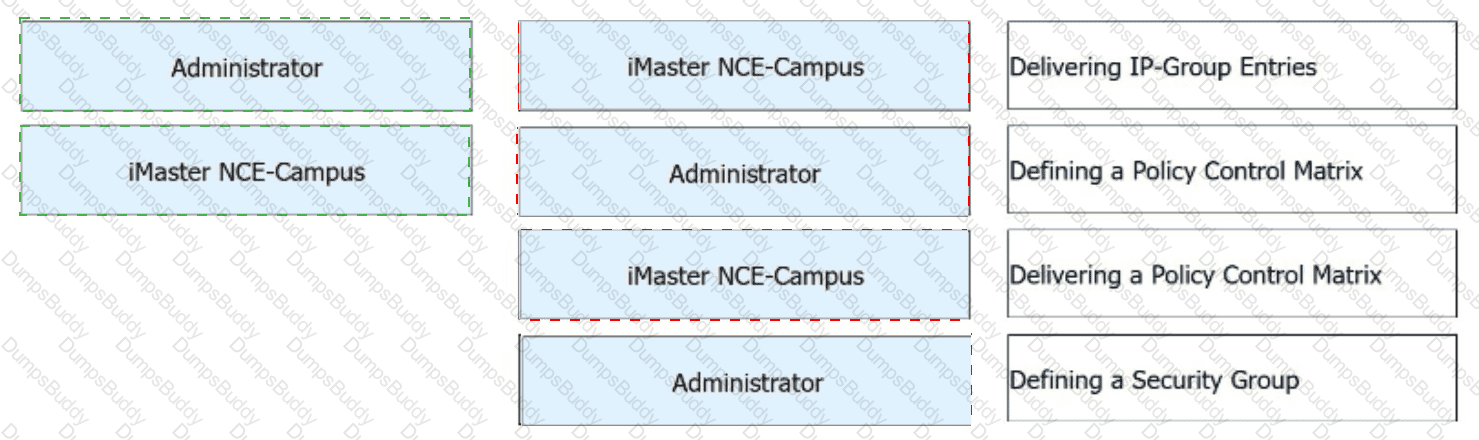
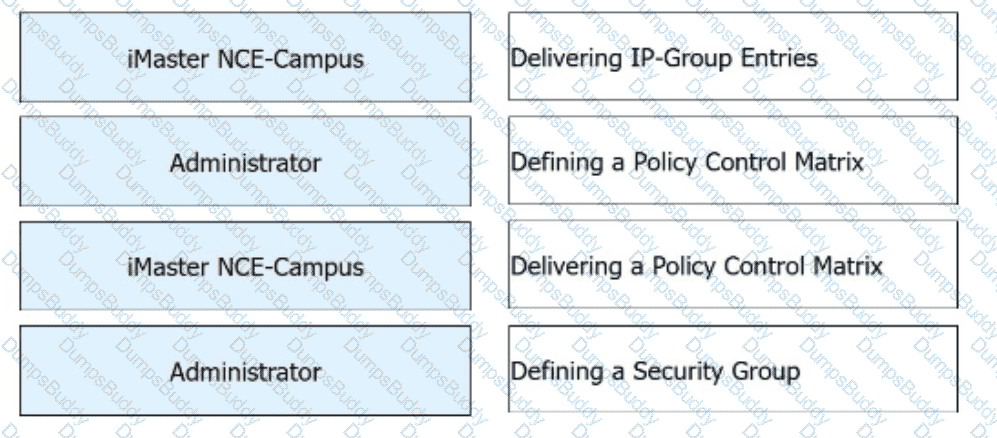
Free mobility is deployed on a campus network through iMaster NCE-Campus. During this deployment, which of the following steps are performed by administrators and which are automatically performed by iMaster NCE-Campus?

(Which of the following commands needs to be run in the BGP view to enable a VPN instance to advertise IP routes to the BGP-EVPN address family?)
(When a network device sends a registration request to iMaster NCE-Campus, which of the following is the destination port number?)
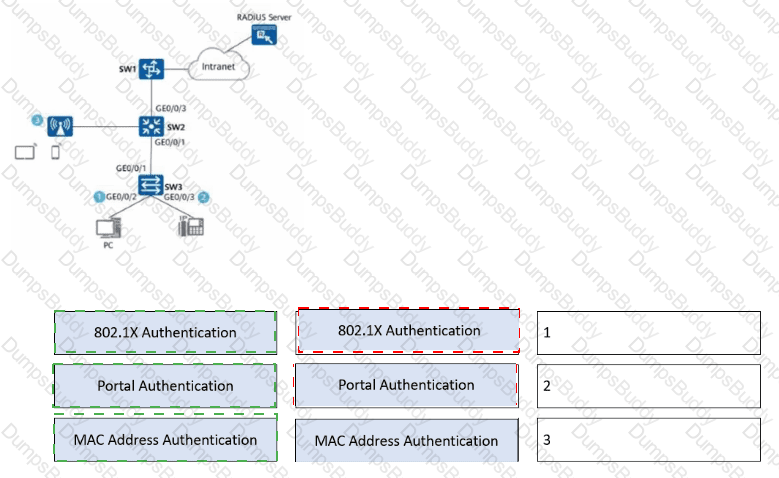
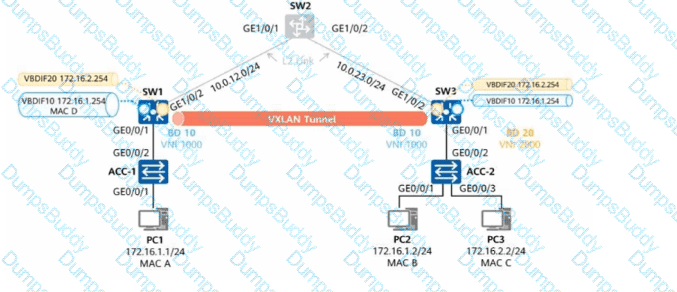
(Refer to the figure.
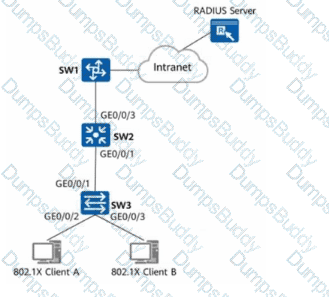
Which of the following steps aremandatoryto enable 802.1X authentication on GE0/0/2 and GE0/0/3 of SW3 and configure a RADIUS server to authenticate and deliver network access rights to users?Choose all that apply.)
(DHCP snooping is a security feature of DHCP that prevents DHCP servers and clients from being attacked. Which of the following statements about DHCP snooping are true?Choose all that apply.)
(On a CloudCampus virtualized campus network, which of the following modes can be used by a fabric to connect to external networks?Choose all that apply.)
(During WLAN planning and design, channels 1, 6, and 11 are recommended on the 2.4 GHz frequency band, and channels 1, 5, 9, and 13 are recommended in high-density scenarios. On the 5 GHz frequency band, it is recommended that high-frequency and low-frequency channels of adjacent APs be staggered to prevent overlapping.)
(After the Huawei CloudCampus Solution is deployed on a campus network, which of the following protocol packets may be exchanged between the management layer and network layer?)
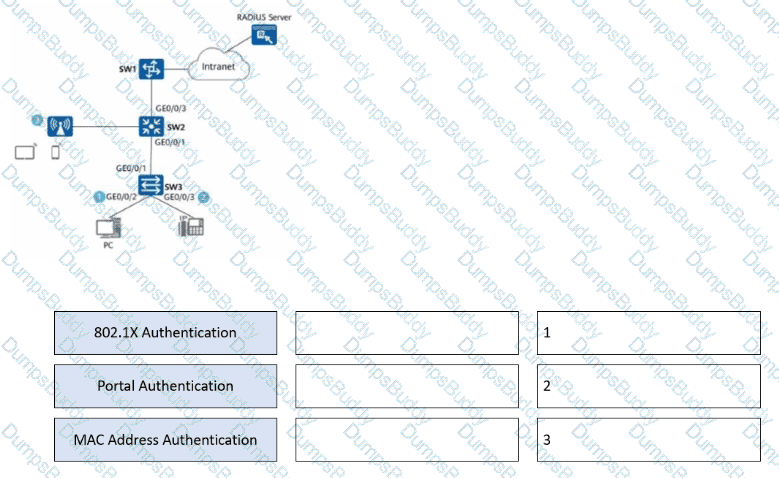
Network admission control (NAC) needs to be deployed on the network shown in the figure. Drag a proper authentication mode to each authentication point.
(Huawei switches support VLAN assignment based on interface, MAC address, protocol, and IP address.)
(The Huawei CloudCampus Solution divides the network architecture into three layers: network layer, management layer, and application layer.)
(An MSP administrator creates a tenant account. Which of the following logs records the operation?)
(On a small- or medium-sized campus network deployed based on the Huawei CloudCampus Solution, an AR functioning as the egress gateway supports web-based network management, registration center query, and DHCP Option 148-based deployment, but does not support CLI-based deployment.)
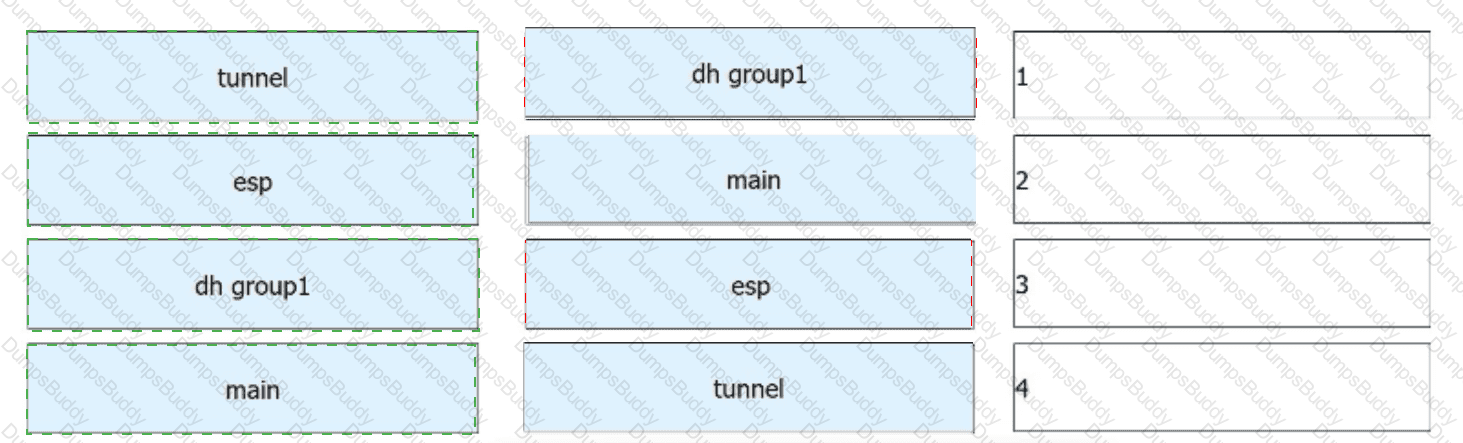
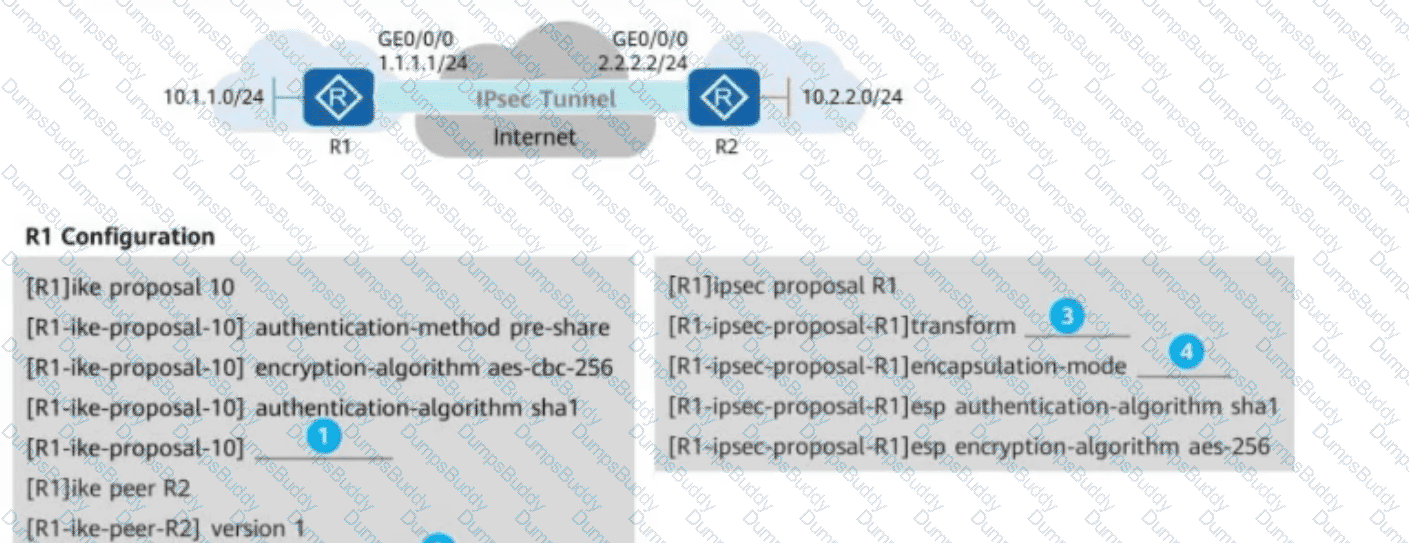
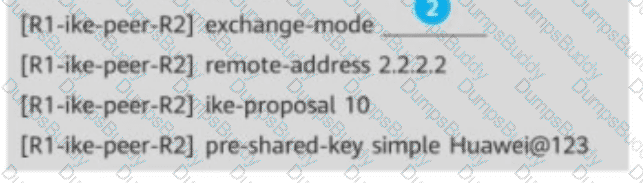
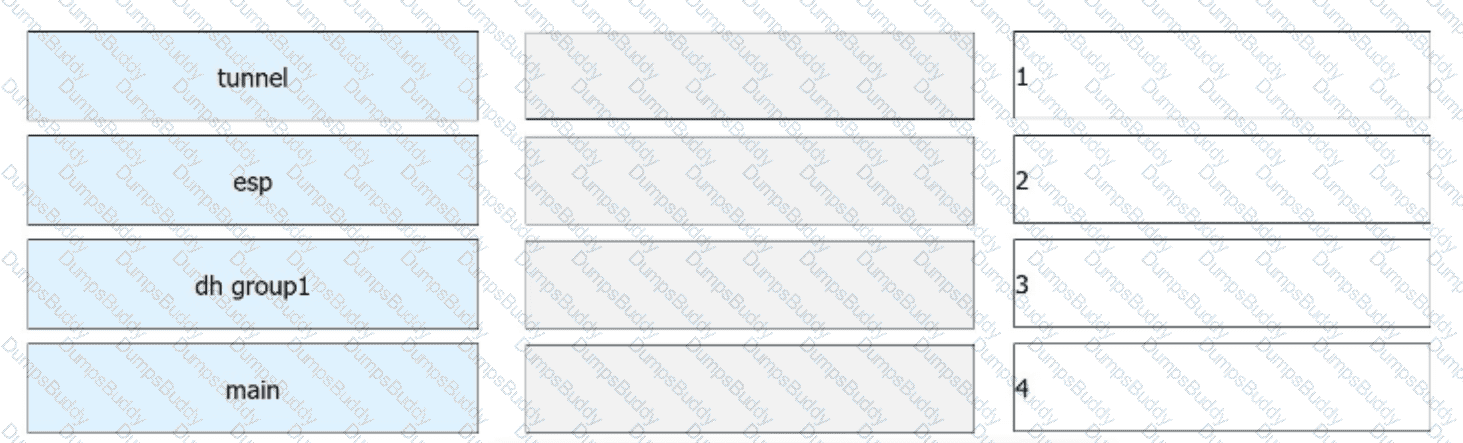
(As shown in the following figure, R1 and R2 establish an IPsec VPN in ISAKMP mode for communication. For IPsec proposals on R1 and R2, ESP is used, the encapsulation mode is set to tunnel mode, SHA1 is configured as the authentication algorithm, and AES-256 is configured as the encryption algorithm. In addition, IKEv1 is configured for IKE peers, the main mode is configured for IKEv1 negotiation phase 1, and the PSK Huawei@123 is configured for PSK authentication between IKE peers. For IKE proposals on R1 and R2, SHA1 is configured as the authentication algorithm, AES-256 is configured as the encryption algorithm, and DH group 1 is configured for IKE negotiation. Based on these configurations on R1 and R2, drag the configuration items on the left to the correct locations on the right.)
(Which of the following fields in the ESP protocol is used to prevent replay attacks?)
(As shown in the figure, distributed VXLAN gateways are used, and thearp-proxy local enablecommand is configured onVBDIF 10 of SW1. Which of the following statements aretrue?)
(To isolate communication between wired terminals, you can enable port isolation on the access switches. However, APs cannot implement wireless user isolation.)
(Which of the following statements about authentication profile configuration is true?)
(Which of the following information types are transmitted through enhanced BGP EVPN in Huawei SD-WAN Interconnection Solution?)