H12-711_V4.0 HCIA-Security V4.0 Exam Questions and Answers
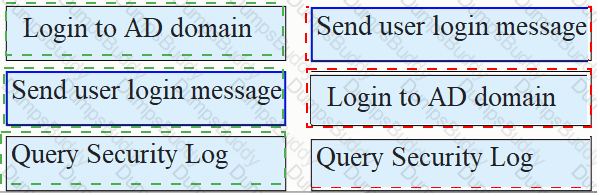
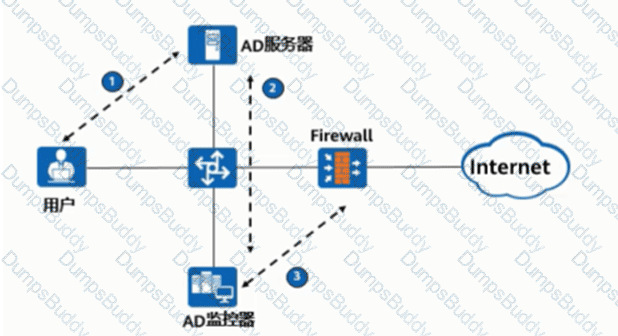
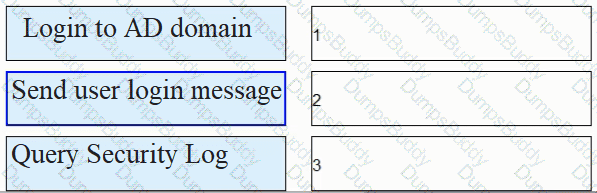
As shown in the figure, the process of AD single sign-on (querying the security log mode of AD server), please match the corresponding operation process.
Regarding the characteristics of the routing table, which of the following items is described correctly
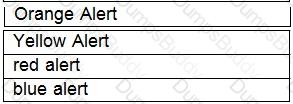
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*
The traffic direction of a firewall is based on the zone priority. The _____ direction refers to the direction from a low-priority zone to a high-priority zone. Capitalize the first letter.
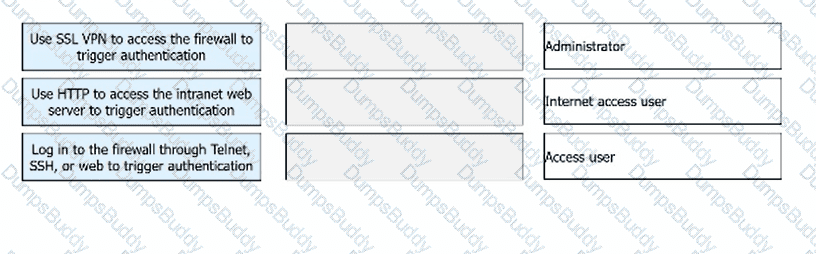
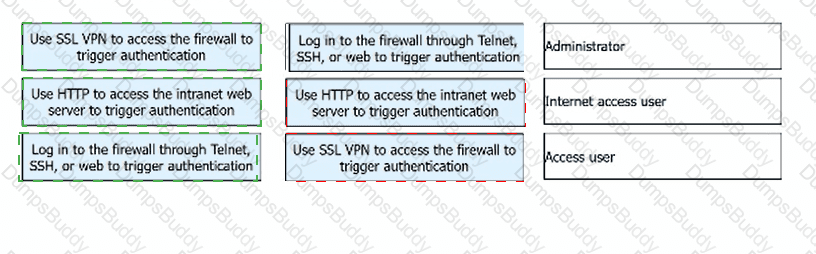
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
IPSec VPN uses an asymmetric algorithm to calculate the ___ key to encrypt data packets.[fill in the blank]
In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
In the PKI certificate revocation process, a user needs to send a signed and encrypted email to the RA to apply for certificate revocation.
A Web server is deployed in an enterprise intranet to provide Web access services to Internet users, and in order to protect the access security of the server, it should be divided into the _____ area of the firewall.
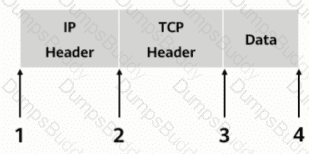
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
During the process of establishing IPSec VPN between peers FW_A and FW_B, two types of security associations need to be established in two stages. In the first stage, _____ is established to verify the identity of the peers.[fill in the blank]*
Which of the following statements are incorrect about the differences between routers and Layer 2 switches?
The keys used by the IPSec encryption and authentication algorithms can be configured manually or dynamically negotiated via the ____ protocol. (abbreviation, all uppercase).
Using the ___ method of the Web proxy, the virtual gateway will encrypt the real URL that the user wants to access, and can adapt to different terminal types.[fill in the blank]*
Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution. 1. Inhibition stage, 2. recovery phase, 3. Detection stage, 4. eradication phase[fill in the blank]*
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.

Both digital envelopes and digital signatures guarantee data security and verify the origin of data.
While working for a company, Tom receives an email with an attachment. Which of the following operations is correct?
What is correct about the following description of device management in the operating system?
A three-way handshake is required to establish a TCP connection, and a four-way handshake is required to end a TCP connection.
In the TCP/P protocol core, which of the following protocols works at the application layer?
Digital envelope technology means that the sender uses the receiver's public key to encrypt the data, and then sends the ciphertext to the receiver
When IKEv1 negotiation phase 1 uses the aggressive mode, only three messages are used. Which of the following is the function of message 3?
Which of the following attack methods is to construct special SQL statements and submit sensitive information to exploit program vulnerabilities
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
Devices that need to provide network services externally, such as WWW servers and FTP servers, can be placed in the DMZ.
What is correct in the following description of Security Alliance in IPSec?
There are two ways to set up an IPSec SA
The following description of asymmetric encryption algorithms, which item is wrong?