CCOA ISACA Certified Cybersecurity Operations Analyst Questions and Answers
Multi-factor authentication (MFA) BEST protects against which of the following attack vectors?
Which of (he following is the PRIMARY reason to regularly review firewall rules?
A nation-state that is employed to cause financial damage on an organization is BEST categorized as:
Which of the following is the GREATEST risk resulting from a Domain Name System (DNS) cache poisoning attack?
Which of the following is theMOSTimportant component oftheasset decommissioning process from a data risk perspective?
An organization's hosted database environment is encrypted by the vendor at rest and in transit. The database was accessed, and critical data was stolen. Which of the following is the MOST likely cause?
In which phase of the Cyber Kill Chain" would a red team run a network and port scan with Nmap?
As part of a penetration testing program, which team facilitates education and training of architects and developers to encourage better security and awareness?
After identified weaknesses have been remediated, which of the following should be completed NEXT?
A penetration tester has been hired and given access to all code, diagrams,and documentation. Which type oftesting is being conducted?
Question 1 and 2
You have been provided with authentication logs toinvestigate a potential incident. The file is titledwebserver-auth-logs.txt and located in theInvestigations folder on the Desktop.
Which IP address is performing a brute force attack?
What is the total number of successful authenticationsby the IP address performing the brute force attack?
The enterprise is reviewing its security posture byreviewing unencrypted web traffic in the SIEM.
How many logs are associated with well knownunencrypted web traffic for the month of December2023 (Absolute)? Note: Security Onion refers to logsas documents.
An employee has been terminated for policy violations.Security logs from win-webserver01 have been collectedand located in the Investigations folder on theDesktop as win-webserver01_logs.zip.
Create a new case in Security Onion from the win-webserver01_logs.zip file. The case title is WindowsWebserver Logs - CCOA New Case and TLP must beset to Green. No additional fields are required.
Your enterprise has received an alert bulletin fromnational authorities that the network has beencompromised at approximately 11:00 PM (Absolute) onAugust 19, 2024. The alert is located in the alerts folderwith filename, alert_33.pdf.
Use the IOCs to find the compromised host. Enter thehost name identified in the keyword agent.name fieldbelow.
For this question you must log into GreenboneVulnerability Manager using Firefox. The URL is:https://10.10.55.4:9392 and credentials are:
Username:admin
Password:Secure-gvm!
A colleague performed a vulnerability scan but did notreview prior to leaving for a family emergency. It hasbeen determined that a threat actor is using CVE-2021-22145 in the wild. What is the host IP of the machinethat is vulnerable to this CVE?
Analyze the file titled pcap_artifact5.txt on the AnalystDesktop.
Decode the C2 host of the attack. Enter your responsebelow.
On the Analyst Desktop is a Malware Samples folderwith a file titled Malscript.viruz.txt.
What is the name of the service that the malware attempts to install?
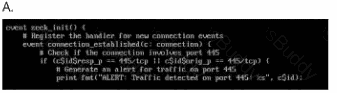
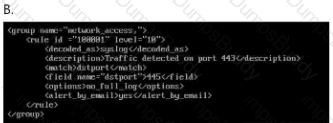
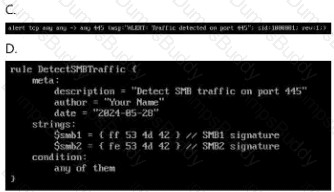
Which ruleset can be applied in the
/home/administrator/hids/ruleset/rules directory?
Double-click each image to view it larger.
An employee has been terminated for policy violations.Security logs from win-webserver01 have been collectedand located in the Investigations folder on theDesktop as win-webserver01_logs.zip.
Generate a SHA256 digest of the System-logs.evtx filewithin the win-webserver01_logs.zip file and providethe output below.
The CISO has received a bulletin from law enforcementauthorities warning that the enterprise may be at risk ofattack from a specific threat actor. Review the bulletin
named CCOA Threat Bulletin.pdf on the Desktop.
Which host IP was targeted during the following timeframe: 11:39 PM to 11:43 PM (Absolute) on August 16,2024?
Following a ransomware incident, the network teamprovided a PCAP file, titled ransom.pcap, located in theInvestigations folder on the Desktop.
What is the name of the file containing the ransomwaredemand? Your response must include the fileextension.
The enterprise is reviewing its security posture byreviewing unencrypted web traffic in the SIEM.
How many unique IPs have received well knownunencrypted web connections from the beginning of2022 to the end of 2023 (Absolute)?
Following a ransomware incident, the network teamprovided a PCAP file, titled ransom.pcap, located in theInvestigations folder on the Desktop.
What is the full User-Agent value associated with theransomware demand file download. Enter your responsein the field below.
The network team has provided a PCAP file withsuspicious activity located in the Investigations folderon the Desktop titled, investigation22.pcap.
What date was the webshell accessed? Enter the formatas YYYY-MM-DD.
Your enterprise SIEM system is configured to collect andanalyze log data from various sources. Beginning at12:00 AM on December 4, 2024, until 1:00 AM(Absolute), several instances of PowerShell arediscovered executing malicious commands andaccessing systems outside of their normal workinghours.
What is the physical address of the web server that wastargeted with malicious PowerShell commands?
The CISO has received a bulletin from law enforcementauthorities warning that the enterprise may be at risk ofattack from a specific threat actor. Review the bulletin
named CCOA Threat Bulletin.pdf on the Desktop.
Which of the following domain name(s) from the CCOAThreat Bulletin.pdf was contacted between 12:10 AMto 12:12 AM (Absolute) on August 17, 2024?
Analyze the file titled pcap_artifact5.txt on the AnalystDesktop.
Decode the contents of the file and save the output in atext file with a filename of pcap_artifact5_decoded.txton the Analyst Desktop.
The network team has provided a PCAP file withsuspicious activity located in the Investigations folderon the Desktop titled, investigation22.pcap.
What is the filename of the webshell used to control thehost 10.10.44.200? Your response must include the fileextension.
In the Open Systems Interconnection (OSI) Model for computer networking, which of the following is the function of the network layer?
On the Analyst Desktop is a Malware Samples folderwith a file titled Malscript.viruz.txt.
Based on the contents of the malscript.viruz.txt, whichthreat actor group is the malware associated with?
A change advisory board Is meeting to review a remediation plan for a critical vulnerability, with a cybersecurity analyst in attendance. When asked about measures to address post-implementation issues, which o! the following would be the analyst's BEST response?
Analyze the file titled pcap_artifact5.txt on the AnalystDesktop.
Decode the targets within the file pcap_artifact5.txt.
Select the correct decoded targets below.
10cal.com/exam
clOud-s3cure.com
c0c0nutf4rms.net
h3avy_s3as.biz
b4ddata.org
The user of the Accounting workstation reported thattheir calculator repeatedly opens without their input.
The following credentials are used for thisquestion.
Username:Accounting
Password:1x-4cc0unt1NG-x1
Using the provided credentials, SSH to the Accountingworkstation and generate a SHA256 checksum of the filethat triggered RuleName Suspicious PowerShell usingeither certutil or Get-FileHash of the file causing theissue. Copy the hash and paste it below.
Which type of cloud deployment model is intended to be leveraged over the Internet by many organizations with varying needs and requirements?


