TPAD01 Threat Protection Administrator Exam Questions and Answers
What are the three default methods available in Recipient Verification to verify that a recipient mailbox exists?
Pick the 3 correct responses below.
You want an administrator, Peter Smith, to receive alerts when the SMTP Queue exceeds the configured threshold. How would you configure this?
Pick the 2 correct responses below.
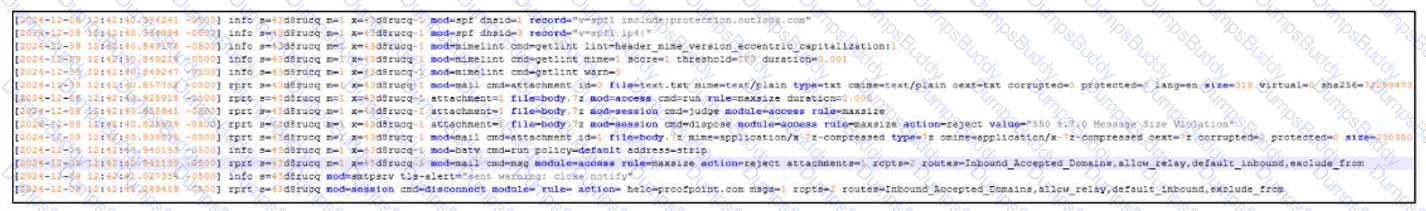
Refer to the exhibit to see the interface used in this scenario.

Which of the following is true regarding the inbound mail route?
A SAML authentication profile is configured on the Proofpoint Protection Server console. Which portals can be accessed using this configuration?
Which of the following is required to configure an outbound mail route in the Proofpoint Protection Server?
Pick the 3 correct responses below.
You have just been licensed to export the Smart Search data from your PoD protection server in JSON format. Where would you create the API keys needed by your SIEM to ingest the JSON stream?
The Abuse Mailbox event source was working in Cloud Threat Protection, but is now showing red under status and is no longer processing emails. After editing the source and clicking “Validate Source,” you receive the error “Unable to validate mailbox.” What is the likely cause of this error?
Which of the following are true regarding Spam Detection?
Pick the 3 correct responses below.
You wish to ensure that all emails to an external partner are sent over a secure connection. What should you do?
If an email is incorrectly filtered as spam, what should an administrator do first when reviewing the filter logs?