PCCET Palo Alto Networks Certified Cybersecurity Entry-level Technician Questions and Answers
On an endpoint, which method should you use to secure applications against exploits?
Which product from Palo Alto Networks enables organizations to prevent successful cyberattacks as well as simplify and strengthen security processes?
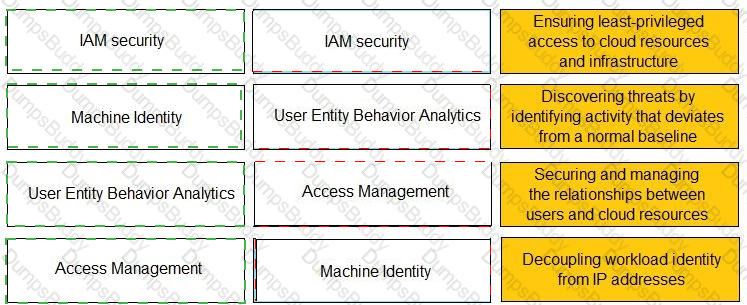
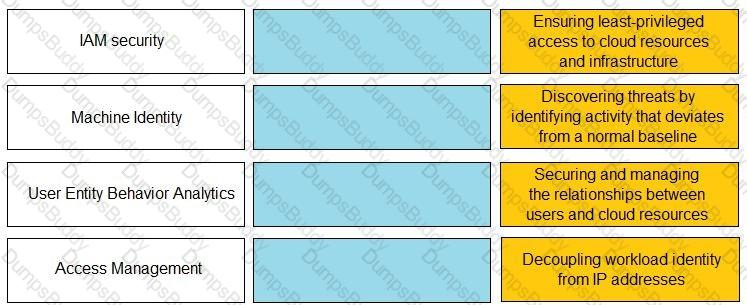
Match the Identity and Access Management (IAM) security control with the appropriate definition.
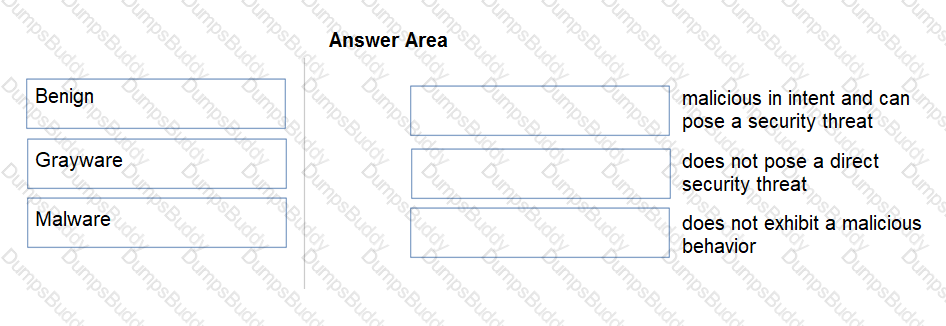
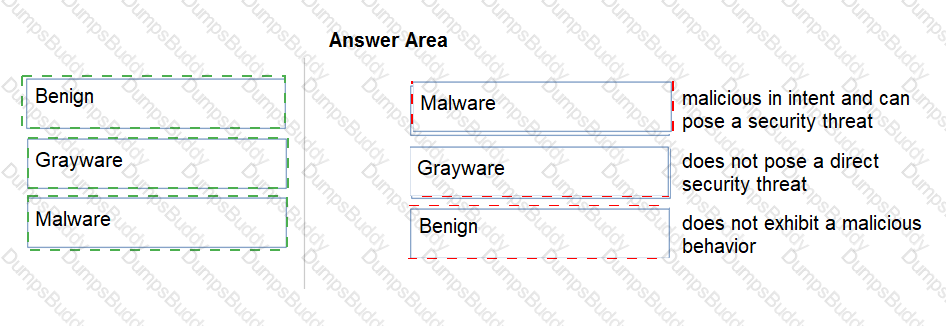
Under which category does an application that is approved by the IT department, such as Office 365, fall?
Which option would be an example of PII that you need to prevent from leaving your enterprise network?
In which phase of the cyberattack lifecycle do attackers establish encrypted communication channels back to servers across the internet so that they can modify their attack objectives and methods?
Which NGFW feature is used to provide continuous identification, categorization, and control of known and previously unknown SaaS applications?
The seventy of an attack needs to be escalated.
What needs to be in place in order for the security operations team to properly inform various units within the enterprise of the issue?
You received an email, allegedly from a bank, that asks you to click a malicious link to take action on your account.
Which type of attack is this?
Which attacker profile acts independently or as part of an unlawful organization?
Which two pieces of information are considered personally identifiable information (PII)? (Choose two.)
Which characteristic of serverless computing enables developers to quickly deploy application code?
A doctor receives an email about her upcoming holiday in France. When she clicks the URL website link in the email, the connection is blocked by her office firewall because it's a known malware website. Which type of attack includes a link to a malware website in an email?
Which network firewall primarily filters traffic based on source and destination IP address?
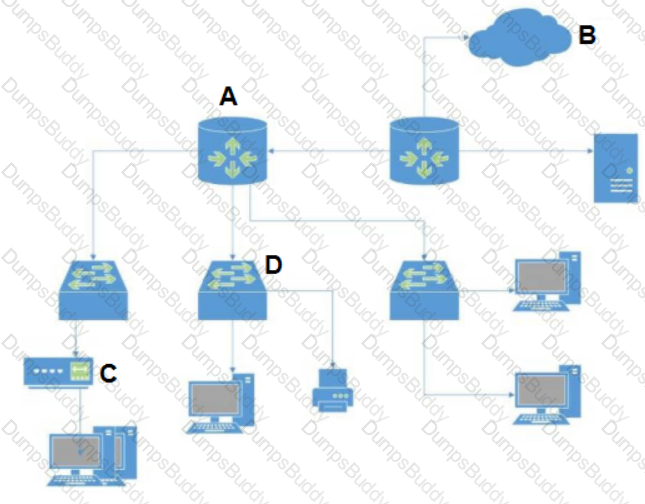
You have been invited to a public cloud design and architecture session to help deliver secure east west flows and secure Kubernetes workloads.
What deployment options do you have available? (Choose two.)
What protocol requires all routers in the same domain to maintain a map of the network?
Which product from Palo Alto Networks extends the Security Operating Platform with the global threat intelligence and attack context needed to accelerate analysis, forensics, and hunting workflows?
What is required for a SIEM to operate correctly to ensure a translated flow from the system of interest to the SIEM data lake?
Data Loss Prevention (DLP) and Cloud Access Security Broker (CASB) fall under which Prisma access service layer?
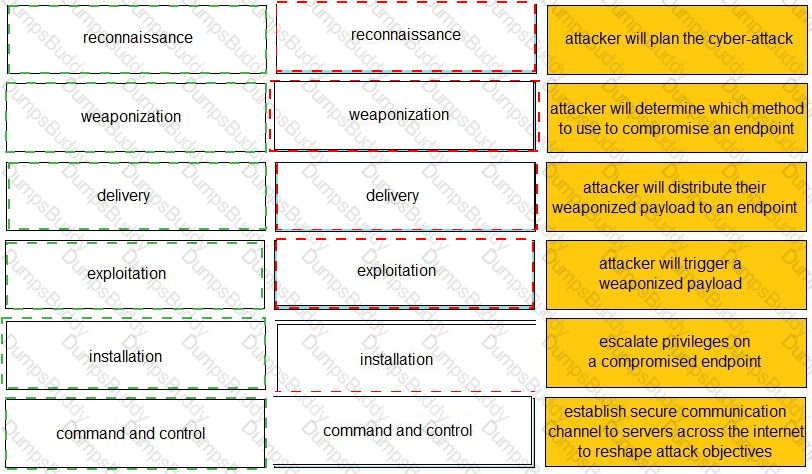
Given the graphic, match each stage of the cyber-attack lifecycle to its description.


Which SOAR feature coordinates across technologies, security teams, and external users for centralized data visibility and action?
In an IDS/IPS, which type of alarm occurs when legitimate traffic is improperly identified as malicious traffic?
Which option describes the “selective network security virtualization” phase of incrementally transforming data centers?
What type of DNS record maps an IPV6 address to a domain or subdomain to another hostname?
The customer is responsible only for which type of security when using a SaaS application?
During the OSI layer 3 step of the encapsulation process, what is the Protocol Data Unit (PDU) called when the IP stack adds source (sender) and destination (receiver) IP addresses?
Which protocol is used by both internet service providers (ISPs) and network service providers (NSPs)?