NetSec-Analyst Palo Alto Networks Network Security Analyst Questions and Answers
An analyst needs to create a security rule to allow access to a specific web application that identifies itself as "web-browsing" but uses a custom, non-standard port of TCP 9000. Which configuration ensures the App-ID engine can still inspect this traffic?
In Strata Cloud Manager (SCM), which logical container is used to group firewalls that share the same configuration requirements, such as those at a specific regional office?
What is the most granular method for ensuring that traffic to a firewall’s public IP address on the public interface is translated to the private IP address of the web server?
A firewall administrator is creating an application override rule to bypass Layer 7 inspection for a pre-defined application. What is the expected behavior for Content-ID checks for this application?
An analyst is configuring a "WildFire Analysis Profile." Which file types can be sent to the WildFire cloud for sandbox analysis?
Which aspect of a network’s current health does the Strata Cloud Manager (SCM) Device Health dashboard provide?
An analyst wants to allow users to visit "Social Networking" sites but prevent them from posting comments or uploading files. Which combination of Security Profile and Action is required?
When pushing a configuration from Panorama to multiple firewalls, an analyst wants to ensure that a specific local interface setting on one firewall is not overwritten by the template value. Which feature should be used?
When using Strata Cloud Manager (SCM), which tool allows an analyst to automatically migrate local firewall configurations to a centralized management folder?
Which log type should be checked first using Log Viewer when a user reports being unable to access a specific website?
An analyst wants to create a custom application for an internal tool that uses a specific proprietary protocol. Which information is required to ensure the firewall correctly identifies this application using App-ID?
A Palo Alto Networks NGFW for a high-security environment is being configured and requires a security profile group that includes vulnerability protection. When configuring the action based on the severity of the threat types, what does Palo Alto Networks recommend? (Choose one answer)
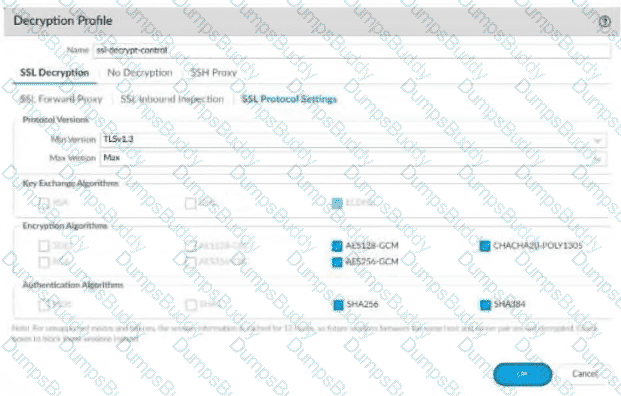
An organization wants to decrypt outbound traffic to ensure no malware is hidden in HTTPS sessions. Which type of decryption policy must be configured on the firewall to act as a "Man-in-the-Middle"?
An analyst notices an unusual amount of bandwidth being consumed by "web-browsing" traffic. Which ACC tab provides a breakdown of which specific URLs and URL Categories are responsible for this bandwidth usage?
An analyst is investigating why an App-ID for a custom application is showing as "unknown-tcp" in the Traffic logs. The application is running on port 8080. What is the most likely cause of this identification failure?
A security administrator needs to block access to a specific list of 500 malicious domains. These domains are updated daily by a third-party intelligence feed. What is the most efficient way to manage these domains as an object?
A user reports that they can reach a website, but the page elements are not loading correctly. The analyst suspects that a security profile is silently dropping some of the web content. Which log, when filtered by the user's IP, will show the specific Content-ID match that is causing the partial page failure?
Which type of object should be used to ensure that a Security policy rule automatically updates when a new virtual machine is spun up in a public cloud environment and assigned a specific tag?