IIA-CIA-Part3 Internal Audit Function Questions and Answers
Which of the following actions should an internal auditor take to clean the data obtained for analytics purposes?
A rapidly expanding retail organization continues to be tightly controlled by its original small management team. Which of the following is a potential risk in this vertically centralized organization?
Which of the following attributes of data are cybersecurity controls primarily designed to protect?
Which of the following network types should an organization choose if it wants to allow access only to its own personnel?
An internal auditor is reviewing key phases of a software development project. Which of the following would; the auditor most likely use to measure the project team's performance related to how project tasks are completed?
The board is considering outsourcing the internal audit function to an external service provider. Which of the following would always remain the responsibility of the organization?
To achieve conformance with the Global Internal Audit Standards, the chief audit executive must include which of the following activities in the quality assurance and improvement program (QAIP)?
Which of the following IT disaster recovery plans includes a remote site dessgnated for recovery with available space for basic services, such as internet and
telecommunications, but does not have servers or infrastructure equipment?
Management is pondering the following question:
"How does our organization compete?"
This question pertains to which of the following levels of strategy?
At one organization, the specific terms of a contract require both the promisor end promise to sign the contract in the presence of an independent witness.
What is the primary role to the witness to these signatures?
What relationship exists between decentralization and the degree, importance, and range of lower-level decision making?
Which of the following controls would enable management to receive timely feedback and help mitigate unforeseen risks?
According to 11A guidance on IT, which of the following are indicators of poor change management?
1. Inadequate control design.
2. Unplanned downtime.
3. Excessive troubleshooting .
4. Unavailability of critical services.
Which of the following IT professionals is responsible for providing maintenance to switches and routers to keep IT systems running as intended?
The board of directors wants to implement an incentive program for senior management that is specifically tied to the long-term health of the organization. Which of the following methods of compensation would be best to achieve this goal?
A manufacturer ss deciding whether to sell or process materials further. Which of the following costs would be relevant to this decision?
An internal audit uncovered high-risk issues that needed to be addressed by the organization. During the exit conference, the audit team discussed the high-risk issues with the manager responsible for addressing them. How should the chief audit executive respond if the manager agrees to correct the issues identified during the audit?
An organization with a stable rating, as assessed by International rating agencies, has issued a bond not backed by assets or collateral. Payments of the interests and the principal to bondholders are guaranteed by the organization. Which type of bond did the organization issue?
Which of the following contract concepts is typically given in exchange for the execution of a promise?
An internal auditor is assessing the risks related to an organization’s mobile device policy. She notes that the organization allows third parties (vendors and visitors) to use outside smart devices to access its proprietary networks and systems. Which of the following types of smart device risks should the internal auditor be most concerned about?
Which of the following business practices promotes a culture of high performance?
Which of the following statements is true regarding user-developed applications (UDAs)?
A new manager received computations of the internal rate of return regarding his project proposal. What should the manager compare the computation results to in order to determine whether the project is potentially acceptable?
Which of the following statements. Is most accurate concerning the management and audit of a web server?
According to 11A guidance on it; which of the following statements is true regarding websites used in e-commerce transactions?
An internal auditor is assessing the risks related to an organization's mobile device policy. She notes that the organization allows third parties (vendors and visitors) to use outside smart devices to access its proprietary networks and systems. Which of the following types of smart device risks should the internal
Auditor be most concerned about?
Which of the following controls would be the most effective in preventing the disclosure of an organization's confidential electronic information?
A company produces water buckets with the following costs per bucket:
Direct labor = 82
Direct material = $5
Fixed manufacturing = 83.50
Variable manufacturing = 82.50
The water buckets are usually sold for $15. However, the company received a special order for 50.000 water buckets at 311 each.
Assuming there is adequate manufacturing capacity and ail other variables are constant , what is the relevant cost per unit to consider when deciding whether to accept this special order at the reduced price?
An organization has instituted a bring-your-own-device (BYOD) work environment. Which of the following policies best addresses the increased risk to the organization’s network incurred by this environment?
When preparing the annual internal audit plan, which of the following should the chief audit executive (CAE) consider to optimize efficiency and effectiveness?
The internal audit function for a large organization has commenced this year’s scheduled accounts payable audit. The annual external audit for the organization is currently being planned. Can the external auditors place reliance on the work performed by the internal audit function?
A chief audit executive wants to implement an enterprisewide resource planning software. Which of the following internal audit assessments could provide overall assurance on the likelihood of the software implementation's success?
The internal audit function conducted an engagement on maintenance operations of a construction organization and identified several issues of medium importance. The head of maintenance proposed an improvement plan with deadlines and personnel responsible. The internal audit function issued the final report to senior management. Senior management was dissatisfied with the report as they believed that improvement plan deadlines should be considerably shorter. Which of the following should the internal audit function change in the reporting process?
An organization that soils products to a foreign subsidiary wants to charge a price that wilt decrease import tariffs. Which of the following is the best course of action for the organization?
An organization produces products X and Y. The materials used for the production of both products are limited to 500 Kilograms
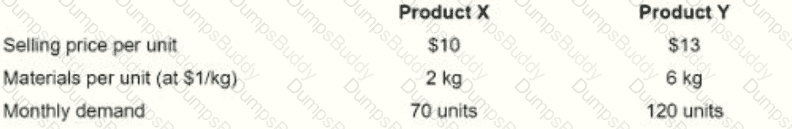
(kg ) per month. All other resources are unlimited and their costs are fixed. Individual product details are as follows in order to maximize profit, how much of product Y should the organization produce each month?
$10 $13
2 kg
70 units
6 kg
120 units
According to Herzberg's Two-Factor Theory of Motivation, which of the following factors arc mentioned most often by satisfied employees?
An internal auditor was assigned to test for ghost employees using data analytics. The auditor extracted employee data from human resources and payroll. Using spreadsheet functions, the auditor matched data sets by name and assumed that employees who were not present in each data set should be investigated further. However, the results seemed erroneous, as very few employees matched across all data sets. Which of the following data analytics steps has the auditor most likely omitted?
Which of the following describes how human resources can best assist in recruitment efforts for the internal audit function?
Which of the following purchasing scenarios would gain the greatest benefit from implementing electronic data interchange (EDI)?
Which of the following is on example of a smart device security control intended to prevent unauthorized users from gaining access to a device's data or applications?
Upon completing a follow-up audit engagement, the chief audit executive (CAE) noted that management has not implemented any mitigation measures to address the high risks that were reported in the initial audit report. What initial step must the CAE take to address this situation?
Focus An organization has decided to have all employees work from home. Which of the following network types would securely enable this approach?
Which of the following key performance indicators would serve as the best measurement of internal audit innovation?
A manager at a publishing company received an email that appeared to be from one of her vendors with an attachment that contained malware embedded in an Excel spreadsheet . When the spreadsheet was opened, the cybercriminal was able to attack the company's network and gain access to an unpublished and highly anticipated book. Which of the following controls would be most effective to prevent such an attack?
An intruder posing as the organization's CEO sent an email and tricked payroll staff into providing employees' private tax information. What type of attack was perpetrated?
Which of the following is the most appropriate way lo record each partner's initial Investment in a partnership?
An organization has a declining inventory turnover but an Increasing gross margin rate, Which of the following statements can best explain this situation?
A small chain of grocery stores made a reporting error and understated its ending inventory. What effect would this have on the income statement for the following year?
Which of the following Issues would be a major concern for internal auditors when using a free software to analyze a third-party vendor's big data?
What is the primary risk associated with an organization adopting a decentralized structure?
Which statement is true regarding the development of a risk-based internal audit plan?
Which of the following is a primary driver behind the creation and prloritteation of new strategic Initiatives established by an organization?
Which of the following is classified as a product cost using the variable costing method?
Direct labor costs.
Insurance on a factory.
Manufacturing supplies.
Packaging and shipping costs.
At one organization, the specific terms of a contract require both the promisor and promisee to sign the contract in the presence of an independent witness. What is the primary role to the witness to these signatures?
A bond that matures after one year has a face value of S250,000 and a coupon of $30,000. if the market price of the bond is 5265,000, which of the following would be the market interest rate?
Which of the following risks would involve individuals attacking an oil company’s IT system as a sign of solidarity against drilling in a local area?
A chief audit executive (CAE) joined an organization in the middle of the financial year. A risk-based annual audit plan has been approved by the board and is already underway. However, after discussions with key stakeholders, the CAE realizes that some significant key risk areas have not been covered in the original audit plan. How should the CAE respond?
Which of the following is a cybersecurity monitoring activity intended to deter disruptive codes from being installed on an organizations systems?
An organization is considering outsourcing its IT services, and the internal auditor as assessing the related risks. The auditor grouped the related risks into three categories;
- Risks specific to the organization itself.
- Risks specific to the service provider.
- Risks shared by both the organization and the service provider
Which of the following risks should the auditor classify as specific to the service provider?
An organization created a formalized plan for a large project. Which of the following should be the first step in the project management plan?
Which of the following scenarios would cause a chief audit executive (CAE) to immediately discontinue using any statements that would indicate conformance with the Global Internal Audit Standards in an audit report?
Which of the following should software auditors do when reporting internal audit findings related to enterprisewide resource planning?
During which phase of the contracting process ere contracts drafted for a proposed business activity?
Which of the following is on advantage of a decentralized organizational structure, as opposed to a centralized structure?
Which of the following practices circumvents administrative restrictions on smart devices, thereby increasing data security risks?
Which of the following describes the most appropriate set of tests for auditing a workstation's logical access controls?
When management uses the absorption costing approach, fixed manufacturing overhead costs are classified as which of the following types of costs?
Which of the following statements is true regarding user developed applications (UDAs) and traditional IT applications?
Which of the following is true regarding reporting on the quality assurance and improvement program (QAIP)?
At what stage of project integration management would a project manager and project management team typically coordinate the various technical and organizational interfaces that exist in the project?
During a routine bank branch audit, the internal audit function observed that the sole security guard at the branch only worked part time. The chief audit executive (CAE) believed that this increased the risk of loss of property and life in the event of a robbery. The branch security manager informed the CAE that a full-time guard was not needed because the branch was in close proximity to a police station. Still, the CAE found this to be an unacceptable risk due to the recent increase in robberies in that area. Which of the following is the most appropriate next step for the CAE to take?
In accounting, which of the following statements is true regarding the terms debit and credit?
According to IIA guidance, which of the following statements is true regarding analytical procedures?
Which of the following security controls would be me most effective in preventing security breaches?
According to lIA guidance on IT, which of the following plans would pair the identification of critical business processes with recovery time objectives?
Which of the following is a security feature that involves the use of hardware and software to filter or prevent specific information from moving between the inside network and the outside network?
Which of the following cost of capital methods identifies the time period required to recover She cost of the capital investment from the annual inflow produced?
Which of the following differentiates a physical access control from a logical access control?
An organization upgraded to a new accounting software. Which of the following activities should be performed by the IT software vendor immediately following the upgrade?
A multinational organization allows its employees to access work email via personal smart devices. However, users are required to consent to the installation of mobile device management (MDM) software that will remotely wipe data in case of theft or other incidents. Which of the following should the organization ensure in exchange for the employees' consent?
A significant project is nearing its development stage end, and line management intends to apply for a final investment decision from senior management at an upcoming meeting. The internal audit function is at the fieldwork stage of an assurance engagement related to this project and discovers that tenders conducted for the project were not carried out transparently by line management. The audit report will not be ready by the upcoming senior management meeting. Which of the following actions is the most appropriate next step for the chief audit executive?
The internal auditor concluded there was a high likelihood that a significant wind farm development, worth $200 million, would be delayed from its approved schedule. As a result, electricity production would not start on time, leading to considerable financial penalties. Which of the following should be added to the observation to support its clarity and completeness?
If an organization has a high amount of working capital compared to the industry average, which of the following is most likely true?
Which of the following can be viewed as a potential benefit of an enterprisewide resource planning system?
According to IIA guidance, which of the following links computers and enables them to -communicate with each other?
Which of the following statements is true regarding the term "flexible budgets" as it is used in accounting?
An organization had a gross profit margin of 40 percent in year one and in year two. The net profit margin was 18 percent in year one and 13 percent in year two. Which of the following could be the reason for the decline in the net profit margin for year two?
According to IIA guidance on IT, which of the following strategies would provide the most effective access control over an automated point-of-sale system?
What kind of strategy would be most effective for an organization to adopt in order to implement a unique advertising campaign for selling identical products across all of its markets?
Which of the following best describes the purpose of fixed manufacturing costs?
Based on test results, an IT auditor concluded that the organization would suffer unacceptable loss of data if there was a disaster at its data center. Which of the following test results would likely lead the auditor to this conclusion?
An internal auditor is using data analytics to focus on high-risk areas during an engagement. The auditor has obtained data and is working to eliminate redundancies in the data. Which of the following statements is true regarding this scenario?
Which of the following parties is most likely to be responsible for maintaining the infrastructure required to prevent the failure of a real-time backup of a database?
An organization has 10,000 units of a defect item in stock, per unit, market price is $10$; production cost is $4; and defect selling price is $5. What is the carrying amount (inventory value) of defects at your end?
An internal auditor is assigned to perform data analytics. Which of the following is the next step the auditor should undertake after she has ascertained the value expected from the review?
The finance department of an organization recently undertook an asset verification exercise. The internal audit function scheduled a review of the IT department’s operations, which includes verifying the existence of computers distributed and their assignment. Can the internal audit function consider relying on the asset verification work performed by the finance department?
Which of the following situations best applies to an organisation that uses a project, rather than a process, to accomplish its business activities?
Senior management of a dairy organization asks the internal audit function to undertake an advisory service within the finance function and the internal audit function subsequently issues a report. Which of the following is aligned with IIA guidance on monitoring the results of such an engagement?
Which of the following best describes a cyberattacK in which an organization faces a denial-of-service threat created through malicious data encryption?
Which of the following authentication controls combines what a user knows with the unique characteristics of the user, respectively?
Which of the following items represents a limitation with an impact the chief audit executive should report to the board?
Which of these instances accurately describes the responsibilities for big data governance?
Which of the following is the most appropriate beginning step of a work program for an assurance engagement involving smart devices?
The budgeted cost of work performed is a metric best used to measure which project management activity?
Which of the following should internal auditors be attentive of when reviewing personal data consent and opt-in/opt-out management process?
During an audit of the payroll system, the internal auditor identifies and documents the following condition:
"Once a user is logged into the system, the user has access to all functionality within the system."
What is the most likely root cause for tins issue?
Which of the following is a necessary action for an internal audit function if senior management chooses not to take action to remediate the finding and accepts the risk?
Which of the following would most likely serve as a foundation for individual operational goats?
Which of the following application controls is the most dependent on the password owner?
Which of the following information security controls has the primary function of preventing unauthorized outside users from accessing an organization's data through the organization's network?
Which of the following data privacy concerns can be attributed specifically to blockchain technologies?
Which of the following controls would an internal auditor consider the most relevant to reduce risks of project cost overruns?
Management is designing its disaster recovery plan. In the event that there is significant damage to the organization's IT systems this plan should enable the organization to resume operations at a recovery site after some configuration and data restoration. Which of the following is the ideal solution for management in this scenario?
Which of the following statements is true regarding cost-volume-profit analysis?
An organization with global headquarters in the United States has subsidiaries in eight other nations. If the organization operates with an ethnocentric attitude, which of the following statements is true?
Which of the following security controls would be appropriate to protect the exchange of information?
Which of the following techniques would best detect an inventory fraud scheme?
When using data analytics during a review of the procurement process, what is the first step in the analysis process?
Which of the following purchasing scenarios would gain the greatest benefit from implementing electronic cate interchange?
In an organization that produces chocolate, the leadership team decides that the organization will open a milk production facility for its milk chocolate. Which of the following strategies have the organization chosen?
Which of the following describes a third-party network that connects an organization specifically with its trading partners?
Which of the following actions is likely to reduce the risk of violating transfer pricing regulations?
Management decides to accept the risk on a significant audit observation related to the organization's exposure to fraud risk. The chief audit executive considers the finding to have a high residual risk. Which of the following steps should be performed last?
Employees of an organization noticed that an exterior surface of the office building was deteriorating. Upon investigation, it was found that the deterioration was caused by harsh cleaning chemicals used to remove excessive bird droppings, and that the birds were drawn to the building to feed from a spider infestation. Which of the following best represents a root cause-based recommendation for this situation?
An organization's technician was granted a role that enables him to prioritize projects throughout the organization. Which type of authority will the technician most likely be exercising?
When auditing the account receivables for the first time, an internal auditor noted that the finance team had not—over many accounting periods—reviewed the accounts receivables for debts that could no longer be collected. How should the auditor proceed?
Which of the following inventory costing methods requires the organization to account for the actual cost paid for the unit being sold?
Which of the following situations best illustrates a "false positive" in the performance of a spam filter?
An employee was promoted within the organization and relocated to a new office in a different building. A few months later, security personnel discovered that the employee's smart card was being used to access the building where she previously worked. Which of the following security controls could prevent such an incident from occurring?
Which of the following organization structures would most likely be able to cope with rapid changes and uncertainties?
During a review of the accounts payable process, an internal auditor gathered all of the vendor payment transactions for the past 24 months. The auditor then used an Analytics tool to identify the top five vendors that received the highest sum of payments. Which of the following analytics techniques did the auditor apply?
As it relates to the data analytics process, which of the following best describes the purpose of an internal auditor who cleaned and normalized data?
An investor has acquired an organization that has a dominant position in a mature, slow-growth industry and consistently creates positive financial income. Which of the following terms would the investor most likely label this investment in her portfolio?
Which of the following is a disadvantage in a centralized organizational structure?
A new manager received computations of the internal fate of return regarding the project proposal. What should the manager compare the computation results to in order to determine whether the project is potentially acceptable?
An internal audit function has commenced its annual follow-up activity. An internal auditor has been assigned to verify whether the recommendations from an audit engagement completed three months ago were implemented by the business unit. The auditor had not participated in that audit engagement. What should the auditor do first?


