H12-811_V2.0 HCIA-Datacom V2.0 Questions and Answers
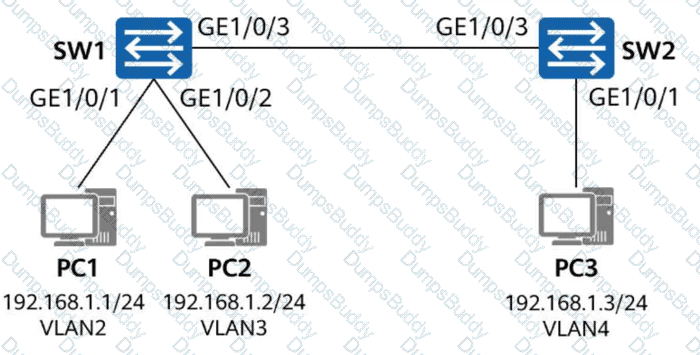
On the network shown in the figure, GE1/0/1 and GE1/0/2 of SW1 are access interfaces, and their PVIDs are VLAN 2 and VLAN 3 respectively. GE1/0/1 of SW2 is also an access interface, and its PVID is VLAN 4. Which of the following configurations on SW1 and SW2 can ensure that data packets sent from PC1 and PC2 can reach PC3?
The domain to which a user belongs is determined by the user name used by the user to log in to the NAS device. If the domain name carried in the user name is not configured on the NAS device, the authentication fails.
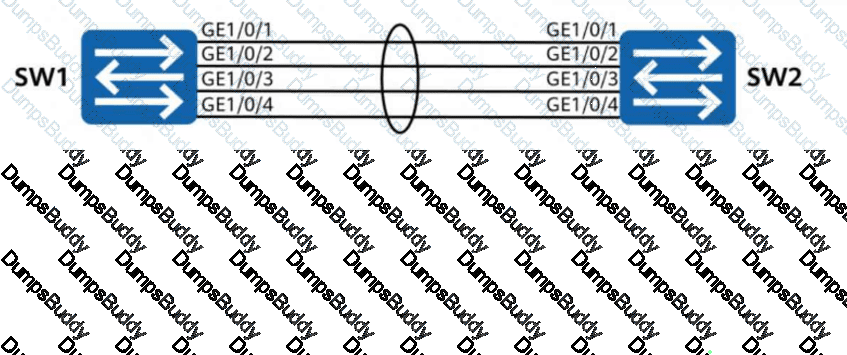
Four links between two switches establish an Eth-Trunk in manual mode, and the bandwidth of each link is 1 Gbit/s. One of the links fails. Which of the following statements are true about this scenario? (Select all that apply)
R1 has the following configurations:
[R1] nat address-group test 1
[R1-address-group-test] section 1 100.1.23.1 100.1.23.254
[R1-address-group-test] mode pat
[R1-address-group-test] quit
[R1] nat-policy
[R1-policy-nat] rule name test
[R1-policy-nat-rule-test] source-address range 192.168.0.0 192.168.255.255
[R1-policy-nat-rule-test] action source-nat address-group test
[R1-policy-nat-rule-test] quit
[R1-policy-nat] quit
[R1] interface GE 0/0/2
[R1-GE0/0/2] nat enable
[R1-GE0/0/2] quit
Which of the following statements is false ?
With the development of data centers, a large number of services are deployed on virtual machines (VMs). The original VLAN isolation solution cannot achieve isolation between so many VMs. VXLAN uses VXLAN Network Identifiers (VNIs) to provide a larger range than VLAN IDs, so that a larger number of VMs can be isolated.
In TCP/IP-based end-to-end communication, only the source and destination hosts process the header information added at the transport layer. Routers along the path will definitely not process this information.
If the neighbor relationship between R1 and R2 has reached the Full state in OSPF, which of the following statements are true? (Select all that apply)
The figure shows the simplified topology of an enterprise campus network. On this network, the aging time of dynamic MAC address entries on switches is 300 seconds.
The administrator connects PC1 to GE1/0/1 of SW1 and successfully pings the IP address of PC2 from PC1. Then, the administrator disconnects the Ethernet cable of PC1
from GE1/0/1 of SW1, immediately connects the cable to GE1/0/2 of SW1, and pings the IP address of PC2 from PC1. Which of the following operations does SW1
perform after receiving a data frame from PC1 when PC1 is connected to GE1/0/2 of SW1?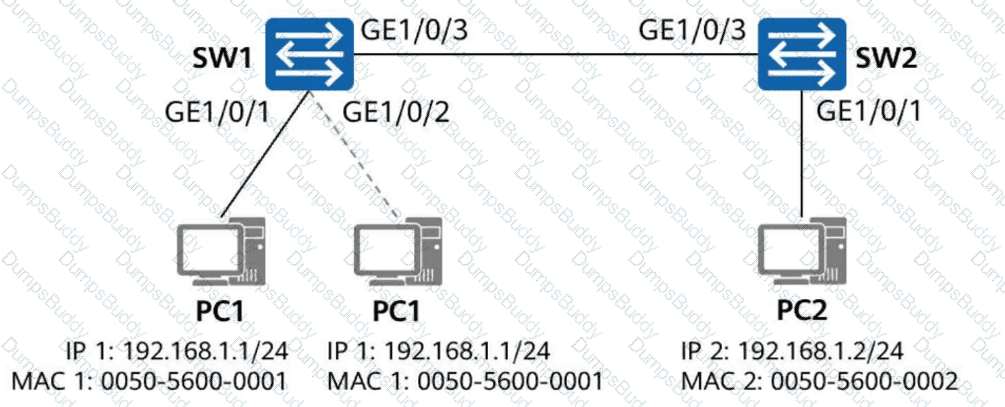
After the root bridge is elected on an STP network, which of the following parameters may be compared by ports on non-root bridge nodes to elect the root port? (Select all that apply)
During VLAN planning for a campus network, VLAN IDs for different service types must be allocated consecutively, without redundancy, to prevent omissions in future allocations.
On an STP network, an administrator wants SW2 to be elected as the root bridge. Which of the following methods can be used to achieve this goal?
What is the broadcast address of the network that contains a host with IP address 192.168.1.147/28?
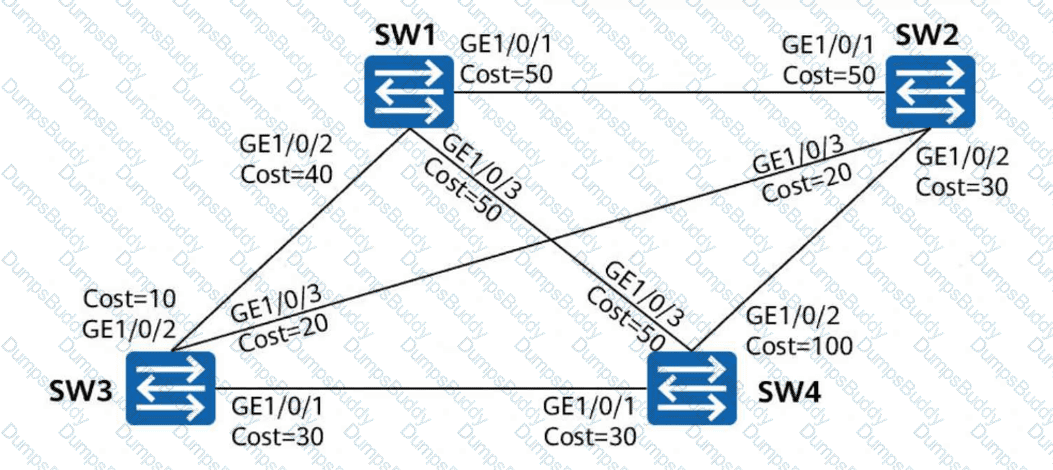
On the switched network shown in the figure, STP is enabled on all devices. SW1 is the root bridge. The port costs are shown in the figure. Other parameters retain the default values. After the network is stable, which of the following paths is used by SW1 to send traffic to SW4?
PC1 and PC2 are connected to the same switch, but they cannot learn each other’s ARP information. This may be caused by incorrect VLAN configuration on the switch.
DAD enables a node to detect whether an IPv6 address is already in use by another node before assigning it to an interface. This ensures that duplicate unicast addresses do not exist on a network. Which of the following packets are used for DAD? (Select all that apply)


