H12-891_V1.0 HCIE-Datacom V1.0 Questions and Answers
In a BGP/MPLS IP VPN scenario, if a PE and CE use OSPF to exchange routing information, domain IDs are used to identify whether the routes imported to VPN instances are from the same OSPF domain.
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, run the command on the VTEP to view BGP EVPN routes. The route entries shown in the following figure are displayed. Which of the following statements about these routing entries are correct?
Network (EthTagId/IP Prefix/IP PrefixLen)
NextHop
* > i 0:172.16.2.0:24 1.1.1.2
* > i 0:172.16.13.0:24 1.1.1.2
* > i 0:192.168.122.0:30 1.1.1.2
IPsec SAs can be established in either manual mode or IKE auto-negotiation mode. Which of the following statements about the two modes is incorrect?
Which of the following operations is not involved in the middle phase of a migration?
Which of the following statements is incorrect about the user authentication points on the network?
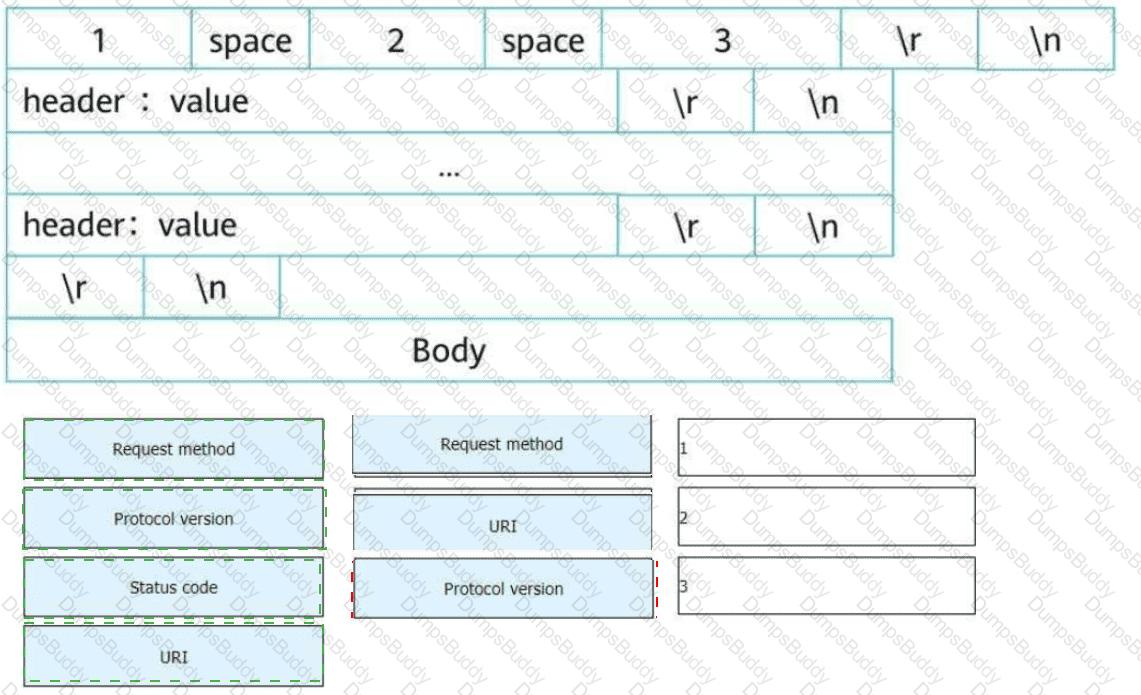
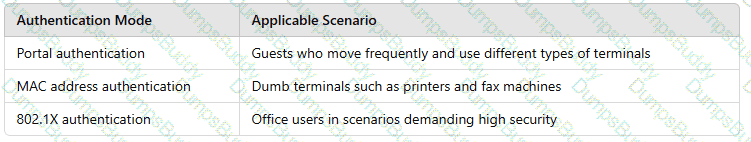
An HTTP request line consists of three fields. Select the fields to form a complete HTTP request message.
By default, the domain ID of an OSPF process is the same as the process ID. You can run the domain-id command in the OSPF process view to change a domain ID.
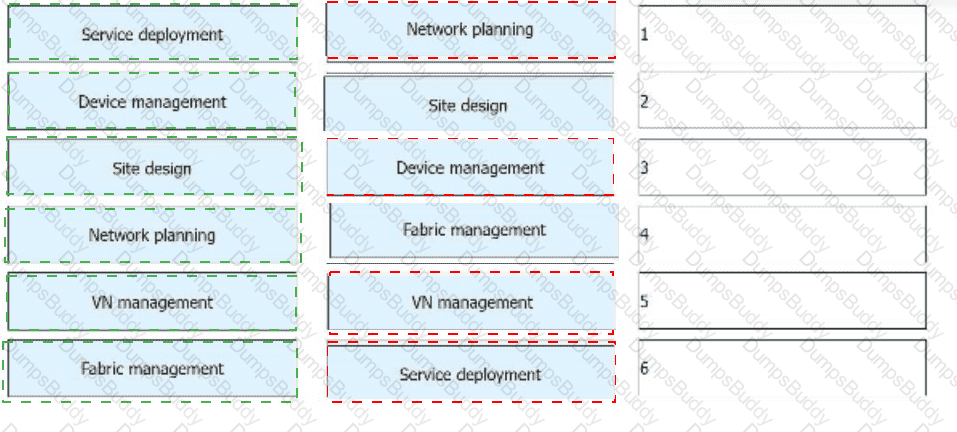
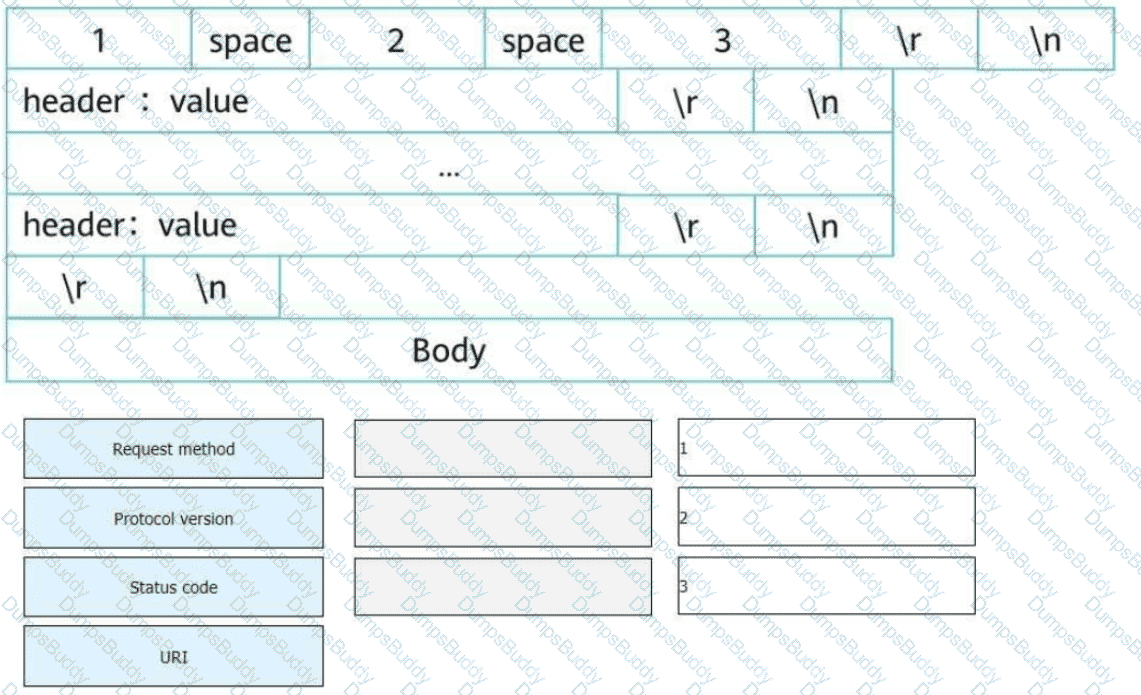
To deploy a virtual campus network using iMaster NCE-Campus, the following steps are performed. From top to bottom, sort the steps in the order in which they occur during network deployment and management.
In the firewall hot standby scenario, in which of the following conditions will the local device proactively send VGMP packets?
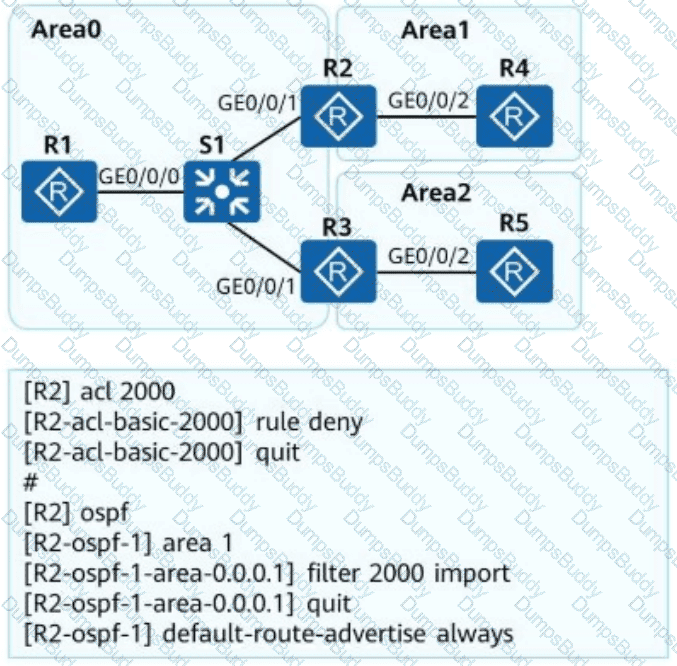
OSPF is deployed on a campus network to implement network interconnection. An engineer configures R2 as shown in the figure. Which of the following statements is incorrect about LSAs on the OSPF network?
When an SSH client logs in to an SSH server that is configured only with username and password authentication in SSH mode, the key exchange phase is not involved (no key is generated).
IPsec uses an asymmetric encryption algorithm to encrypt the symmetric algorithm key, which it uses to encrypt/decrypt data, ensuring security and performance.
iMaster NCE-CampusInsight uses SNMP technology to collect metrics and logs of network devices and detects network exceptions based on real service traffic.
Which of the following factors does not need to be considered during the selection of core devices for the enterprise bearer WAN?
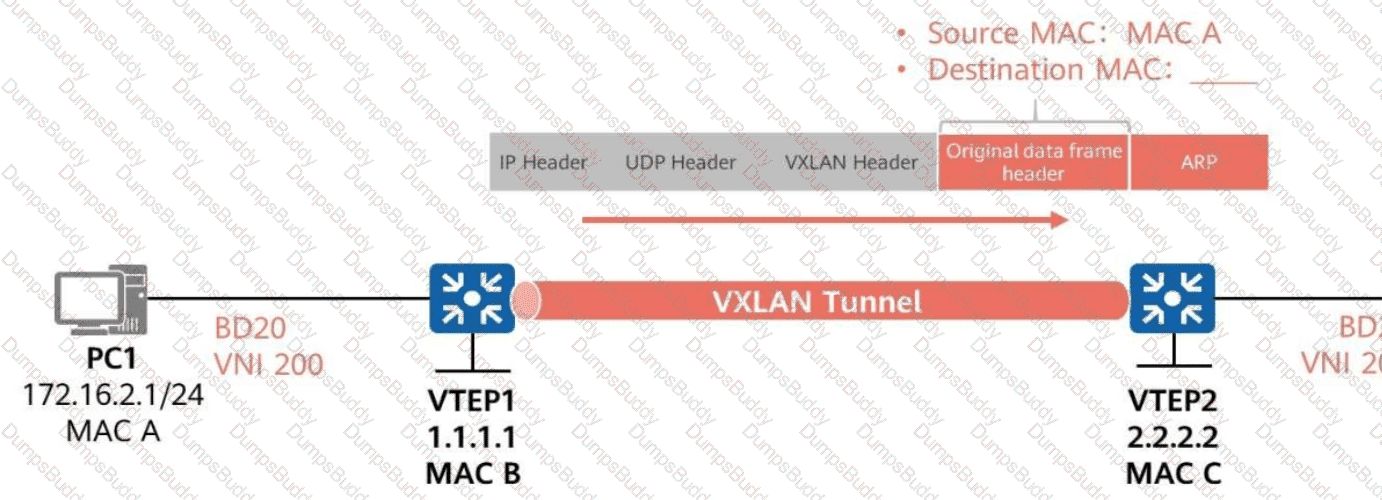
As shown in the figure, ARP broadcast suppression is enabled on VTEP1 in BD 20 (VNI 200).
VTEP1 learns ARP information about PC2 through BGP EVPN routes.
When VTEP1 forwards the ARP request for PC1’s MAC address to VTEP2,
What is the destination MAC address of the inner data frame?
Which of the following is the default port used by iMaster NCE-Campus northbound open APIs?
YANG is a data modeling language for the definition of data sent over network management protocols such as NETCONF. Which of the following are basic YANG data models? (Select all that Apply)
When static IPsec VPN is used for WAN interconnection in the Huawei CloudCampus Solution, the AP, Router, and ____ can be used as egress devices.
Which of the following community attributes ensure that BGP routes are transmitted only within an AS?
Which of the following statements about the multicast address used by OSPFv3 are correct?
Network Quality Analysis (NQA) is a real-time network performance detection and measurement technology. It monitors the performance of multiple protocols running on a network. Which of the following protocols can be monitored by NQA?
In the Huawei CloudCampus Solution, which of the following devices can go online through the registration query center?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following fields is not carried in BGP EVPN Type 2 routes?
The following figure shows the inter-AS MPLS VPN Option B solution. If ASBR-PE1 and ASBR-PE2 only transmit VPNv4 routes, you can run the following command on ASBR-PE1:
[ASBR-PE1-bgp-af-vpnv4] undo peer 10.0.34.4 enable
Which of the following is the drop probability of packets exceeding the upper threshold in WRED?
On a CloudCampus virtualized campus network, virtual networks are defined based on services. Each virtual network corresponds to a service, and isolation needs to be manually configured between virtual networks.
Huawei Open Programmability System (OPS) provides openness and programmability capabilities for network devices and enables users to perform secondary development. To facilitate script completion, Huawei OPS provides the Python script template in which the OPSConnection class is created. The member function for creating device resources is def post(self, uri, req_data).
The naming of SRv6 instructions complies with certain rules. You can quickly determine the function of an instruction based on the instruction name. Which of the following statements about the keywords in SRv6 instruction names are correct? (Select all that apply)
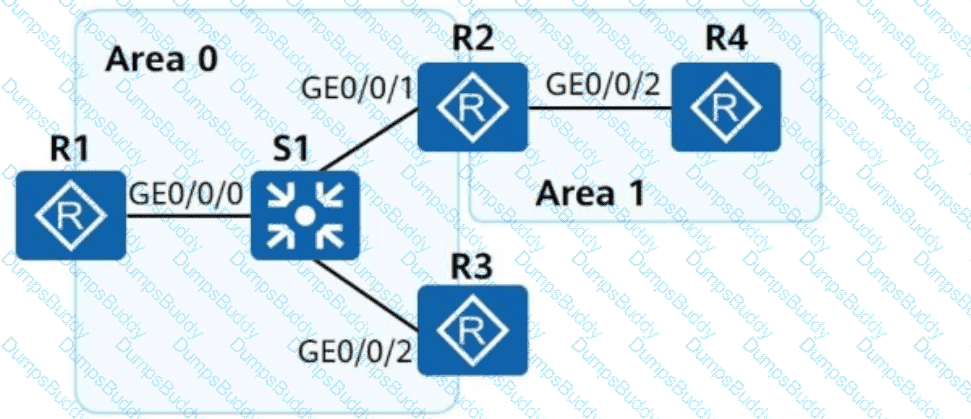
On the campus network shown, IPv6 is deployed for service tests. Four routers are deployed on the network, and these routers use OSPFv3 for network connectivity. Which of the following statements about LSAs generated by the OSPFv3 network is incorrect?
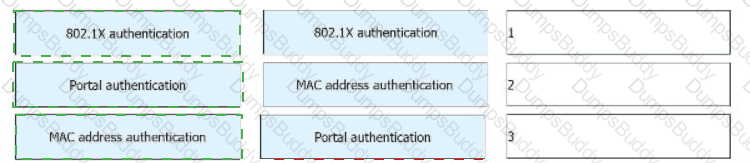
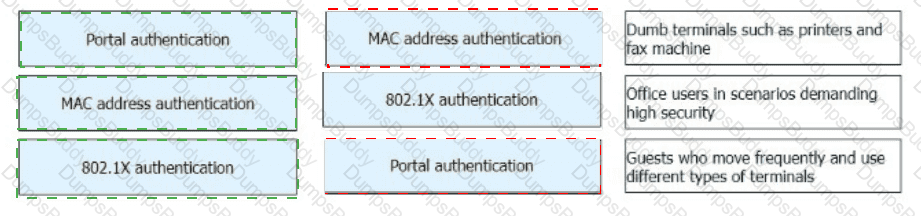
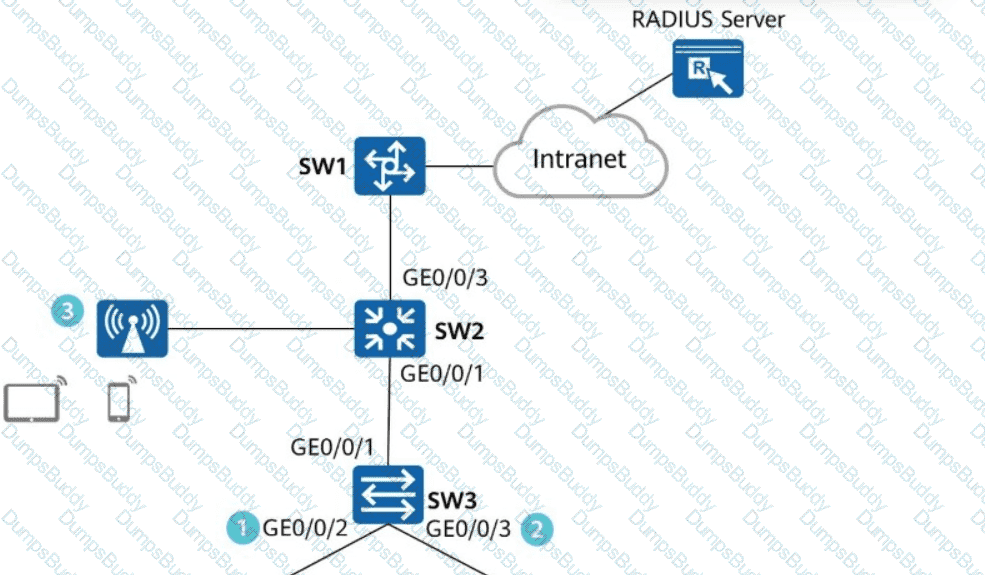
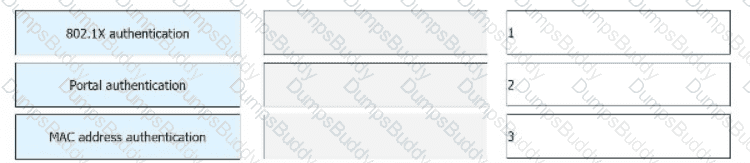
Network Admission Control (NAC) needs to be deployed on the network shown in the figure. Drag a proper authentication mode to each authentication point.
The TTL field encapsulated in the MPLS label header can prevent infinite loops of MPLS packets. Which of the following statements regarding the TTL field are correct?
Which of the following headend behaviors can insert SRHs into IPv6 packets? (Select All that Apply)
BGP routing policies can be used to control the advertisement and acceptance of routes.
As shown in the figure, SW1 and SW2 use asymmetric IRB (Integrated Routing and Bridging) forwarding, and PC1 and PC2 communicate with each other. Which of the following is the destination MAC address of the original data frame in the packet sent from VTEP1 to VTEP2?
Which of the following number sequences can be matched by the regular expression 100.$?
Portal authentication is recommended for scenarios with high mobility and numerous terminal types, such as shopping malls and supermarkets. MAC address authentication is recommended for dumb terminals that do not support Portal authentication, such as printers, fax machines, and IP phones.
During the configuration of L3VPNv4 over SRv6 BE, if an RR is deployed in the SR domain, which command must be run on the RR to ensure that the PEs at both ends can correctly learn VPNv4 routes?
On an SR-MPLS network, manually configured prefix SIDs on different devices may conflict with each other. Assume that there are four routes (prefix/mask SID) as follows. Which of the following routes will be selected according to the conflict handling principle?
As shown in the figure, PE1 establishes an EVPN peer relationship with each of PE2 and PE3. When the network is initialized, CE1 sends an ARP request packet.
Which of the following statements are correct about how a PE processes the packet?
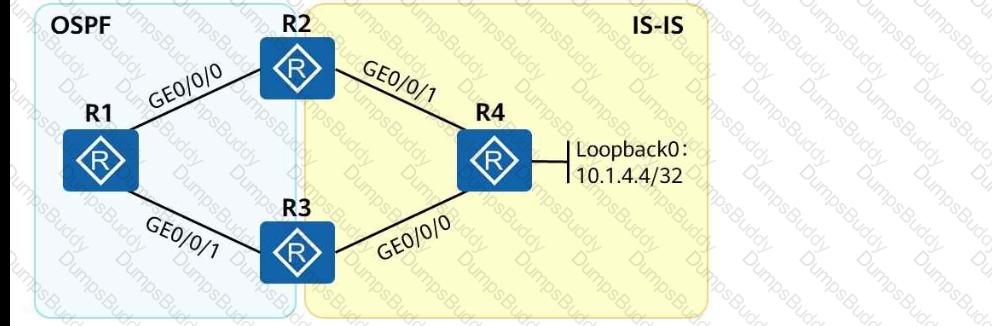
As shown in the following figure, an engineer tests network interconnection between two branches. To implement network interconnection, OSPF is deployed on R1, R2, and R3 of branch 1, and IS-IS is deployed on R2, R3, and R4 of branch 2. Which of the following operations needs to be performed to allow R1 to access R4 ' s loopback interface address?
Flavors can be used to enhance SRv6 instructions to meet more diversified service requirements. Which of the following are flavors? (Select all that apply)
The Ingress VTEP performs both Layer 2 and Layer 3 table lookup for packet forwarding. The forwarding mode is _____ IRB forwarding. (Capitalize the first letter.)
In an MPLS VPN network, two-layer MPLS labels are added into data packets before they are transmitted over the public network. Which of the following statements regarding data packet processing are correct?
Which of the following inter-AS MPLS L3VPN solutions needs ASBRs to transmit VPNv4 routes?
During the implementation of iMaster NCE-Campus Wi-Fi location-based services (LBS), terminal location data is sent to an LBS platform through HTTP requests. Which of the following data formats is used in such HTTP requests?
Refer to the following command output on the router R3. Which of the following statements are correct?
< R3 > display interface Tunnel
Tunnel0/0/0 current state : UP
Line protocol current state : UP
Last line protocol up time : 15:21:26 UTC-08:00
Description: HUAWEI, AR Series, Tunnel0/0/0 Interface
Route Port, The Maximum Transmit Unit is 1500
Internet Address is 20.1.1.2/24
Encapsulation is TUNNEL, loopback not set
Tunnel source 10.0.3.3 (LoopBack0), destination 10.0.1.1
Tunnel protocol/transport GRE/IP, key disabled
keepalive disabled
Checksumming of packets disabled
An SRv6 Policy can be either statically configured on a device, or be delivered to a device after being dynamically generated by the controller.
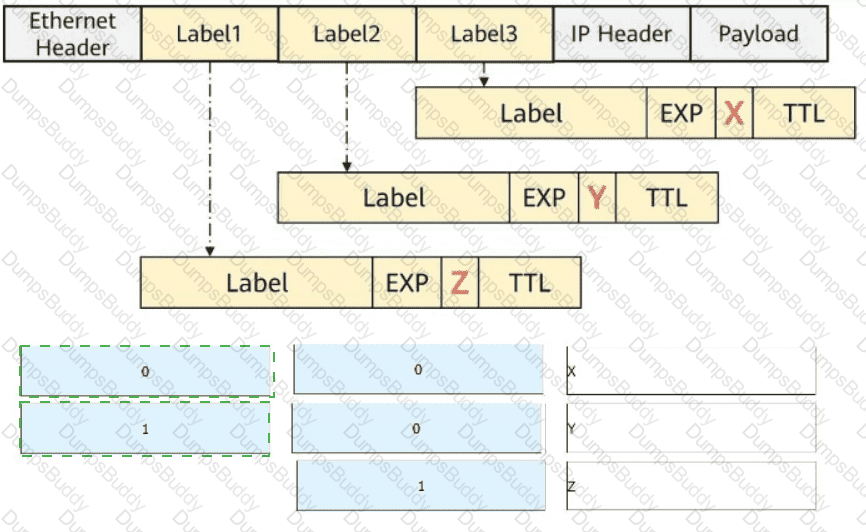
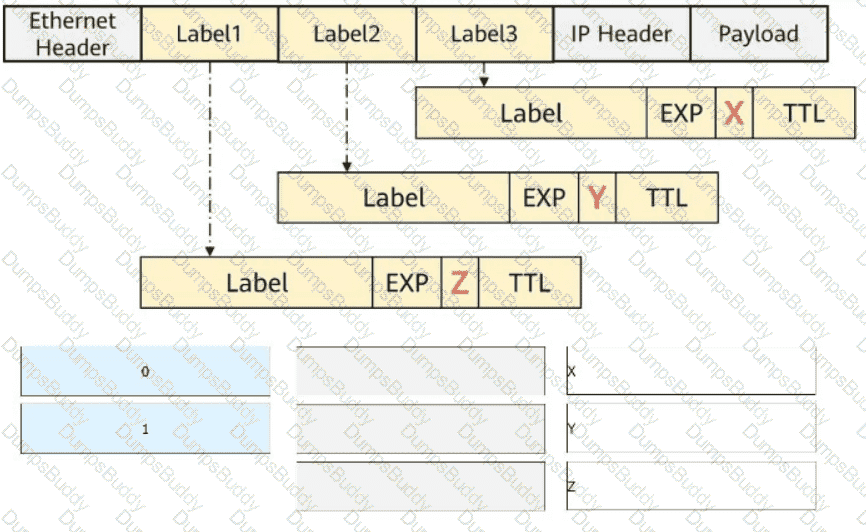
The figure shows a packet that contains three label headers. Select the values (in decimal notation) of the X, Y, and Z fields, respectively.
As shown in the figure, when PE1 receives an ARP request packet, it forwards the packet to PE4. The packet then carries two labels. The label value 201 is carried by the EVPN Type ____ route. (Enter only digits.)
Which of the following commands are mandatory for configuring an OSPF-based SR-MPLS TE tunnel? (Select All that Apply)
Which of the following roles is NOT a core role in Huawei ' s Free Mobility solution?
An Ethernet Segment Identifier (ESI) is 10 bytes long and unique on the entire network.
On a campus network, which of the following problems may occur when you manually create a static VXLAN tunnel?
The path of an SR-MPLS TE tunnel can be calculated by the controller or tunnel ingress.
Which of the following statements about the SP scheduling algorithm is incorrect?
When static IPsec VPN is used for WAN interconnection in the Huawei CloudCampus Solution, the AP, Router, and _____ can be used as egress devices. (Use full spelling with the first letter capitalized.)
In the LDP session establishment process, the initiator sends an Initialization message for parameter negotiation. Which message will be sent by the responder if it does not accept negotiation parameters?
If an engineer wants to remotely log in to a Huawei device, the engineer uses the Paramiko library to compile the following code when compiling the SSH Python script:
cli = ssh.invoke_shell()
cli.send( " screen-length 0 temporary\n " )
What is the function of screen-length 0 temporary?
iMaster NCE-WAN is the core component of the Huawei SD-WAN Solution and is responsible for SD-WAN network management and service orchestration.
In the CloudCampus public cloud scenario, if deployment through the Huawei registration query center is used, you do not need to configure DHCP Option 148 on the DHCP server of the campus network.
An engineer uses two routers to perform IPv6 tests and wants to use OSPFv3 for IPv6 network connectivity. Which of the following OSPFv3 configurations for R1 are correct?
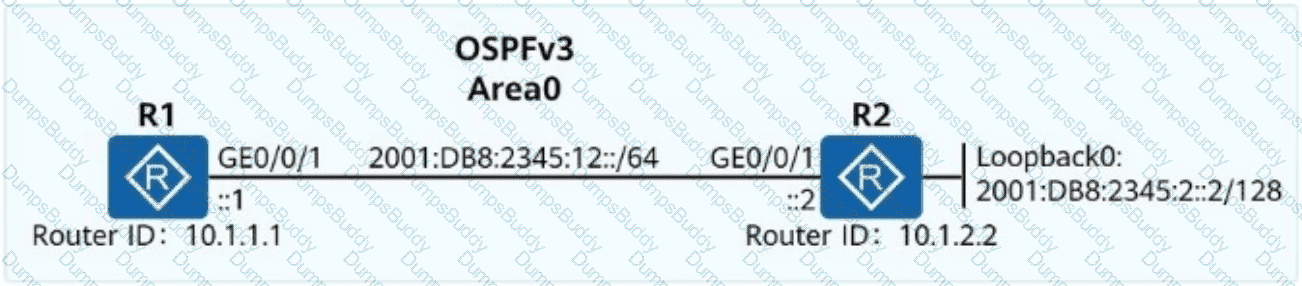
Exhibit:
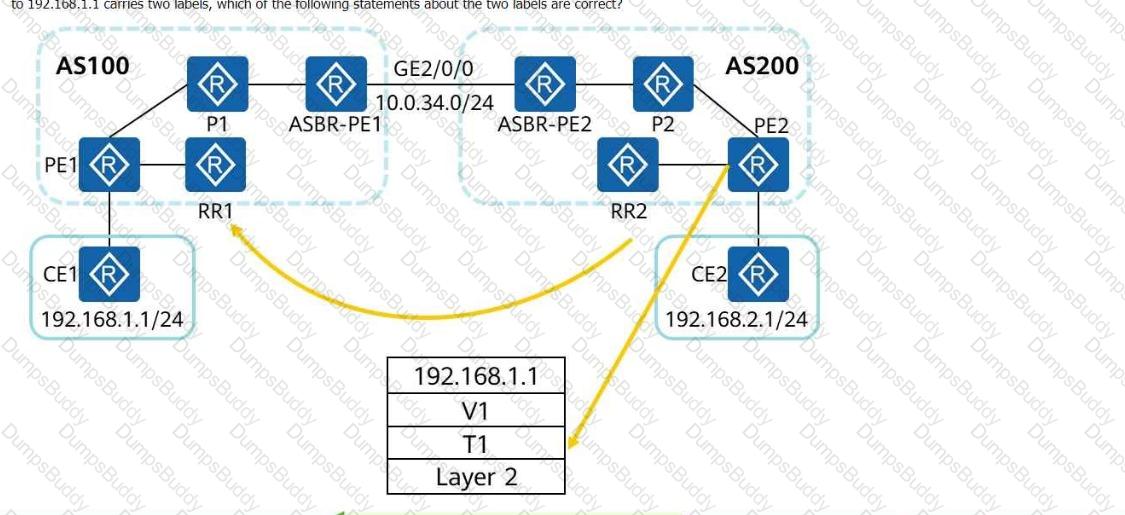
The following figure shows the inter-AS MPLS VPN Option C (solution 2). RRs are deployed, and no traffic passes through the RRs during forwarding. If a data packet sent from PE2 to 192.168.1.1 carries two labels, which of the following statements about the two labels are correct?
Drag the authentication modes on the left into their applicable scenarios on the right.

NETCONF provides a set of mechanisms for managing network devices. NETCONF operations take place on a configuration datastore of network devices. Which of the following statements is incorrect about the configuration datastore?
Telemetry is a technology that remotely collects data from physical or virtual devices at high speed, and has a layered protocol stack. Which of the following layers is not included in the telemetry protocol stack?
When Huawei iMaster NCE-IP is used to configure SR-MPLS TE tunnels, which of the following protocols is used by the controller to collect device running status information?
When you configure a virtualized campus network on iMaster NCE-Campus and enable external networks to connect to the Internet, iMaster NCE-Campus will automatically deliver a specific route to direct traffic to the corresponding external network.
OSPF is deployed on a campus network to implement network interconnection. The LSDB of R2 is shown in the figure.
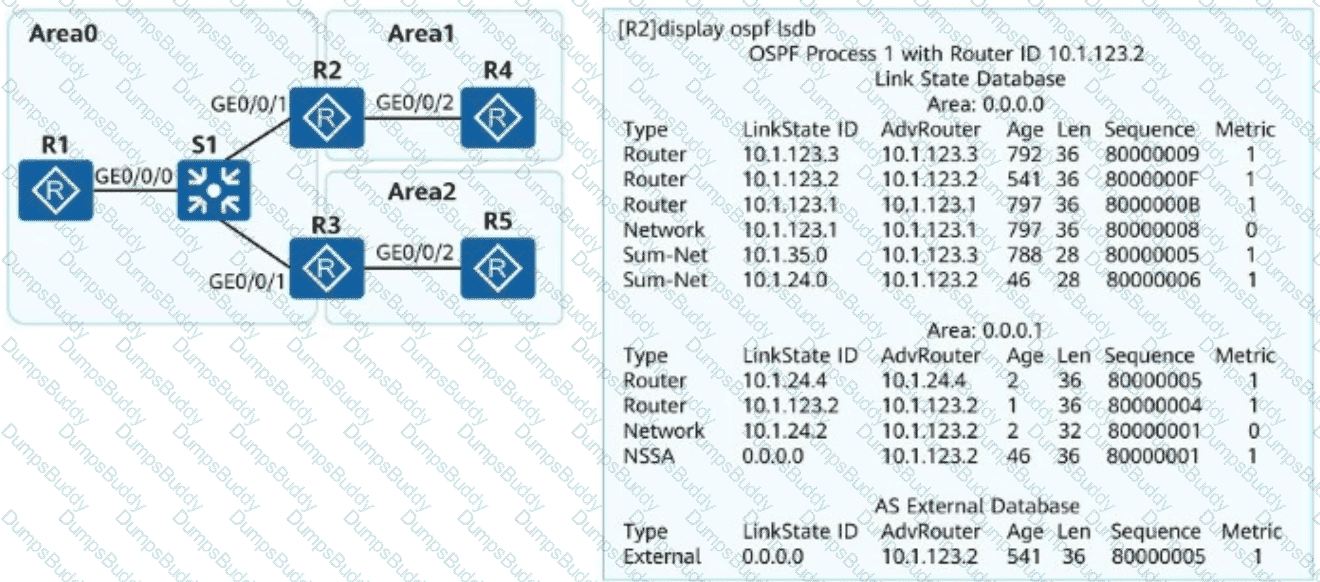
What can be determined from the LSDB?
For telemetry data push, data can be transferred between devices and collectors using the TLS protocol. TLS must be configured for data encryption if data is pushed based on gRPC.
When designing IGP routes for an enterprise bearer WAN, ensure that the metric of aggregation-layer links is smaller than that of access-layer links, so that data can be preferentially forwarded over aggregation-layer links.
An enterprise has three types of services. Voice and video services are key services and need to be guaranteed, and FTP services are non-key services. Which of the following scheduling modes is optimal for satisfying the service requirements?
The figure shows an L3VPN over an SRv6 BE (Best Effort) network. According to the information displayed on PE2, which of the following statements is incorrect?
Collecting information before a cutover helps you determine whether services are normal before and after the cutover.
Before connecting an SSH client to an SSH server in public key authentication mode, a client needs to create a key pair. Which of the following commands is used to create a DSS key pair on the client using Git Bash?
On a CloudCampus virtualized campus network, which of the following modes can be used by a fabric to connect to external networks?
During the evolution from OSPFv2 to OSPFv3, LSA formats and functions remain unchanged, except that the network layer addresses in LSAs are changed from IPv4 to IPv6.
/ifm/interfaces/interface in Huawei Open Programmability System (OPS) is the URL used to identify a device ' s managed object.
Which of the following fields is added to BGP4+ Update packets to advertise IPv6 routes?
In the following figure, a GRE tunnel is established between R1 and R2. If the command ping -a 10.1.1.1 10.3.1.1 is run on R1, which of the following statements is correct about the ICMP packet sent by GE0/0/1 of R1?
After a wireless user passes Portal authentication, which of the following parameters cannot be used for authorizing the user?
OSPFv2 is an IGP running on IPv4 networks, whereas OSPFv3 is an IGP running on IPv6 networks. OSPFv2 and OSPFv3 have similar LSA types, but their LSA functions are slightly different. Which of the following is not an OSPFv3 LSA type?
A 32-bit MPLS header consists of a 20-bit label used for packet forwarding, a 3-bit EXP field that identifies the IP packet priority, a 1-bit bottom-of-stack flag that identifies the last label, and an 8-bit TTL field. Which statement regarding the TTL field is correct?
An LSR supports various label retention modes. Which of the following statements regarding the liberal mode are correct?
In the firewall hot standby scenario, which of the following status information can be backed up between the active and standby firewalls?
The naming of SRv6 instructions complies with certain rules. You can quickly determine the function of an instruction based on the instruction name. Which of the following statements about the keywords in SRv6 instruction names are correct?
A network administrator needs to retrieve a token ID from iMaster NCE using the following Python code:
import requests
nbi_name = " demol3@north.com "
nbi_pwd = " qqcOVcVel@ "
host = " 139.9.213.72 "
port = " 18002 "
URI = " /controller/v2/tokens "
post_token_url = " https:// " + host + " : " + port + URI
headers_post = { ' Content-Type ' : ' application/json ' , ' Accept ' : ' application/json ' }
r = requests.post(post_token_url, headers=headers_post, json={ " userName " : nbi_name, " password " : nbi_pwd}, verify=incorrect)
Which of the following statements is incorrect?