FCSS_EFW_AD-7.6 Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator Questions and Answers
What does the command set forward-domain < domain_ID > in a transparent VDOM interface do?
Why does the ISDB block layers 3 and 4 of the OSI model when applying content filtering? (Choose two.)
Refer to the exhibit, which shows a physical topology and a traffic log.
The administrator is checking on FortiAnalyzer traffic from the device with IP address 10.1.10.1, located behind the FortiGate ISFW device.
The firewall policy in on the ISFW device does not have UTM enabled and the administrator is surprised to see a log with the action Malware, as shown in the exhibit.
What are the two reasons FortiAnalyzer would display this log? (Choose two.)
You must configure a loopback as a BGP source to connect to the ISP.
Which two commands must you use to establish the connection? (Choose two.)
You configured the FortiGate devices in an enterprise network to join the Fortinet Security Fabric. You have a list of IP addresses that must be blocked by the data center firewall. This list is updated daily.
How can you automate updates to the firewall policy to add the IP addresses from the daily updated list?
Refer to the exhibit.
A LAN interface connected from FortiGate to two FortiSwitch devices is shown.
Which two statements about the LAN interface connection shown in the exhibit are correct? (Choose two.)
An administrator applied a block-all IPS profile for client and server targets to secure the server, but the database team reported the application stopped working immediately after.
How can an administrator apply IPS in a way that ensures it does not disrupt existing applications in the network?
Refer to the exhibits. The exhibits show a network topology, a firewall policy, and an SSL/SSH inspection profile configuration.
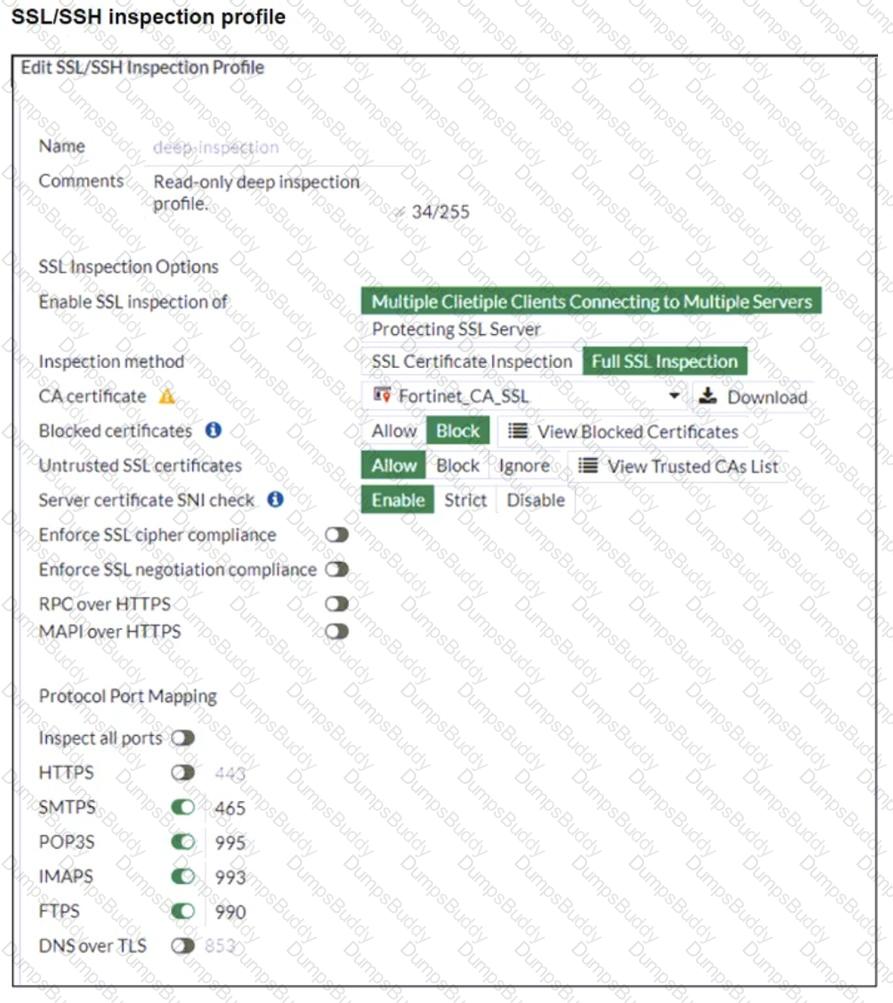
Why is FortiGate unable to detect HTTPS attacks on firewall policy ID 3 targeting the Linux server?
Refer to the exhibit.
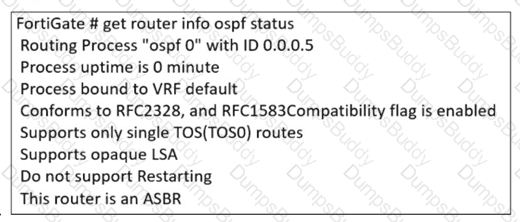
The partial output of an OSPF command is shown. You are checking the OSPF status of a FortiGate device when you receive the output shown in the exhibit. Based on the output, which two statements about FortiGate are correct? (Choose two answers)
Which two statements about IKEv2 are true if an administrator decides to implement IKEv2 in the VPN topology? (Choose two.)
An administrator is designing an ADVPN network for a large enterprise with spokes that have varying numbers of internet links. They want to avoid a high number of routes and peer connections at the hub.
Which method should be used to simplify routing and peer management?
Which two recommendations prevent invalid paths when using zero phase 2 selectors?
An administrator needs to install an IPS profile without triggering false positives that can impact applications and cause problems with the user ' s normal traffic flow.
Which action can the administrator take to prevent false positives on IPS analysis?
Refer to the exhibit, which contains the partial output of an OSPF command.
An administrator is checking the OSPF status of a FortiGate device and receives the output shown in the exhibit.
Which statement on this FortiGate device is correct?
Refer to the exhibits.
The system administrator settings configured on a root FortiGate and the Security Fabric settings configured on a downstream FortiGate are shown.
When prompted to sign in with Security Fabric to the downstream FortiGate, a user enters the single sign-on (SSO) provider credentials.
What is the result?
The IT department discovered during the last network migration that all zero phase selectors in phase 2 IPsec configurations impacted network operations.
What are two valid approaches to prevent this during future migrations? (Choose two.)
Refer to the exhibit, which shows the HA status of an active-passive cluster.
An administrator wants FortiGate_B to handle the Core2 VDOM traffic.
Which modification must the administrator apply to achieve this?
Refer to the exhibit, which shows the ADVPN IPsec interface representing the VPN IPsec phase 1 from Hub A to Spoke 1 and Spoke 2, and from Hub В to Spoke 3 and Spoke 4.
An administrator must configure an ADVPN using IBGP and EBGP to connect overlay network 1 with 2.
What must the administrator configure in the phase 1 VPN IPsec configuration of the ADVPN tunnels?
Which two parameters must you configure in neighbor-range for ADVPN iBGP deployment?
What is the initial step performed by FortiGate when handling the first packets of a session?
How will configuring set tcp-mss-sender and set tcp-mss-receiver in a firewall policy affect the size and handling of TCP packets in the network?
Refer to the exhibit, which shows the FortiGuard Distribution Network of a FortiGate device.
FortiGuard Distribution Network on FortiGate
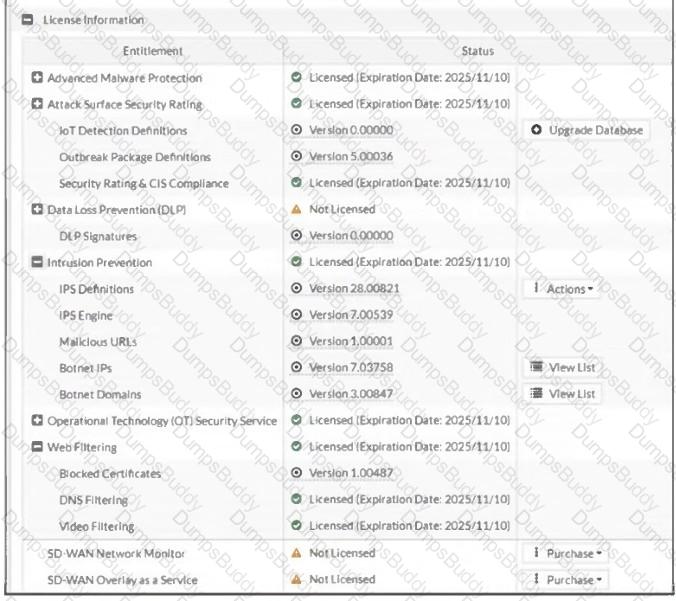
An administrator is trying to find the web filter database signature on FortiGate to resolve issues with websites not being filtered correctly in a flow-mode web filter profile.
Why is the web filter database version not visible on the GUI, such as with IPS definitions?
A user reports that their computer was infected with malware after accessing a secured HTTPS website. However, when the administrator checks the FortiGate logs, they do not see that the website was detected as insecure despite having an SSL certificate and correct profiles applied on the policy.
How can an administrator ensure that FortiGate can analyze encrypted HTTPS traffic on a website?
A company that acquired multiple branches across different countries needs to install new FortiGate devices on each of those branches. However, the IT staff lacks sufficient knowledge to implement the initial configuration on the FortiGate devices.
Which three approaches can the company take to successfully deploy advanced initial configurations on remote branches? (Choose three.)


