300-220 Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity 300-220 CBRTHD Questions and Answers
The SOC team receives an alert about a user sign-in from an unusual country. After investigating the SIEM logs, the team confirms the user never signed in from that country. The incident is reported to the IT administrator who resets the user's password. Which threat hunting phase was initially used?
Refer to the exhibit.
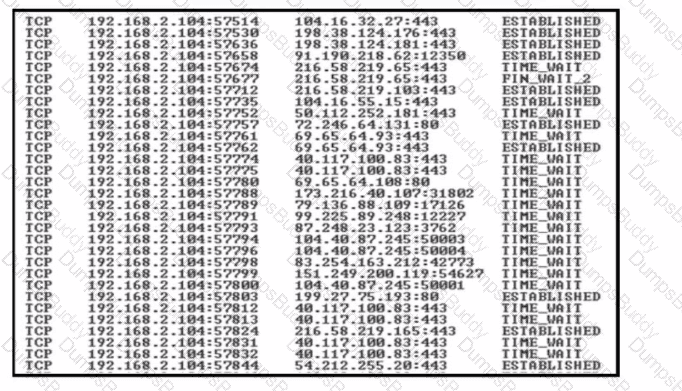
A security team detects a spike in traffic from the company web server. After further investigation, the team discovered that multiple connections have been established from the server to different IP addresses, but the web server logs contain both expected traffic and DDoS traffic. Which attribute must the team use to further filter the logs?
While investigating multiple incidents, analysts notice that attackers consistently use SMB for lateral movement and avoid PowerShell execution. Why is this observation valuable for attribution?
During an investigation, analysts observe that attackers consistently avoid PowerShell logging, disable AMSI, and prefer WMI for execution. Why is this information critical for attribution?
A threat hunting team wants to ensure hunts are repeatable, scalable, and less dependent on individual analyst intuition. What is the MOST important process improvement?
During multiple intrusions, analysts observe that attackers consistently perform internal reconnaissance before privilege escalation, avoid noisy exploitation, and limit actions to business hours of the victim’s region. Why is this observation important for attribution?
After a multi-week threat hunting exercise, a security team confirms that an attacker gained access using valid credentials, moved laterally, and exfiltrated data without deploying malware. Senior leadership asks how the hunting program reduced organizational risk. Which outcome BEST demonstrates the value of threat hunting?
A SOC team using Cisco security technologies wants to distinguishIndicators of Attack (IOAs)fromIndicators of Compromise (IOCs)during threat hunting. Which scenario BEST represents an IOA rather than an IOC?
Refer to the exhibit.
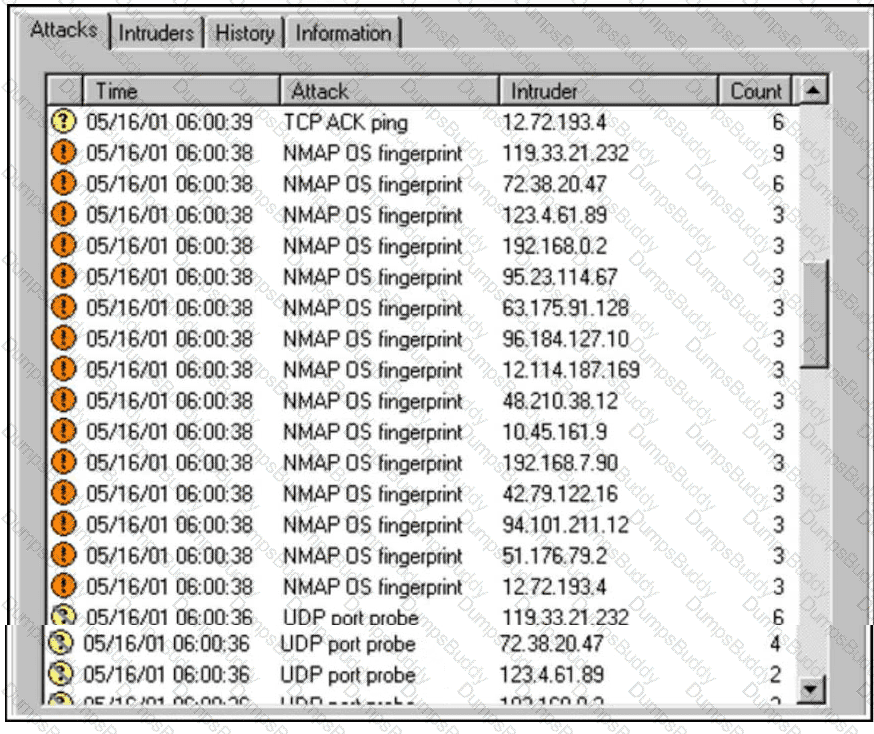
An increase in company traffic is observed by the SOC team. After they investigate the spike, it is concluded that the increase is due to ongoing scanning activity. Further analysis reveals that an adversary used Nmap for OS fingerprinting. Which type of indicators used by the adversary sits highest on the Pyramid of Pain?
Refer to the exhibit.
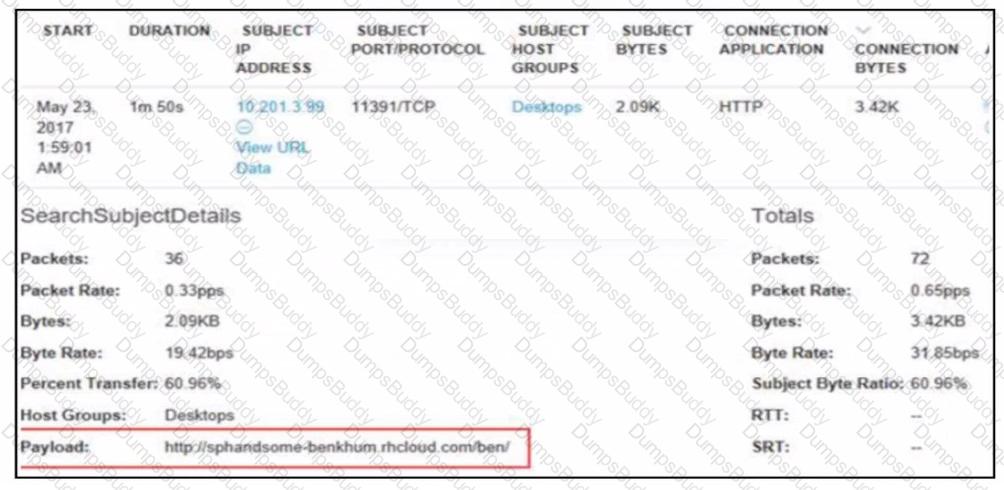
A security analyst receives an alert from Cisco Secure Network Analytics (formerly StealthWatch) with the C2 category. Which information aids the investigation?
During multiple investigations using Cisco telemetry, analysts observe attackers consistently perform internal discovery before privilege escalation and avoid high-risk actions. Why is this observation useful for attribution?
During a structured hunt, analysts using Cisco SIEM tools complete hypothesis testing and confirm malicious activity. What is the NEXT step in the Cisco threat hunting lifecycle?
A SOC analyst is usingCisco Secure Network Analytics (Stealthwatch)to hunt for command-and-control (C2) activity across the enterprise. The analyst wants to identify stealthy C2 channels that intentionally avoid known malicious IP addresses and domains. Which Stealthwatch hunting approach BEST supports this objective?
Which hunting technique is MOST effective for detecting stealthy data exfiltration over standard web protocols?


