400-007 Cisco Certified Design Expert (CCDE v3.1) Questions and Answers
Company XYZ plans to run OSPF on a DMVPN network. They want to use spoke-to-spoke tunnels in the design. What is a drawback or concern in this type of design?
What are three examples of solution components of the network infrastructure that help enforce security policy compliance on all devices as they seek to access the network and computing resources, thereby limiting damage from emerging security threats such as viruses, worms, and spyware? (Choose three)
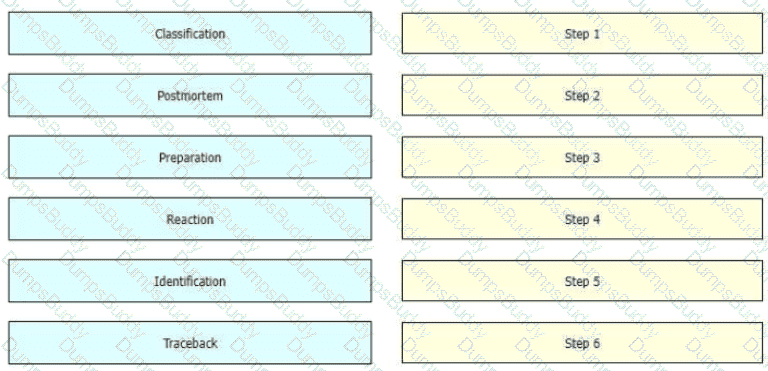
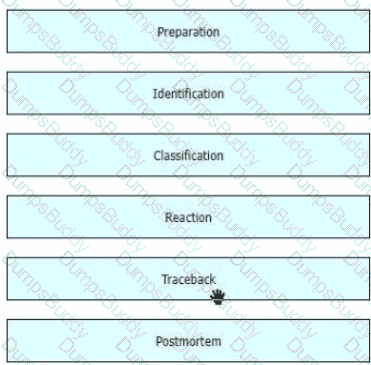
While computer networks and sophisticated applications have allowed individuals to be more productive the need to prepare for security threats has increased dramatically A six-step methodology on security incident handling has been adopted by many organizations including service providers enterprises, and government organizations to ensure that organizations are aware of significant security incidents and act quickly to stop the attacker, minimize damage caused, and prevent follow on attacks or similar incidents in the future Drag and drop the actions on the left to the targets on the right in the correct order.
You were tasked to enhance the security of a network with these characteristics:
A pool of servers is accessed by numerous data centers and remote sites
The servers are accessed via a cluster of firewalls
The firewalls are configured properly and are not dropping traffic
The firewalls occasionally cause asymmetric routing of traffic within the server data center.
Which technology should you recommend to enhance security by limiting traffic that could originate from a hacker compromising a workstation and redirecting flows at the servers?
The SD-WAN architecture is composed of separate orchestration, management, control, and data planes. Which activity happens at the orchestration plane?
As more links are added to the network, information and attributes related to the link is added to the control plane, meaning every link that gets added will slow down the convergence of the control plane by some measurable amount of time As a result when additional redundancy is built or added the MTTR will increase too Which risk increases along with the increased MTTR?
A large defense organization is planning their cloud migration journey, but they have high data sovereignty concerns, major regulation or compliance requirements, and very restrictive SLAs. Which cloud architecture model can be adopted?
The Layer 3 control plane is the intelligence over the network that steers traffic toward its intended destination Which two techniques can be used in service provider-style networks to offer a more dynamic, flexible, controlled, and secure control plane design? (Choose two.)
During initial preparations to deploy 802 1x for wired access to their network, a company must ensure that the solution complies with existing internal security policies These policies mandate that every Auth C/Auth Z request must be protected by a tunnel which authenticates both server and clients using their PKI AI the same time, the user authentication phase must be independent of the tunnel Which scheme meets the requirements?
multinational corporation with offices in various regions worldwide are looking for a network architecture that provides a balance between low- latency and cost-effectiveness for connecting their offices to the cloud. Which cloud connectivity option is the best fit for this corporation?
Which issue poses a challenge for security architects who want end-to-end visibility of their networks?
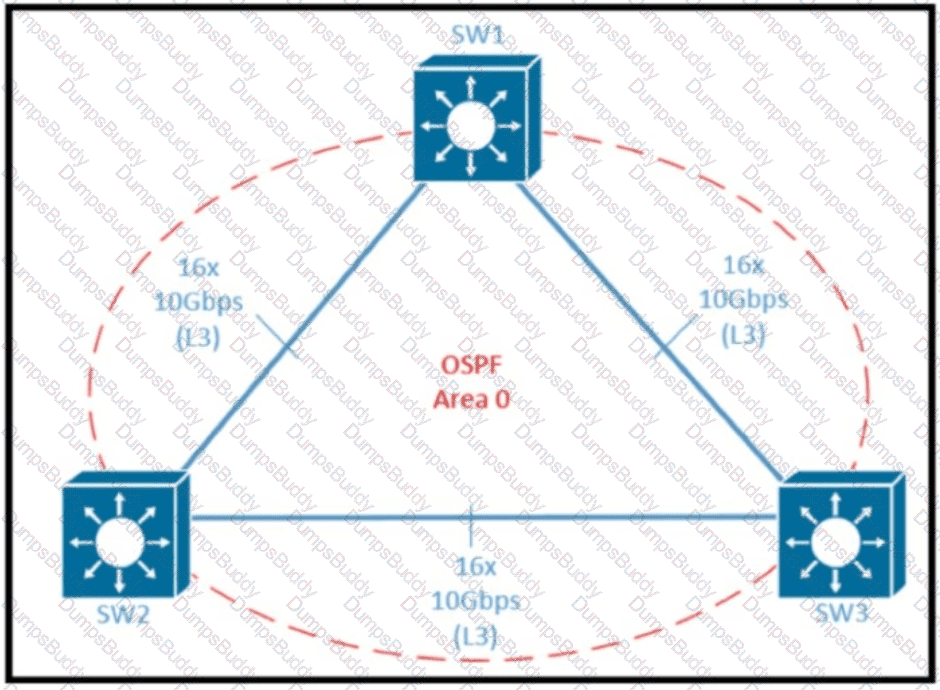
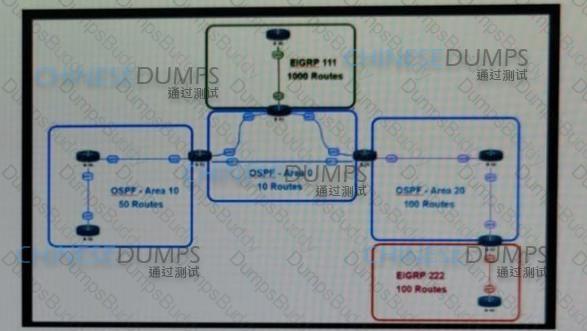
Refer to the exhibit Which two design options reduce the size of OSPF database in the shown topology? (Choose two.)
Refer to the exhibit.
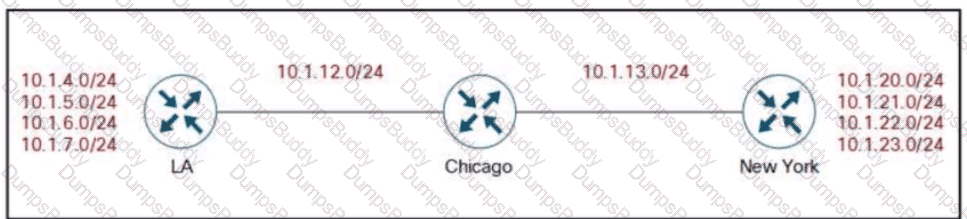
Company XYZ’s BGP topology is as shown in the diagram. The interface on the LA router connected toward the 10.1.5.0/24 network is faulty and is going up and down, which affects the entire routing domain. Which routing technique can be used in the routing policy design so that the rest of the network is not affected by the flapping issue?
Over the years, many solutions have been developed to limit control plane state which reduces the scope or the speed of control plane information propagation. Which solution removes more specific information about a particular destination as topological distance is covered in the network?
What are two advantages of the Agile project management methodology? (Choose two)
Refer to the exhibit.
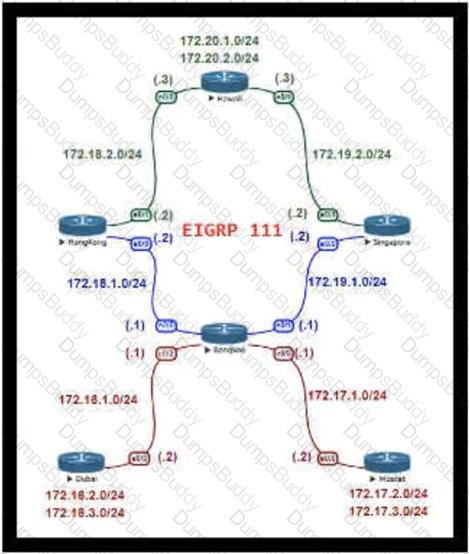
For Company XYZ, Bangkok is using ECMP to reach the 172.20.2.0/24 network. The company wants a design that would allow them to forward traffic from 172.16.2.0/24 toward 172.20.2.0/24 via the Singapore router as the preferred route. The rest of the traffic should continue to use ECMP. Which technology fulfills this design requirement?
Which regulatory compliance element ensures adherence to regulations and improves speed to market, which gives businesses a competitive advantage?
Which two features describe controller-based networking solutions compared to traditional networking solutions? (Choose two.)
risk is a major determining factor in whether a company chooses to go with a public cloud, a private, or a hybrid of both. what are two factors that impact the decision on which cloud service placement model to use? (choose two)
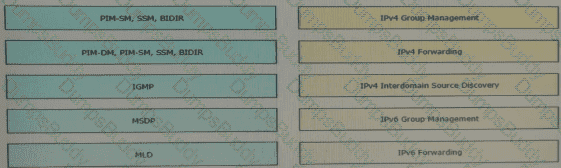
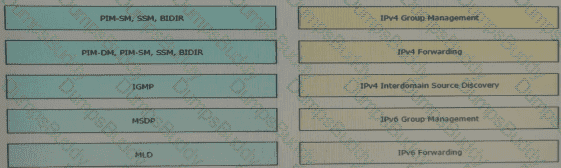
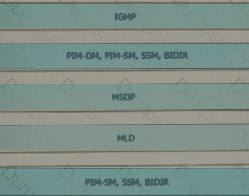
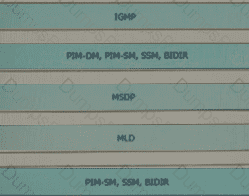
Drag and drop the multicast protocols from the left onto the current design situation on the right.
When planning their cloud migration journey, what is crucial for virtually all organizations to perform?
An IT service provider is upgrading network infrastructure to comply with PCI security standards. The network team finds that 802.1X and VPN authentication based on locally-significant certificates are not available on some legacy phones. Which workaround solution meets the requirement?
Which aspect of BGP-LS makes it scalable in large network when multiarea topology information must be gathered?
As network designer, which option is your main concern with regards to virtualizing multiple network zones into a single hardware device?
In a distributed cloud-native environment, calls to services and cloud resources can fail caused by unanticipated events that will require longer periods of time to resolve. These faults can range in severity from a partial loss of connectivity to the complete failure of a service. In these situations, it ' s pointless for an application to continually retry an operation that is unlikely to succeed. Which pattern can prevent an application from repeatedly trying to execute an operation that ' s likely to fail?
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
: 476
While designing a robust network architecture for a large e-commerce dient that has recently decided to make a global expansion of their cloud-based applications and services a network architect is evaluating cloud connectivity options The top priorities are low-latency and high- throughput connectivity between their on-premises data centers and the cloud providers Which cloud connectivity solution fits in this specific use case?
Which methodology is the leading lifecycle approach to network design and implementation?
A large enterprise cloud design team is evaluating cloud consumption models. What is an example of a typical PaaS limitation or concern?
A legacy enterprise is using a Service Provider MPLS network to connect its head office and branches. Recently, they added a new branch to their network. Due to physical security concerns, they want to extend their existing IP CCTV network of the head office to the new branch, without any routing changes in the network. They are also under some time constraints. What is the best approach to extend the existing IP CCTV network to the new branch, without incurring any IP address changes?
Which two benefits can software defined networks provide to businesses? (Choose two.)
Company XYZ wants to prevent switch loops caused by unidirectional point-to-point link conditions on Rapid PVST+ and MST. Which technology can be used in the design to meet this requirement?
Refer to the exhibit.
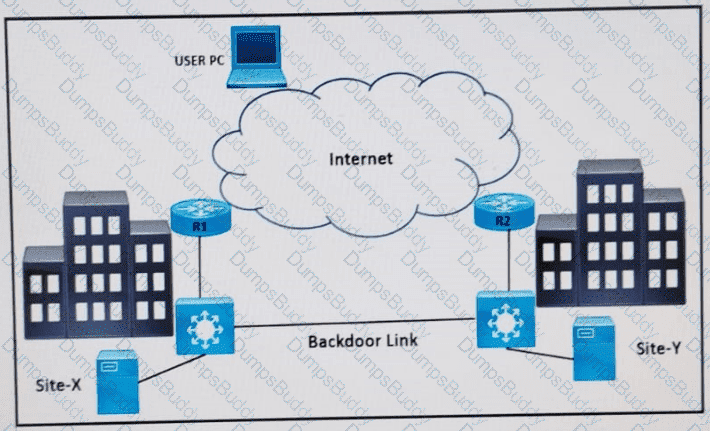
Refer to the exhibit. Two data center sites (X and Y) connect to the Internet and each other using a backdoor link. Both advertise the same IP prefix (100.75.10.0/23) to the Internet. Firewalls are behind R1 and R2.
Problem: When users attempt to reach 100.75.10.0/23, the return traffic is routed to Site-Y, regardless of where the session originated. This results in asymmetric traffic and potentially broken sessions due to firewall behavior.
Which design resolves the issue?
You have been tasked with designing a data center interconnect to provide business continuity. You want to encrypt the traffic over the DCI using IEEE 802.1AE MACsec to prevent the deployment of any firewall or IPS. Which two interconnect technologies support MACsec? (Choose two.)
Which optimal use of interface dampening on a fast convergence network design is true?
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
An organization is looking to perform a major overhaul on their data center storage infrastructure with a focus on high availability and fault tolerance Which approach will accomplish this?
: 488
The modularity built into the architecture allows flexibility in network design and facilitates implementation and troubleshooting Which solution is difficult to implement manage and troubleshoot especially for large networks?
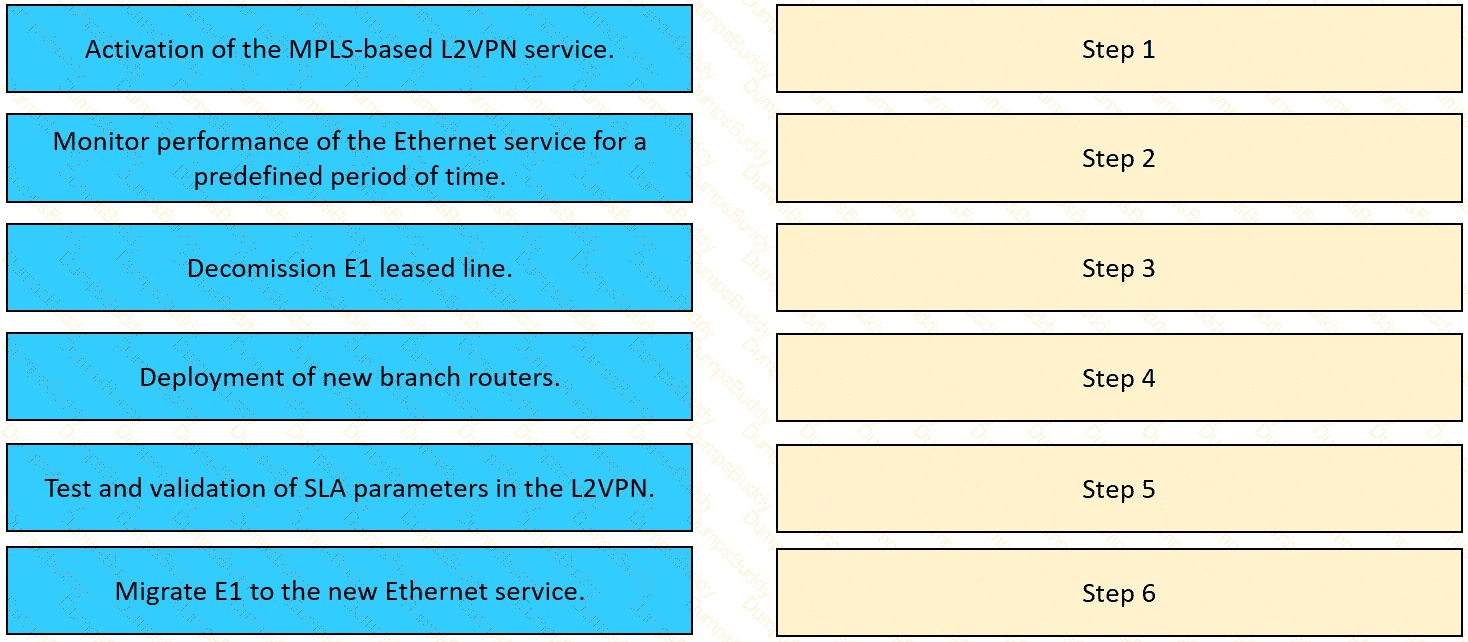
The network team in XYZ Corp wants to modernize their infrastructure and is evaluating an implementation and migration plan to allow integration MPLS-based, Layer 2 Ethernet services managed by a service provider to connect branches and remote offices. To decrease OpEx and improve
response times when network components fail, XYZ Corp decided to acquire and deploy new routers. The network currently is operated over E1 leased lines (2 Mbps) with a managed CE service provided by the telco.
Drag and drop the implementation steps from the left onto the corresponding targets on the right in the correct order.
The Company XYZ network is experiencing attacks against their router. Which type of Control Plane Protection must be used on the router to protect all control plane IP traffic that is destined directly for one of the router interfaces?
Your company wants to deploy a new data center infrastructure. Based on the requirements you have chosen VXLAN as encapsulation technology. The customer is concerned about misconfiguration of Layer 2 devices and DC-wide outages caused by Layer 2 loops. What do you answer?
A business wants to refresh its legacy Frame Relay WAN and consolidate product specialists via video in 200 branches. Which technology should be used?
: 475
Company XYZ is a large US-based online retailer that is preparing for a major sale scheduled for the holiday season. Large volumes of dynamic workloads are expected, which are time sensitive and seasonal. In anticipation of the surge in data, they are re-architecting their workload management. Which two technical considerations for service placement of workloads should be considered? (Choose two.)
: 494 DRAG DROP
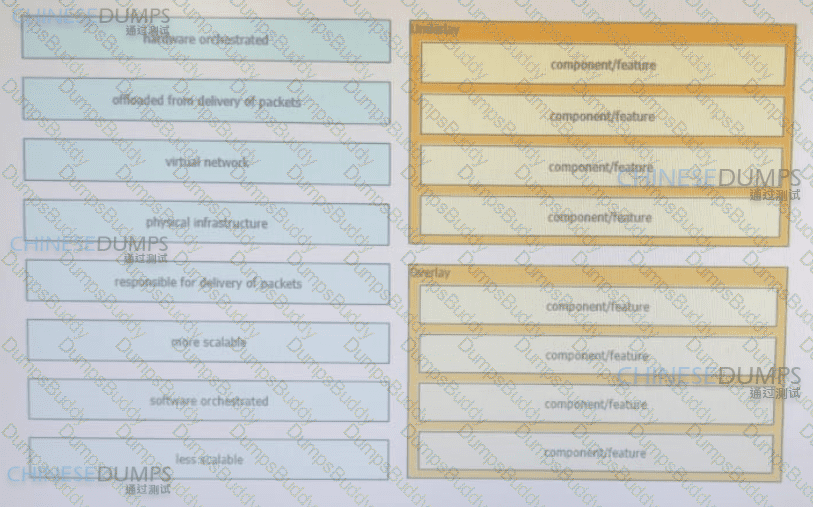
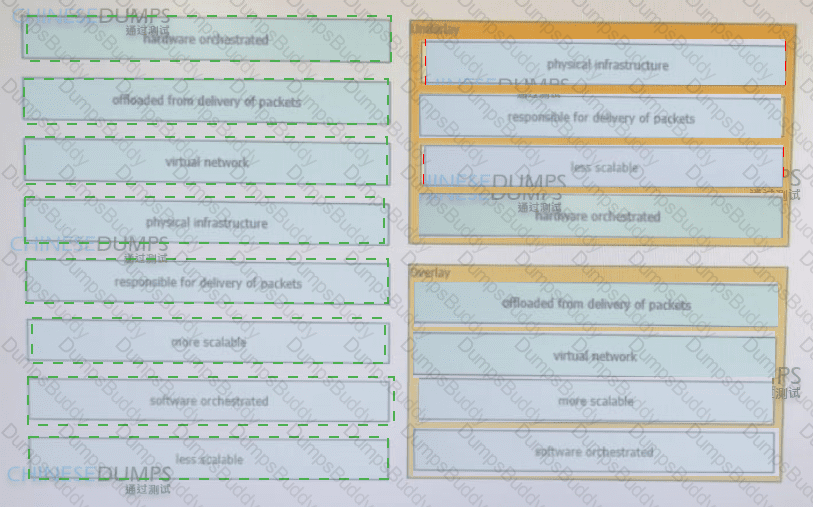
The customer ' s network manager asked for some key points to use m a presentation on overlay/underlay features and responsibilities. Drag and drop the features or responsibilities from the left onto the corresponding groups on the right in no particular order.
What are two top cloud-native security challenges faced by today ' s cloud-oriented organizations? (Choose two.)
: 501
An organization who recently adapted SDWAN has been using CPU intensive policy routing on their new WAN edge device in the HQ to forward traffic to one of its branches which hosts the enterprise firewall What can replace the CPU intensive policy routing?
What is an advantage of using Agile over Waterfall methodology in the network design lifecycle?
: 485
Traditionally, infrastructure is not managed using code but instead it is managed and provisioned manually which can cause potential issues On the other side, infrastructure as code brings several advantages What is a benefit of infrastructure as code?
What are two primary design constraints when a robust infrastructure solution is created? (Choose two.)
Refer to the exhibit.

Which impact of using three or more ABRs between the backbone area and area 1 is true?
Company XYZ has two routing domains (EIGRP and OSPF). They want full reachability and need OSPF to see link costs added to external routes. How must redistribution be designed?
What are two advantages of controller-based networks versus traditional networks? (Choose two.)
A service provider recently migrated to an SD-WAN solution for delivering WAN connections to its customers. One of the main challenges with the SD-WAN deployment is that branch site volume increases every year, which causes management complexity. Which action resolves the issue?
You are using iSCSI to transfer files between a 10 Gigabit Ethernet storage system and a 1 Gigabit Ethernet server. The performance is only approximately 700 Mbps and output drops are occurring on the server switch port. Which action will improve performance in a cost-effective manner?
You are designing a network for a branch office. In order to improve convergence time, you are required to use the BFD feature. Which four routing protocols can you use to facilitate this? (Choose four.)
An enterprise SDWAN customer based in the US has several branches in Europe Currently branches use the HQ in the US to access both internal and external services over an MPLS arcuit The design team has been tasked to suggest a solution allowing branches to access their cloud-based office productivity tools and services directly Since all their applications and services are hosted in the cloud, the design team has also been asked to come up with a solution, so branches can connect to the cloud directly from the branch as well Which two cost-effective and optimized solutions can be suggested? (Choose two)
cloud onRamp (SaaS)
Which purpose of a dynamically created tunnel interface on the design of IPv6 multicast services is true?
What is a disadvantage of the traditional three-tier architecture model when east-west traffic between different pods must go through the distribution and core layers?
Modem IT departments are more service oriented than they used to be To meet the needs oí their customers. IT departments are spending more time analyzing and documenting their processes for delivering services A focus on processes helps to ensure effective service delivery and to avoid wasted expenditures on technology that doesn ' t provide a needed service What defines frameworks and processes that can help an organization match the delivery of IT services with the business needs of the organization?
Reter to the exhibit This network is running OSPF and EIGRP as the routing protocols Mutual redistribution of the routing protocols has been contoured on the appropriate ASBRs The OSPF network must be designed so that flapping routes m EIGRP domains do not affect the SPF runs within OSPF The design solution must not affect the way EIGRP routes are propagated into the EIGRP domains Which technique accomplishes the requirement?
What is the most important operational driver when building a resilient and secure modular network design?
A company uses equipment from multiple vendors in a data center fabric to deliver SDN, enable maximum flexibility, and provide the best return on investment. Which YANG data model should be adopted for comprehensive features to simplify and streamline automation for the SDN fabric?
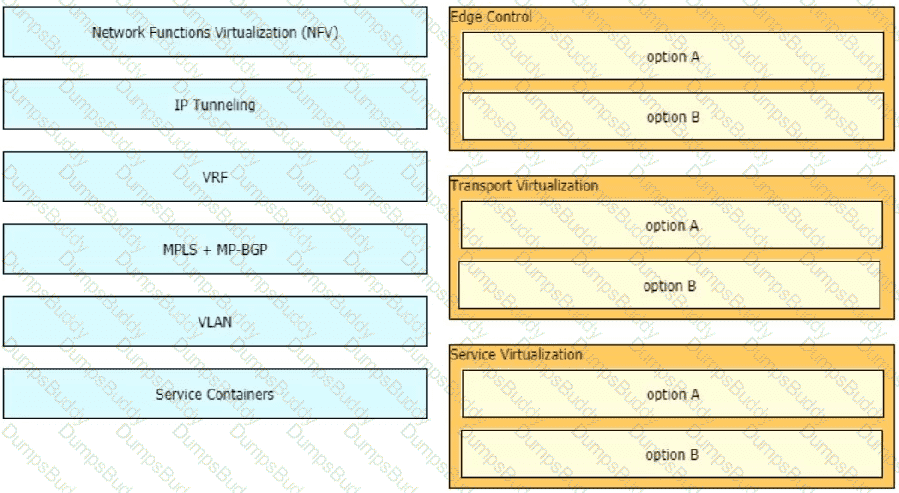
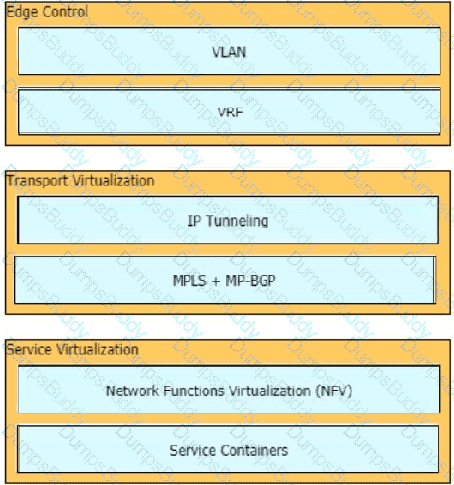
Drag and drop the end-to-end network virtualization elements from the left onto the correct network areas on the right.
Company XYZ wants to redesign the Layer 2 part of their network to use all uplinks for increased performance, support host reachability with conversational learning, and avoid port-channels. Which other technique can be used?
Which parameter is the most important factor to consider when deciding service placement in a cloud solution?
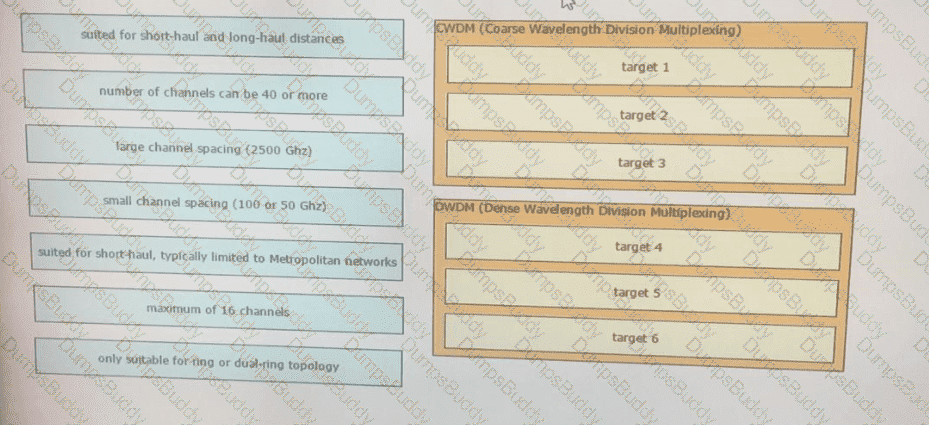
Drag and drop the optical technology design characteristics on the left to the correct optical technologies on the right. Not all options are used
A network architect is designing a policy where database applications access the internet directly, while other traffic routes through the data center, with dynamic path switching based on performance. Which solution meets these requirements?
What is an architectural framework created by ETSI that defines standards to decouple network functions from proprietary hardware-based appliances and have them run in software on standard x86 servers?
Which aspect of BGP-LS makes it scalable in large networks when multiarea topology information must be gathered?
: 484
Traditionally networks handled static web pages e-mail and routine client/server traffic Today enterprise networks must handle more sophisticated types of network applications that include voice and video Applications place increasing demands on IT infrastructures as they evolve into highly visible services that represent the face of the business to internal and external audiences The large amount and variety of data requires that the modern network be aware of the content earned across it to optimally handle that content. Which service provide this intelligence?
which two actions must be taken when assessing an existing wireless network implementation for its readliness to support voice traffic? (choose two)
A company requires an RPO of less than 10 seconds to ensure business continuity. Which technology should be deployed?
A small organization of 20 employees is looking to deliver a network design service for modernizing customer networks to support advanced solutions.
Project scope and weekly progress should be visualized by the management.
Always consider feedback and make changes accordingly during the project.
Should consider flexibility to change scope at any point in time.
Which project methodology meets the requirements and has the least impact on the outcome?
A business invests in SDN and develops its own SDN controller that, due to budget constraints, runs on a single controller. The controller actively places an exclusive lock on the configuration of the devices to ensure it is the only source of changes to the environment. What is the result if the controller fails?
The controller has a global view of the network, and it can easily ensure that the network is in a consistent and optimal configuration. Which two statements describe a centralized SDN control path? (Choose two.)
A rapidly growing e-commerce business with a global customer base needs a robust network design that can support their business-critical operations and ensure low-latency access for their customers around the globe. The IT team is considering different solutions to meet their requirements. Which network design is suitable for these needs?
: 487
Which layer of the SDN architecture orchestrates how the applications are given the resources available in the network?
Network changes due to mergers, acquisitions, and divestitures can be highly disruptive if not carefully planned. When an organization sells part of its business, it must detach those parts of the network with minimal risk and downtime.
Which network design approach is appropriate to minimize the impact and risks as the divested parts of the network are detached?
A network hacker is trying to interrupt the transport packet on IPsec. A packet with duplicate sequence numbers is introduced. The customer sends high-priority traffic during this window. Which design parameter should be considered to mitigate this issue?
A network security team uses a purpose-built tool to actively monitor the campus network, applications, and user activity. The team also analyzes enterprise telemetry data from IPFIX data records that are received from devices in the campus network. Which action can be taken based on the augmented data?
Which two factors must be considered for high availability in campus LAN designs to mitigate concerns about unavailability of network resources? (Choose two.)
: 491
Budget is one of the important factors when you design a network Regardless of who controls the budget, one common network design goal is to contain costs Reduced budgets or limited resources often force network designers to select the most affordable solution instead of the best solution Which two elements must be considered when you do ROI analysis for the network design that explains how quickly the new network w ill pay for itself’ (Choose two. )
An architect receives a functional requirement for a NAC system from a customer security policy stating that if a corporate Wi-Fi device does not meet current AV definitions, it cannot access the network until updated. Which component should be built into the NAC design?
A banking customer determines that it is operating POS and POI terminals that are noncompliant with PCI DSS requirements, as it is running TLSv1.0. The customer plans to migrate the terminals to TLSv1.2. What are two requirements to complete the migration? (Choose two.)
Refer to the exhibit.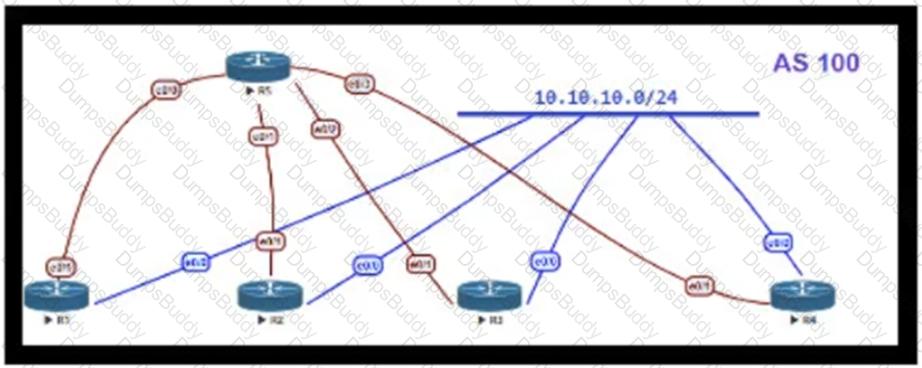
OSPF is running as the IGP to provide reachability to all AS100 networks. R3 and R4 are the current ABRs at the boundary of OSPF Area 0 and Area 1. Now BGP must be deployed within AS 100 because it will be receiving Internet routes from its eBGP peers (the service provider) connected to R1 and R2. What is an optimal solution for this deployment to configure BGP relationships and redistribute BGP learned routes into OSPF?
A software-defined network exposes an API to the RIB and forwarding engine, allowing off-box control of routing—what SDN model is used?
Before migrating anything to the cloud, what are three cloud readiness assessment steps that are required to perform? (Choose three.)
A Service Provider is designing a solution for a managed CE service to a number of local customers using a single CE platform and wants to have logical separation on the CE platform using Virtual Routing and Forwarding (VRF) based on IP address ranges or packet length. Which is the most scalable solution to provide this type of VRF Selection process on the CE edge device?
The Company XYZ network requires OSPF dead neighbor detection in a subsecond manner. However, the company network does not support BFD. Which other feature can be used to fulfill the design requirement?
Which two benefits can software-defined networks provide to businesses? (Choose two.)
A multinational enterprise integrates a cloud solution with these objectives:
• Achieve seamless connectivity across different countries and regions
• Extend data center and private clouds into public clouds and provider-hosted clouds
What are two outcomes of deploying data centers and fabrics that interconnect different cloud networks? (Choose two.)
Which two statements describe the usage of the IS-IS overload bit technique? (Choose two.)
: 490
In order to achieve key business objectives, the design team of a hosting provider has identified a series of objectives in their cloud computing environments
•Customer data privacy and protection against external vulnerabilities must be improved.
•Access to sensitive data must be monitored and relevant regulations must be adhered to.
•Use data analyzing to optimize operations and business decision-making
Which step must be take to meet these requirements?
A business requirement stating that failure of WAN access for dual circuits into an MPLS provider for a Data Centre cannot happen due to related service credits that would need to be paid has led to diversely routed circuits to different points of presence on the provider’s network. What should a network designer also consider as part of the requirement?
You have been tasked with designing a data center interconnect as part of business continuity. You want to use FCoE over this DCI to support synchronous replication. Which two technologies allow for FCoE via lossless Ethernet or data center bridging? (Choose two.)
Which two features are advantages of SD-WAN compared to MPLS-based connectivity? (Choose two.)
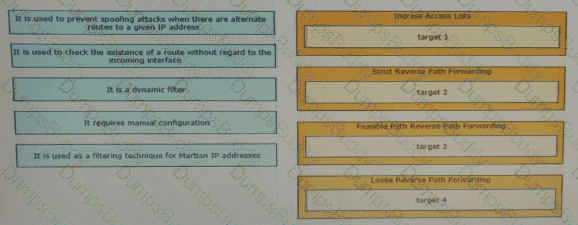
Drag and drop the design characteristics from the left onto the correct network filter techniques on the right. Not all options are used.
An existing wireless network was designed to support data traffic only. You must now install context-aware services for location tracking. What changes must be applied to the existing wireless network to increase the location accuracy? (Choose two)
Company XYZ is running a redundant private WAN network using OSPF as the underlay protocol. The current design accommodates for redundancy in the network, but it is taking over 30 seconds for the network to reconverge upon failure. Which technique can be implemented in the design to detect such a failure in a subsecond?
What is the key strategy to address scalability challenges In the rapidly evolving digital landscape with resilient designs?
: 482
Even with two different device platforms that support NETCONF or any other common transport method it does not mean they are compatible from a tooling and/or a developer’s perspective What is required to get the compatibility?
Refer to the table.
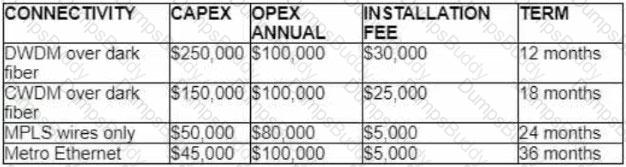
A customer investigates connectivity options for a DCI between two production data centers to aid a large-scale migration project. The solution must provide a single 10G connection between locations and be able to run its own varying QoS profiles without service provider interaction based on the migration stages. All connectivity methods are at 10 Gbps. Which transport technology costs the least if the connectivity is required for just one year?
A company with an existing multivendor network is moving from 1 G dark fiber to an ISP virtual leased-line solution The company ' s internal security policy states that any traffic traversing a network that is not owned by the company must be encrypted What must be used to meet the requirements?
Drag and drop the multicast protocols from the left onto the current design situation on the right.
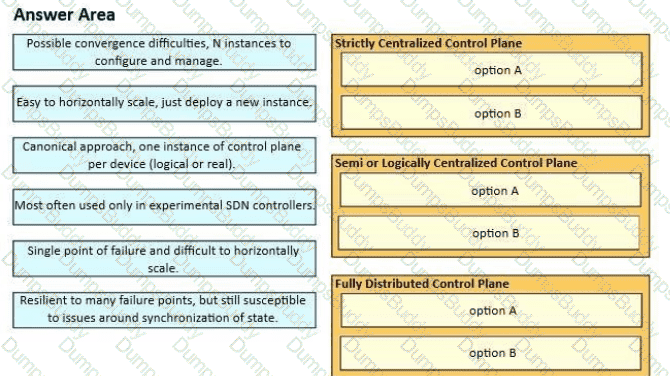
Network operators have many options available, from fully centralized to fully distributed control planes, and each approach has its own set of characteristics. Drag and drop the characteristics from the left onto the corresponding approach on the right.
You are designing an Out of Band Cisco Network Admission Control Layer 3 Real-IP Gateway deployment for a customer. Which VLAN must be trunked back to the Clean Access Server from the access switch?
: 503
As organizations rush to implement AI, many fail to address its ethical considerations Not examining those issues puts an organization at risk of legal violations, loss of customer trust and long-term reputational damage. Which two ethical standards are required in preven ting such pitfalls? (Choose two. )
What is a web-based model in which a third-party provider hosts applications that are available to customers over the Internet?
What are the two benefits of using northbound APIs in SDN architecture? (Choose two.)
A consultant needs to evaluate project management methodologies for a new service deployment on the existing network of a customer. The customer wants to be involved in the end-to-end project progress and be provided with frequent updates. The customer also wants the ability to change the requirements if needed, as the project progresses. Which project management methodology should be used?
Which two mechanisms avoid suboptimal routing in a network with dynamic mutual redistribution between multiple OSPFv2 and EIGRP boundaries? (Choose two.)
An Agile for Infrastructure transition often means dismantling traditional IT hierarchies and rebuilding it to align with business objectives and workflows. Organizations are seeing the benefits of using automation tools in the network such as faster, more efficient, and more effective delivery of products and services. Which two components help increase overall productivity and improve company culture? (Choose two.)
Your network operations team is deploying Access Control Lists (ACLs) across your Internet gateways. They wish to place an ACL inbound on the Internet gateway interface facing the core network (the " trusted " interface). Which IP address would the ACL need for traffic sourced from the inside interface, to match the source address of the traffic?
What are two reasons for a company to prefer a hybrid approach rather than a mixed approach while transitioning to a software-defined network? (Choose two.)
SDN is still maturing. Throughout the evolution of SDN, which two things will play a key role in enabling a successful deployment and avoiding performance visibility gaps in the infrastructure? (Choose two.)
Which two statements explain the operation of BFD asynchronous mode? (Choose two.)
While reviewing an existing network design, you are discussing the characteristics of different STP versions. Which protocol minimizes unicast flooding during a Topology Change Notification in a Layer 2 switched network with many VLANs?
Virtualization pose a special challenges for NAC because virtual servers can move around a data center, and the VLAN can change as the servers move. What is an option that can be used to improve security in this condition?
In the wake of a security compromise incident where the internal networks were breached by an outside attacker at the perimeter of the infrastructure, an enterprise is now evaluating potential measures that can help protect against the same type of incident in the future. What are two design options that can be employed? (Choose two)
Company XYZ connects its sites over a private WAN. Their overlay network is running a DMVPN setup where the headquarters site is the hub. The company is planning on implementing multicast routing on the network. What should be used in the multicast routing design?
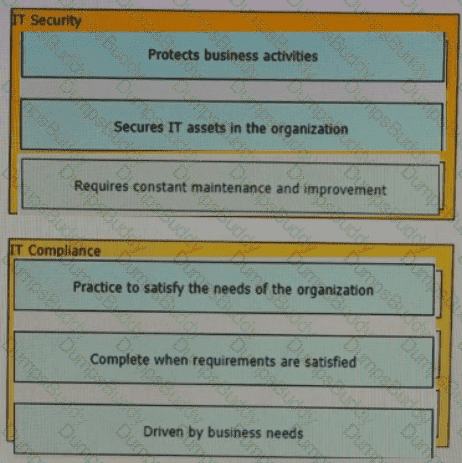
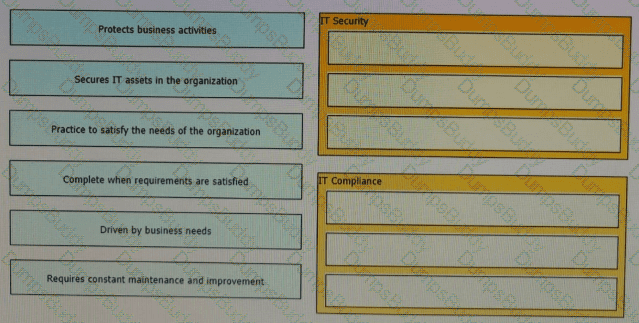
The line between security and compliance is easily blurred and is, to a large extent, a moving target Drag and drop each of the requirements on the left to the appropriate section on the right
: 498
When organizations initially start consuming public cloud services, they often use VPNs over the internet to connect their on-premises applications to the public cloud infrastructure. In which two cases are other connectivity methods a better fit? (Choose two.)
Which function is performed at the access layer of the three-layer hierarchical network design model?
In large-scale networks controllers needs to be able to process millions of flows per second without compromising the quality of the service What are two actions that must be implemented to address scaling limitations when deploying the network*? (Choose two.)
An engineer must design a network for a company that uses OSPF LFA to reduce loops. Which type of loop would be reduced by using this design?
A large enterprise is planning a new WAN connection to headquarters. The current dual-homed setup with static routing is not providing consistent resiliency. Users complain when one specific link fails, while failure of the other causes no issues. The organization wants to improve resiliency and ROI.
Which solution should be recommended?
: 473
A network consists of multiple planes where each plane represents a different area of network operations and cames different types of network traffic Which two statements describe the concepts of assurance in the context of control planes? (Choose two.)
An architect designs a multi-controller network architecture with these requirements:
Achieve fast failover to control traffic when controllers fail.
Yield a short distance and high resiliency in the connection between the switches and the controller.
Reduce connectivity loss and enable smart recovery to improve the SDN survivability.
Improve connectivity by adding path diversity and capacity awareness for controllers.
Which control plane component of the multi-controller must be built to meet the requirements?
A product manufacturing organization is integrating cloud services into their IT solution. The IT team is working on the preparation phase of the implementation approach, which includes the Define Strategy step. This step defines the scope of IT, the application, and the service. What is one topic that should be considered in the Define Strategy step?
An external edge router provides connectivity from a service provider to an enterprise. Which two Internet edge best practices meet compliance regulations? (Choose two)
As a service provider is implementing Strong Access Control Measures, which two of the following PCI Data Security Standard requirements must be met? (Choose two . )
SD-WAN can be used to provide secure connectivity to remote offices, branch offices, campus networks, data centers, and the cloud over any type of IP-based underlay transport network. Which two statements describe SD-WAN solutions? (Choose two.)
Which three Cisco products are used in conjunction with Red Hat to provide an NFVi solution? (Choose three.)
Refer to the exhibit.

The enterprise customer wants to stream one-way video from their head office to eight branch offices using multicast. Their current service provider provides a Layer 3 VPN solution and manages the CE routers, but they do not currently support multicast. Which solution quickly allows this multicast traffic to go through while allowing for future scalability?
Company ABC uses IPv4-only. Recently they started deploying new endpoint devices. For operational reasons, IPv6 cannot be disabled on these new endpoint devices. Which security measure prevents the new endpoint from learning an IPv6 prefix from an attacker?
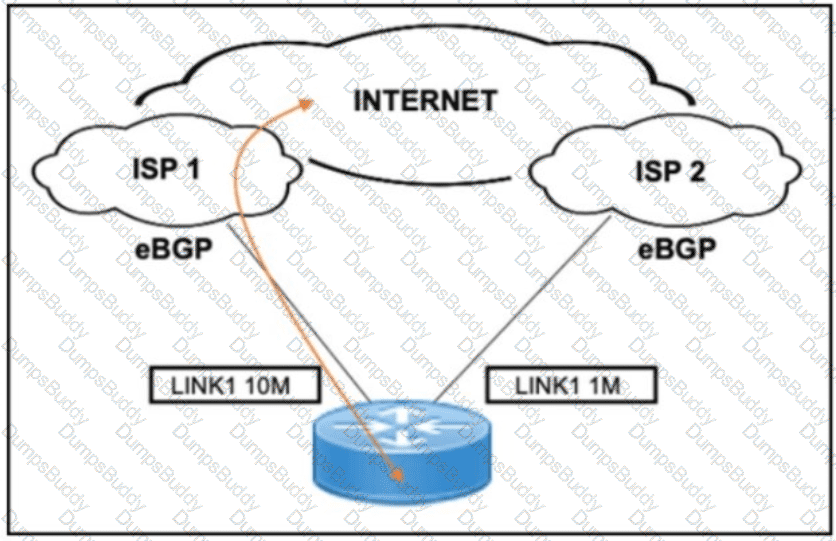
Refer to the exhibit. A customer needs to implement a connectivity model by using one active link for inbound and outbound traffic and a second link for backup. The backup link is low speed and is required only during outages of the primary link. Which design solution should be implemented?
Refer to the exhibit.
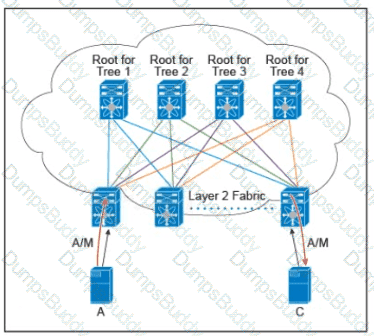
There are multiple trees in the Cisco FabricPath. All switches in the Layer 2 fabric share the same view of each tree. Which two concepts describe how the multicast traffic is load-balanced across this topology? (Choose two.)
Refer to the exhibit.
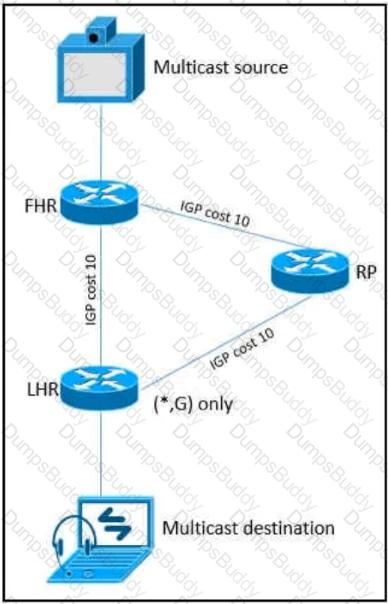
As part of a redesign project, you must predict multicast behavior. What happens to the multicast traffic received on the shared tree (*,G), if it is received on the LHR interface indicated?


 A picture containing table Description automatically generated
A picture containing table Description automatically generated
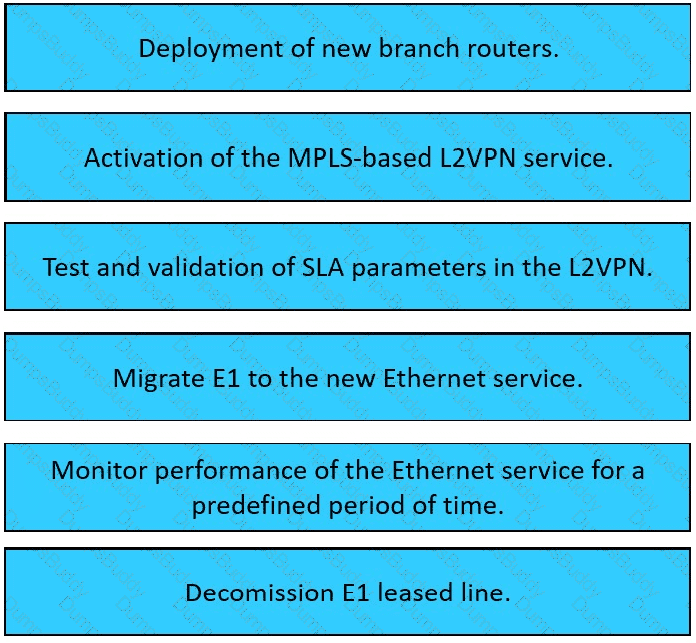 Table Description automatically generated
Table Description automatically generated

 Graphical user interface Description automatically generated with medium confidence
Graphical user interface Description automatically generated with medium confidence

 A picture containing table Description automatically generated
A picture containing table Description automatically generated