350-401 Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR) Questions and Answers
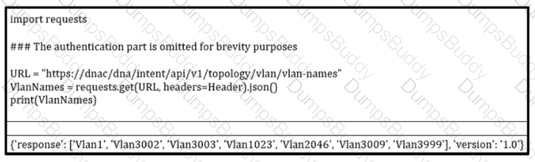
Refer to the exibit. How should the programmer access the list of VLANs that are recevied via the API call?
What is a client considered when it is in web authentication state and roams between two controllers with mobility tunnels?
Which AP mode allows a supported AP to function like a WLAN client would, associating and identifying client connectivity issues?
An engineer is implementing a new SSID on a Cisco Catalyst 9800 Series WLC that must be broadcast on 6 GHz radios. Users will be required to use EAP-TLS to authenticate. Which wireless Layer 2 security method is required?
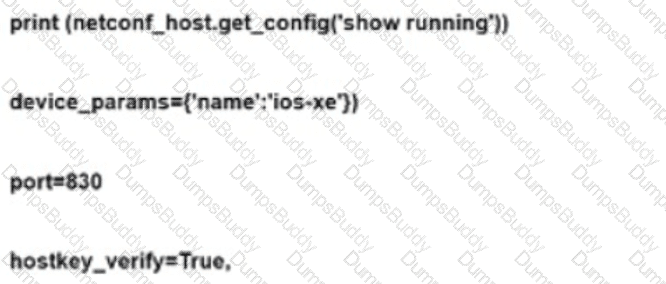
Refer to the exhibit. A network engineer must configure NETCONF. After creating the configuration, the engineer gets output from the command show line, but not from show running-config. Which command completes the configuration?
Which language defines the structure or modeling of data for NETCONF and RESTCONF?
A customer requests a design that includes GLBP as the FHRP. The network architect discovers that the members of the GLBP group have different throughput capabilities. Which GLBP load balancing method supports this environment?
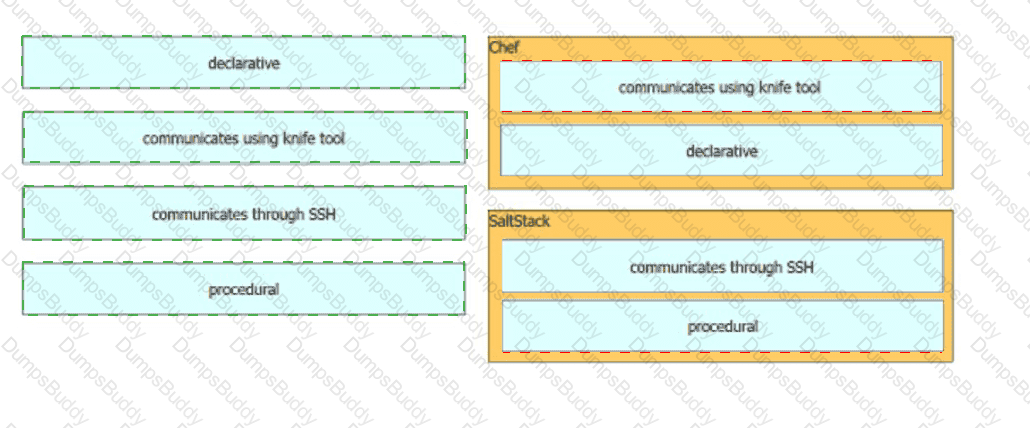
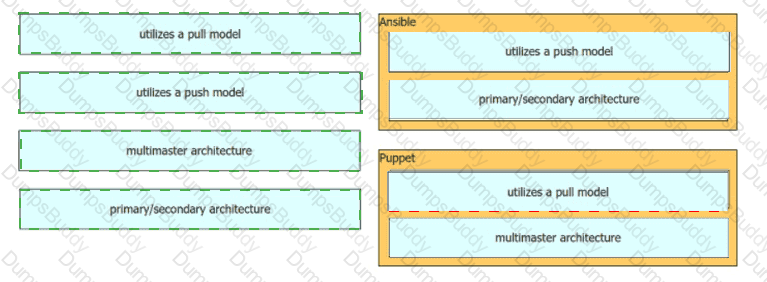
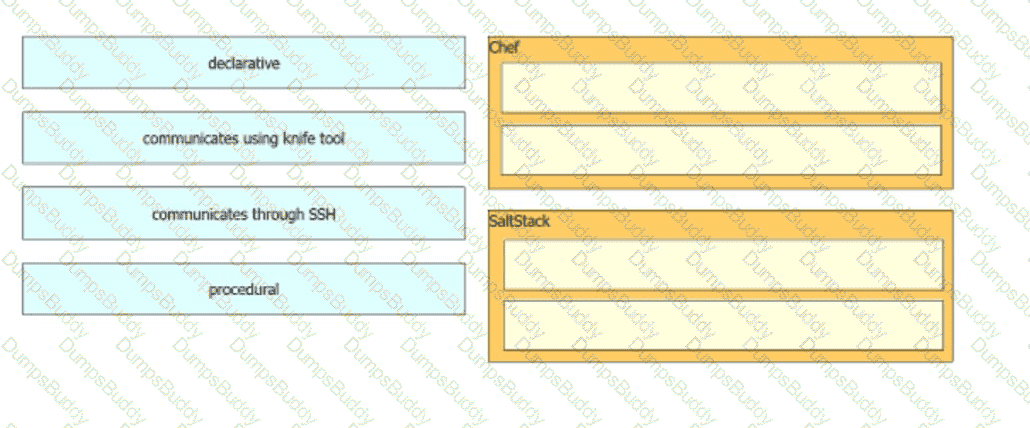
Drag and drop the characteristics from the left into the orchestration tools that they describe on the right.
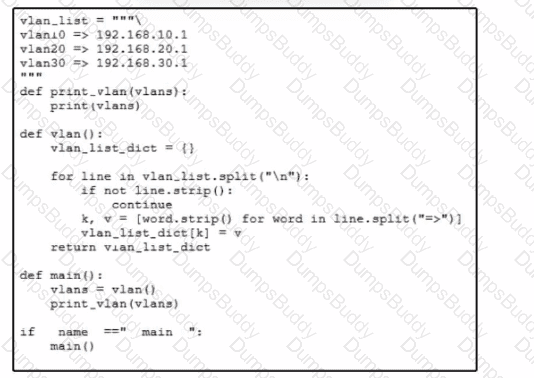
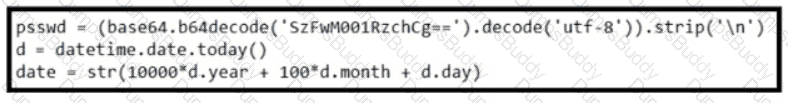
Refer to the exhibit A network engineer must use a Python script lo convert data received from a network device. Which type of data is printed to the console when the script runs?
What is provided by the Stealthwatch component of the Cisco Cyber Threat Defense solution?
An engineer must create an EEM script to enable OSPF debugging in the event the OSPF neighborship goes down. Which script must the engineer apply?
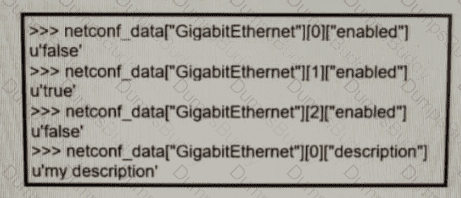
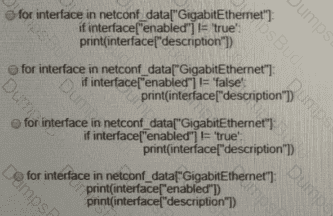
Refer to the exhibit. Which python code snippet prints the descriptions of disabled interface only?
In Cisco CatalystCenter(formerly DNA Center) Inventory, the Software Version of a networkdevice displays a status of OUTDATED. What does It me?
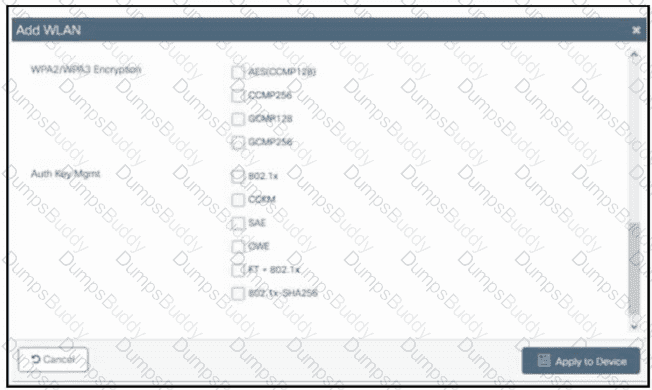
Refer to the exhibit. A customer asks an engineer to create a new secure WLAN to support only WPA3. Users must connect using a passphrase. Which encryption and key management configuration is required?
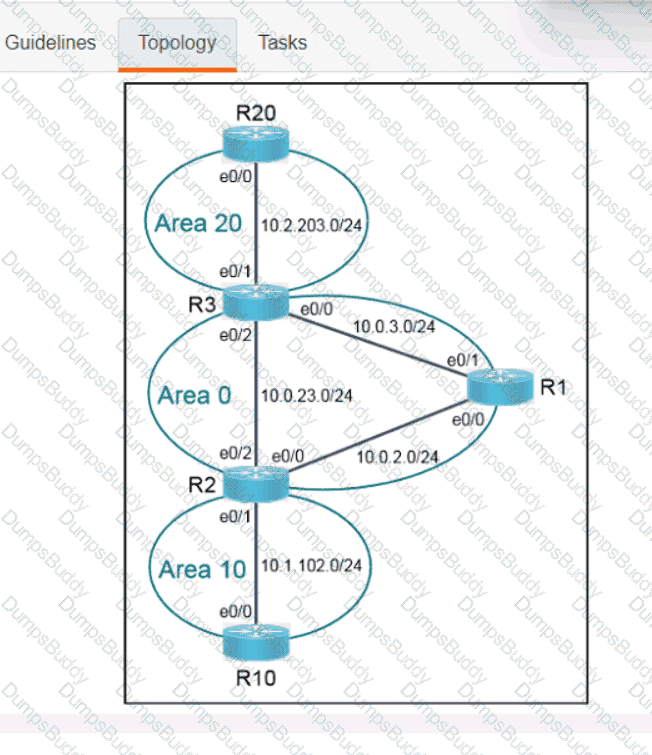
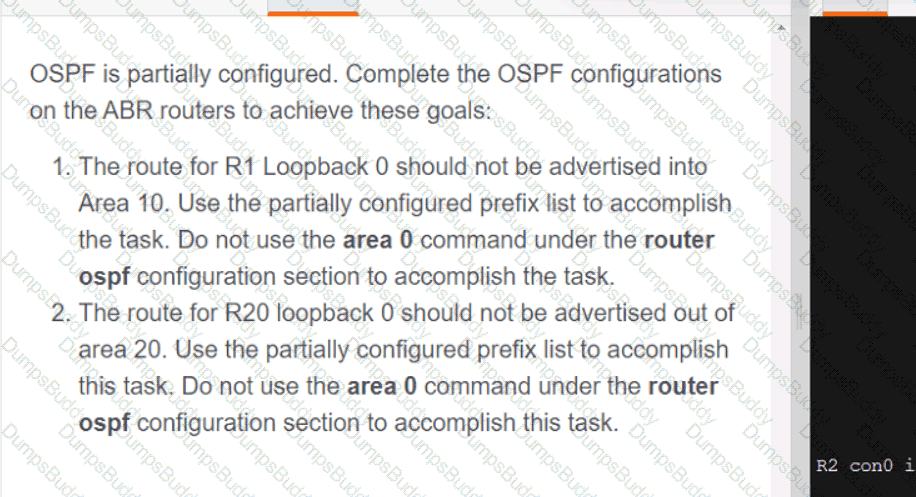
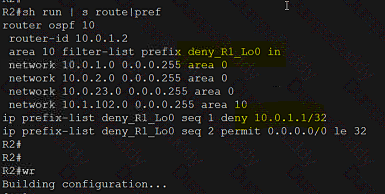
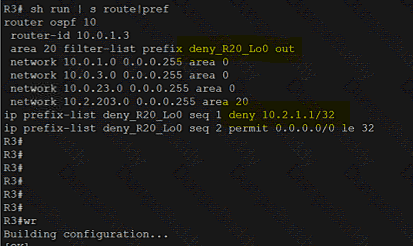
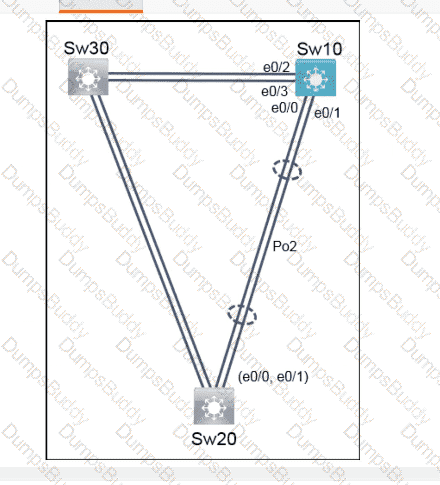
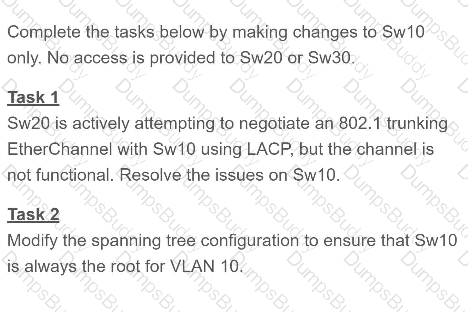
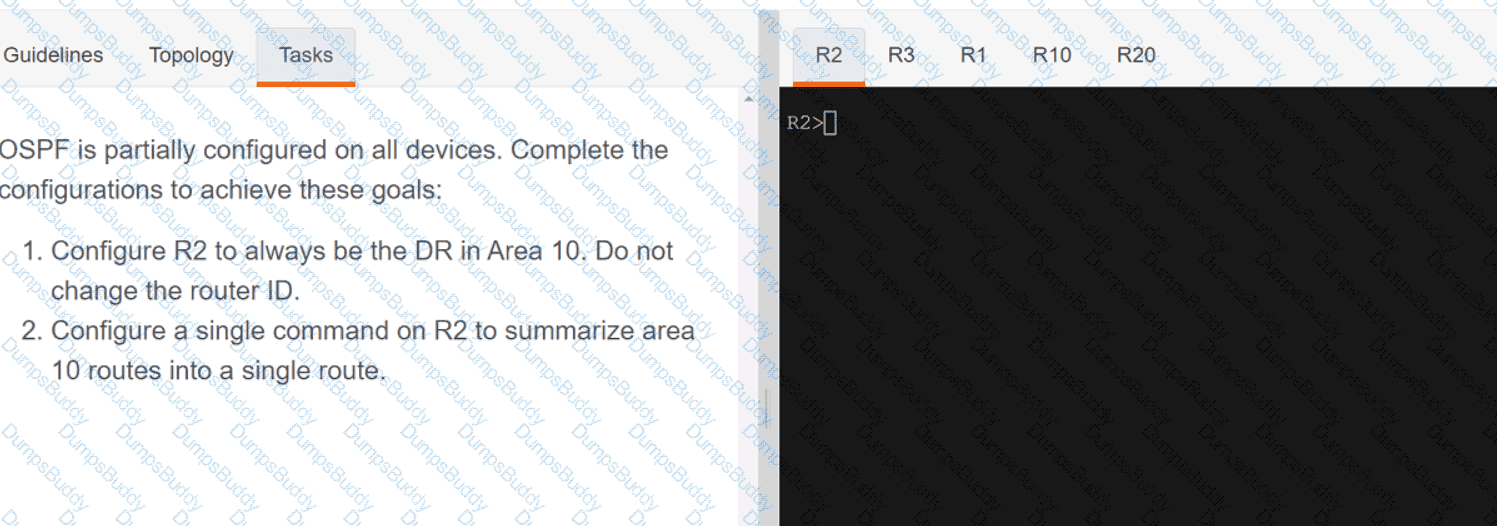
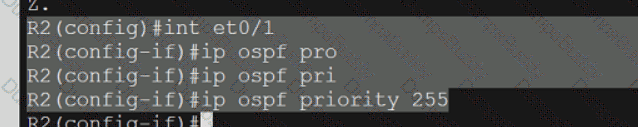
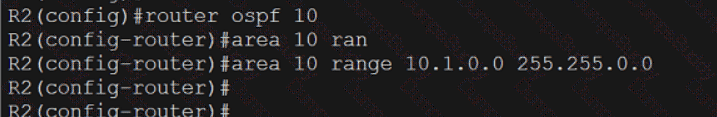
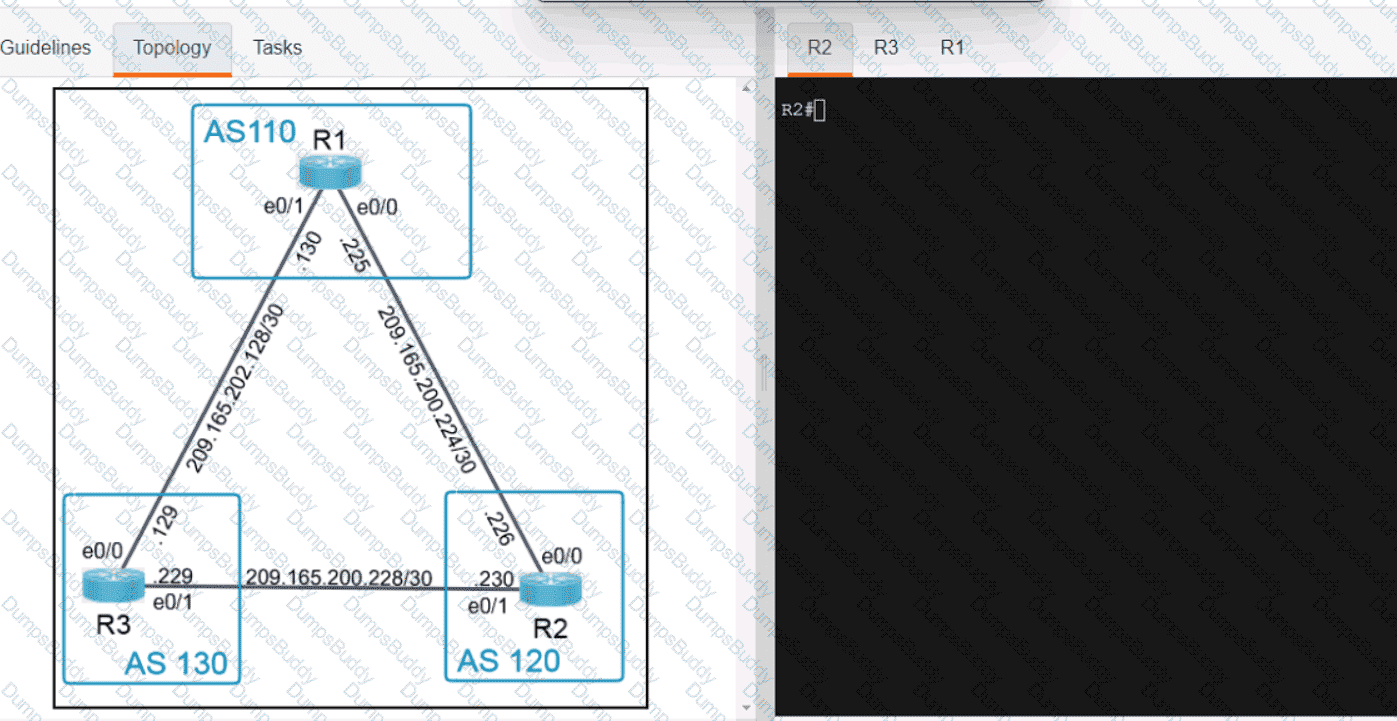
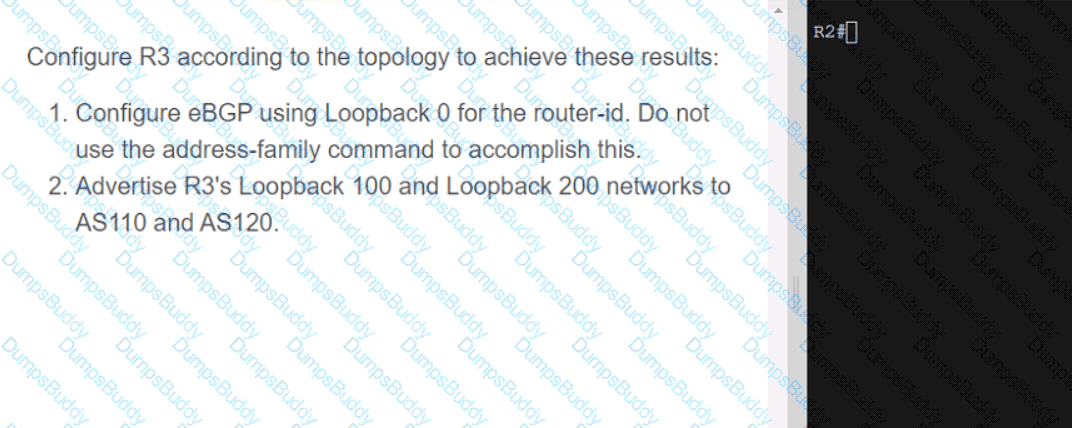
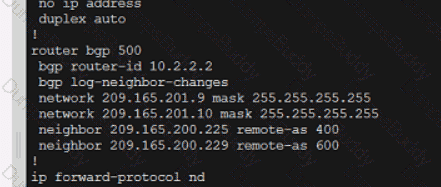
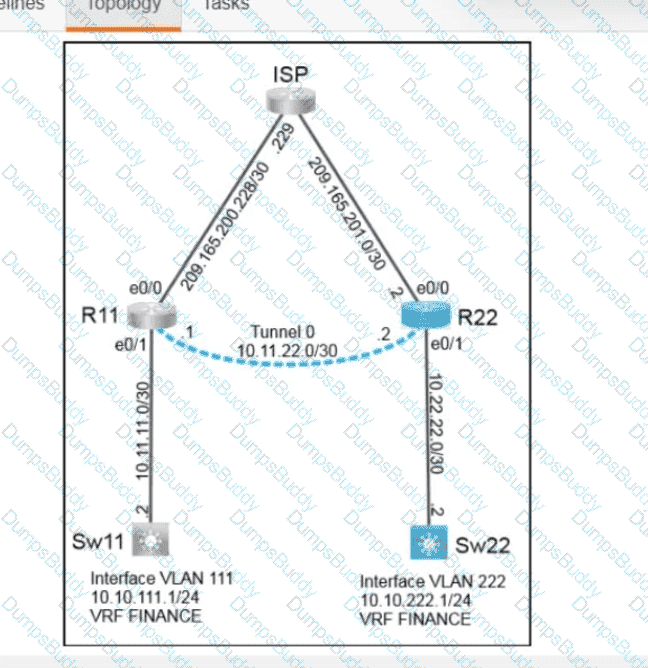
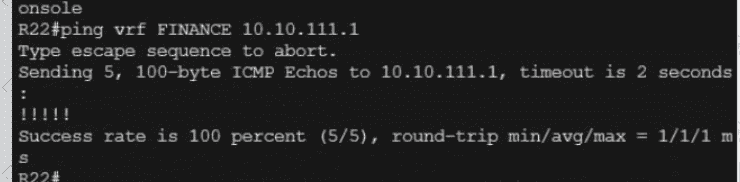
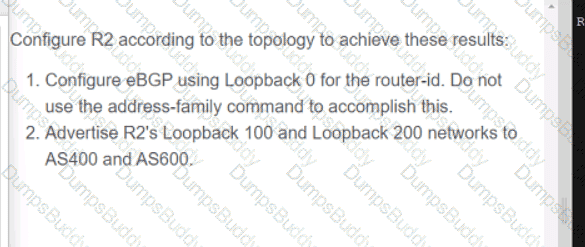
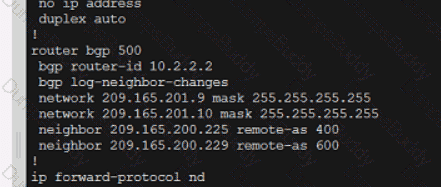
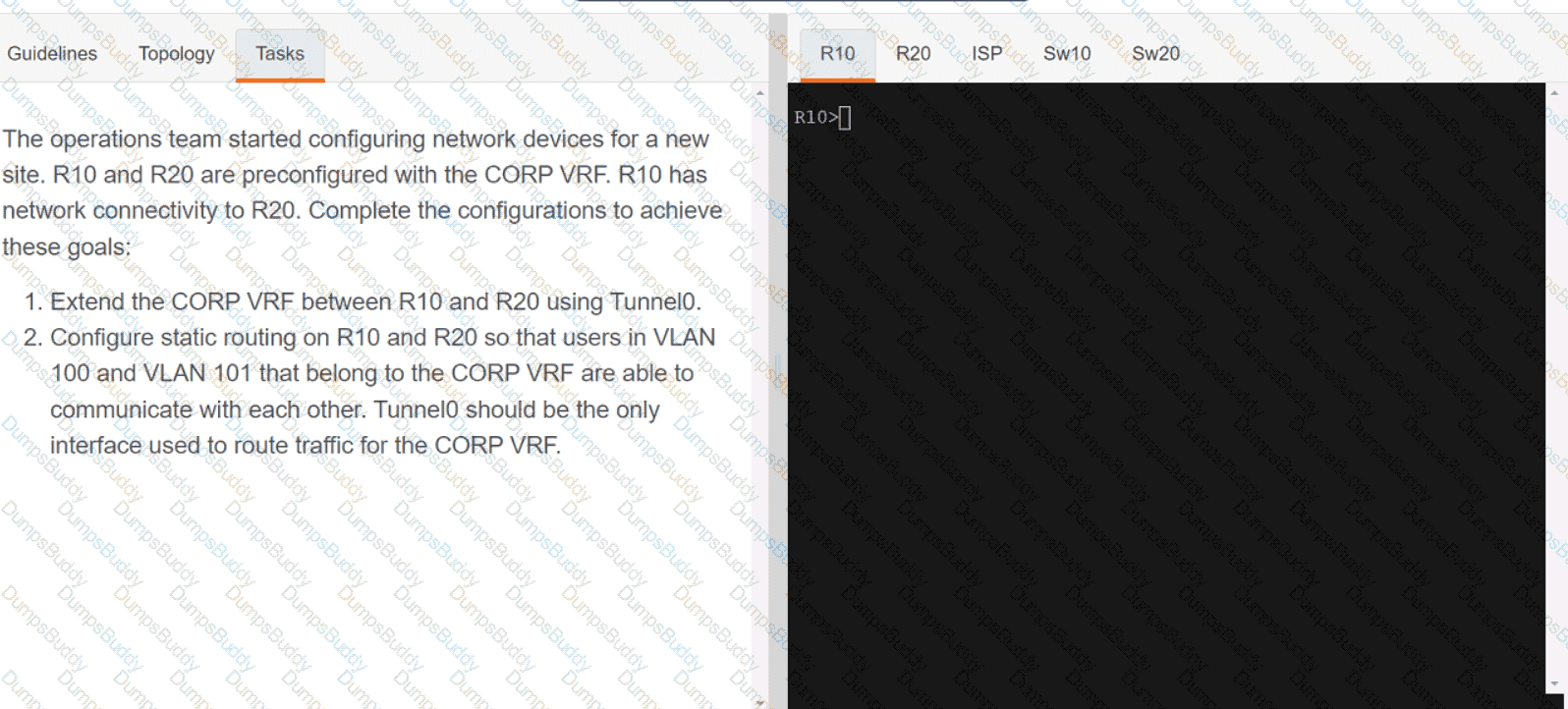
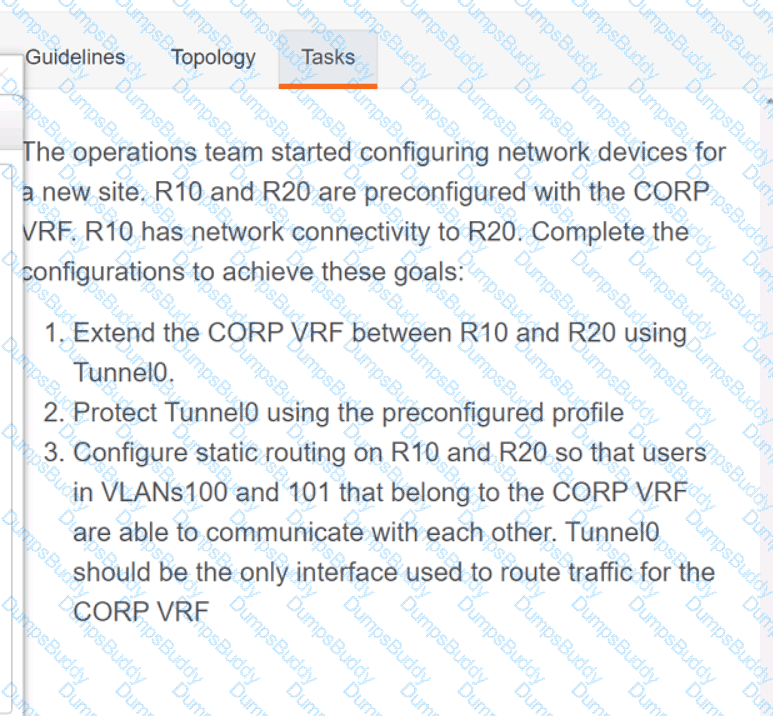
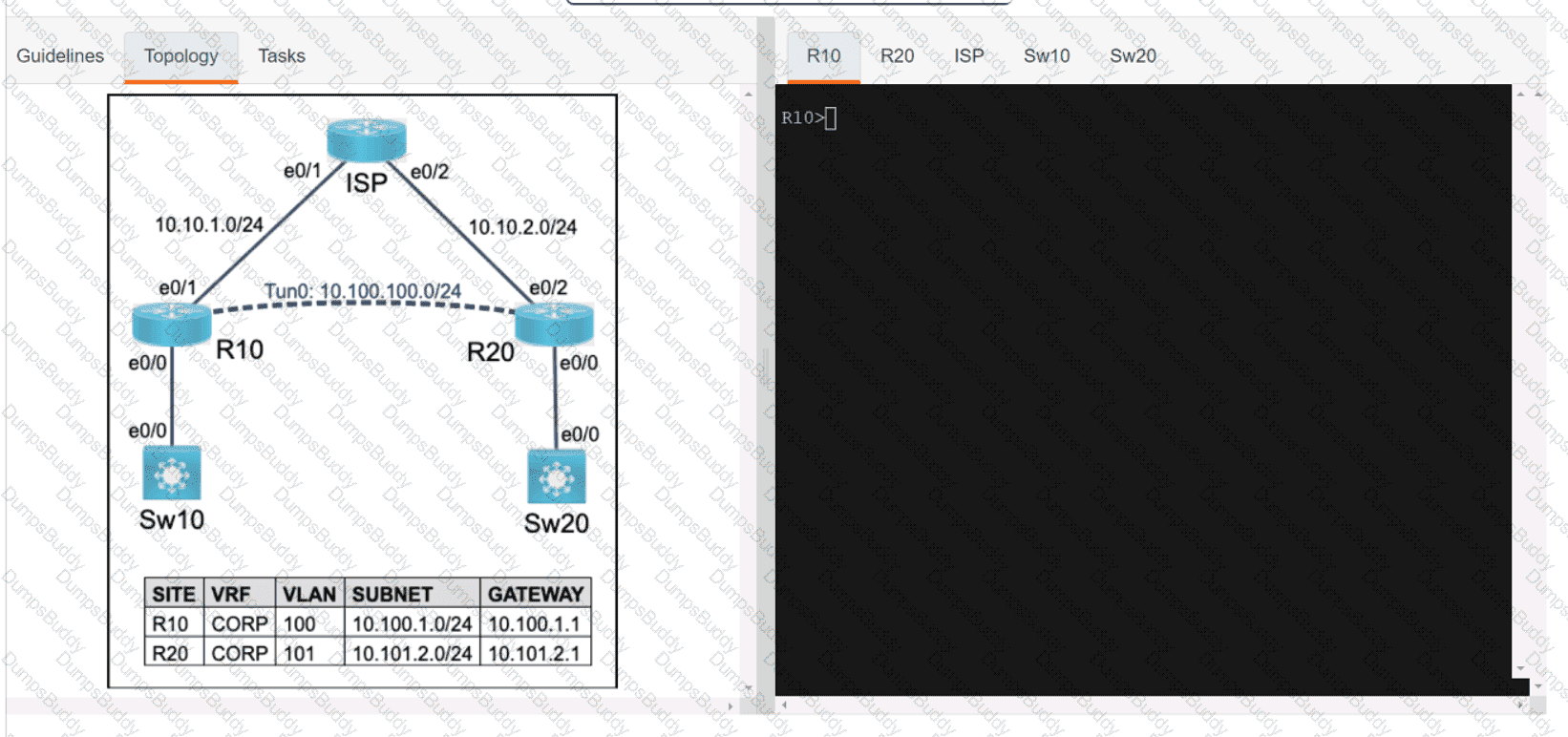
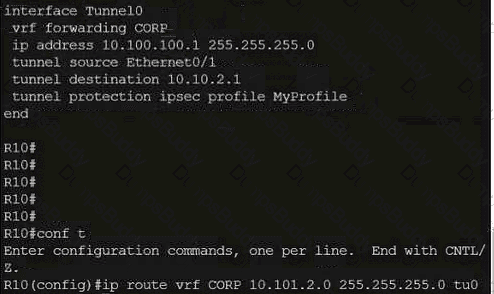
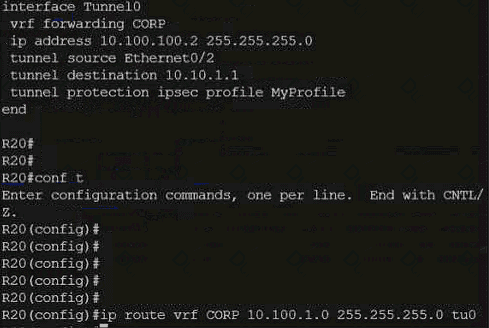
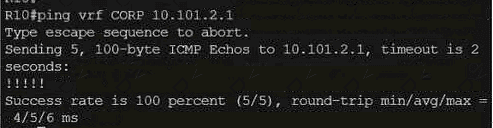
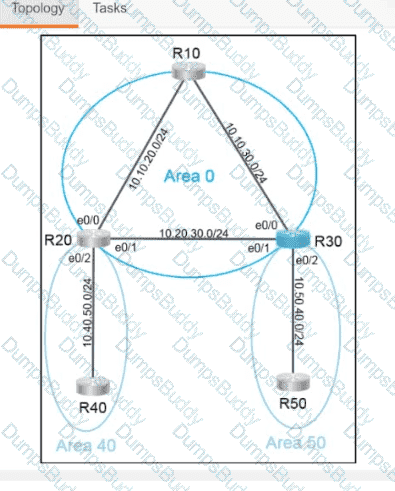
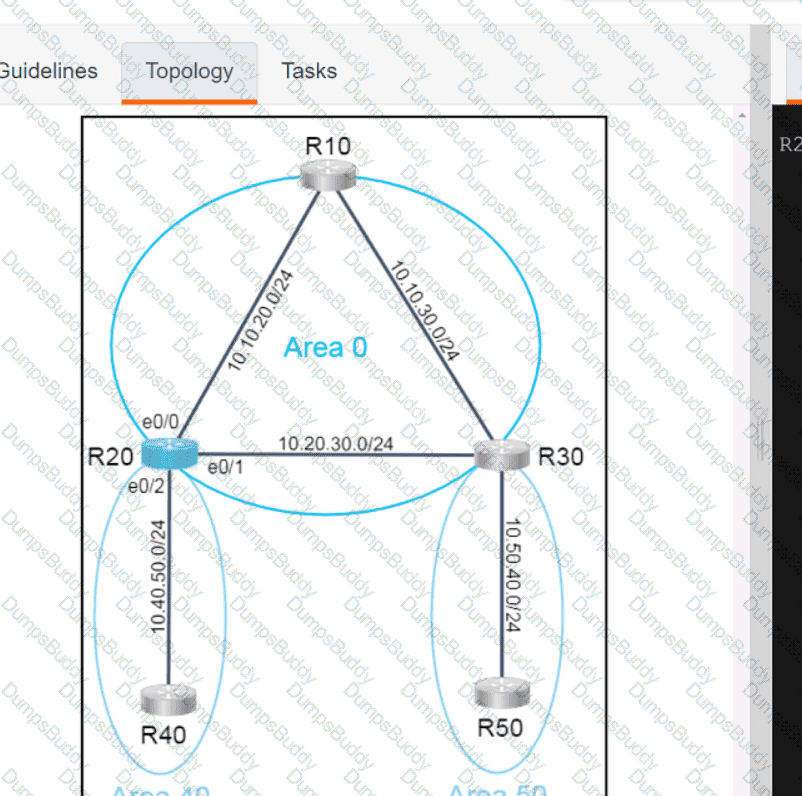
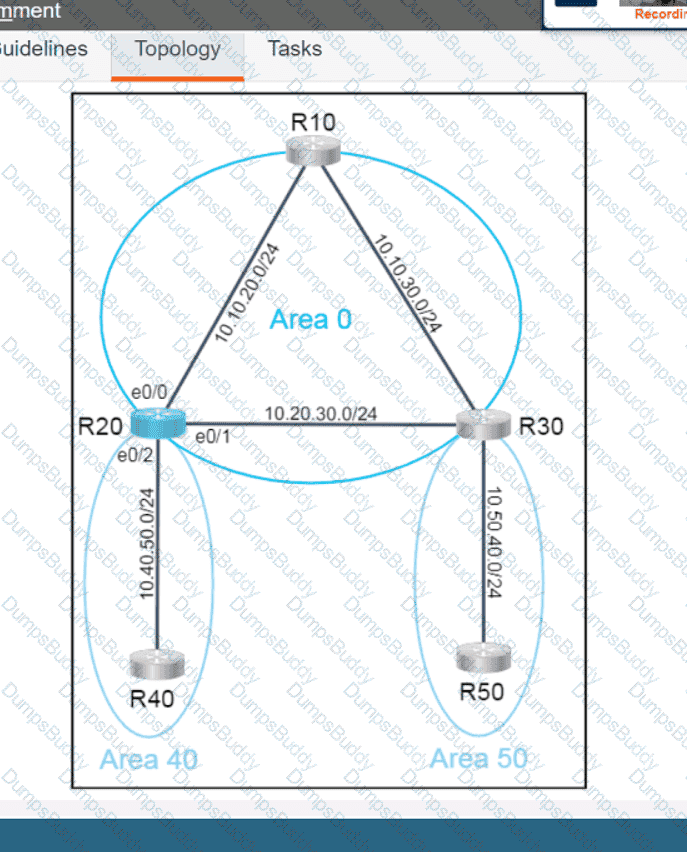
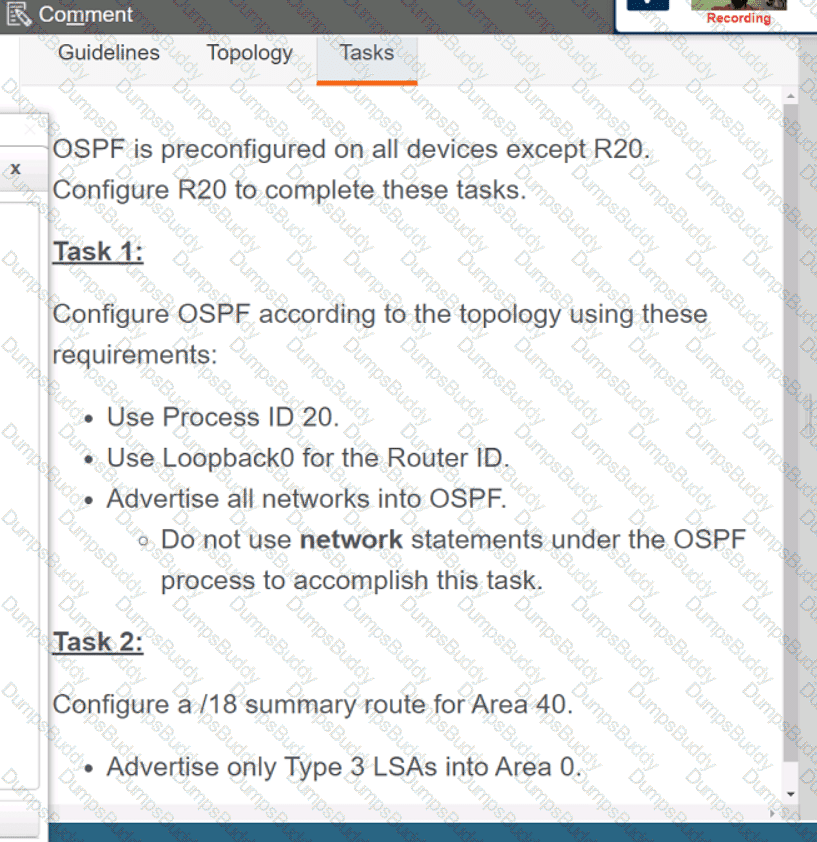
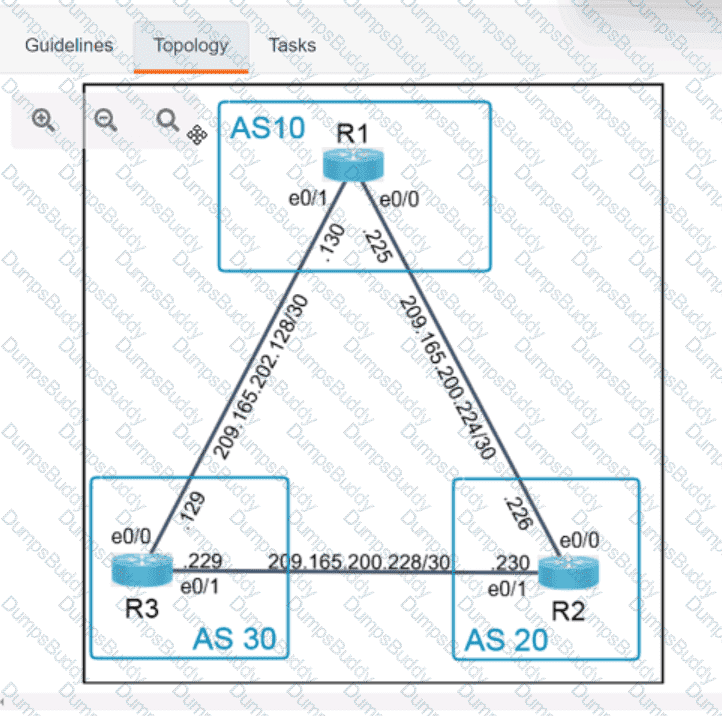
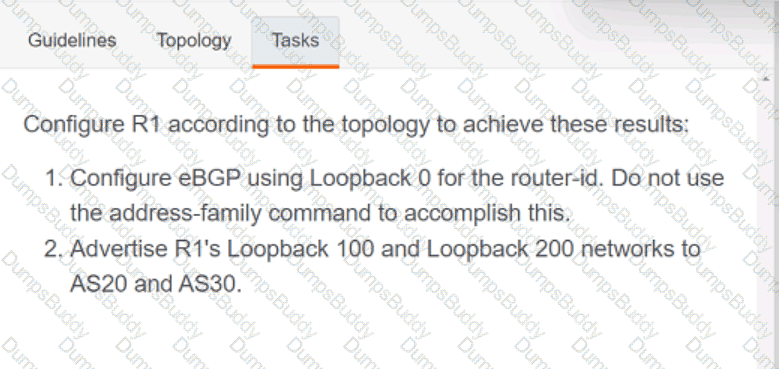
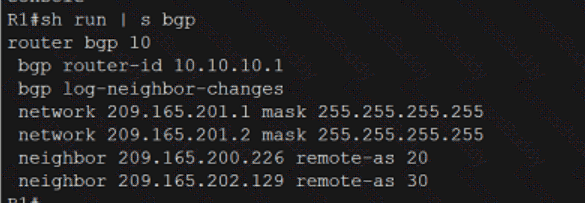
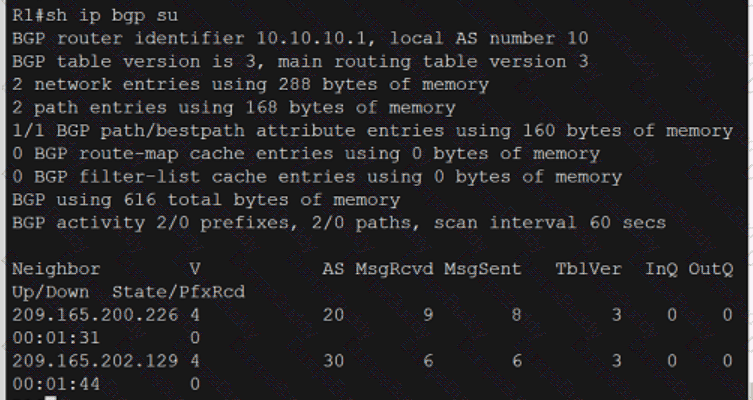
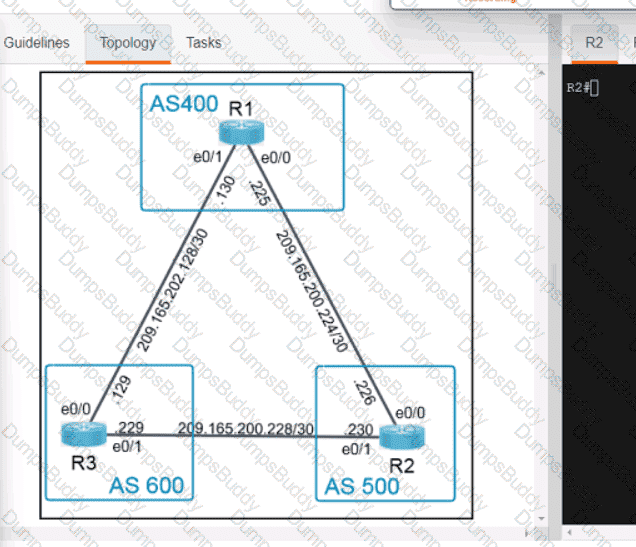
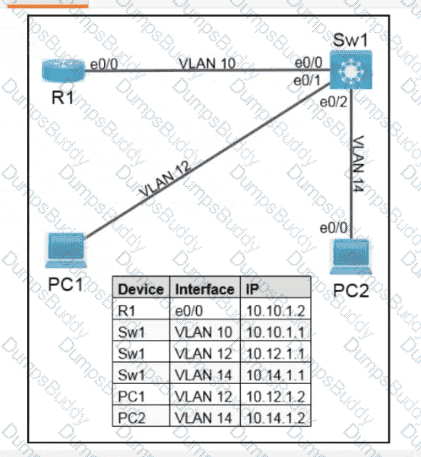
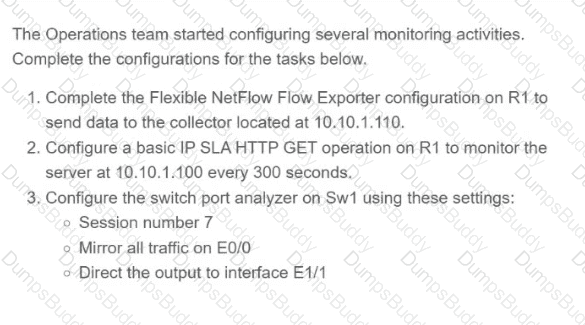
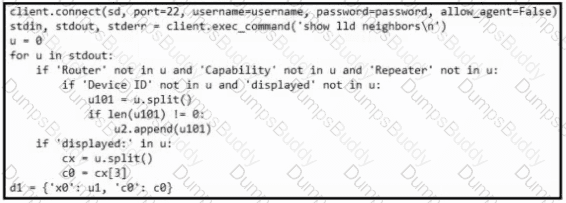
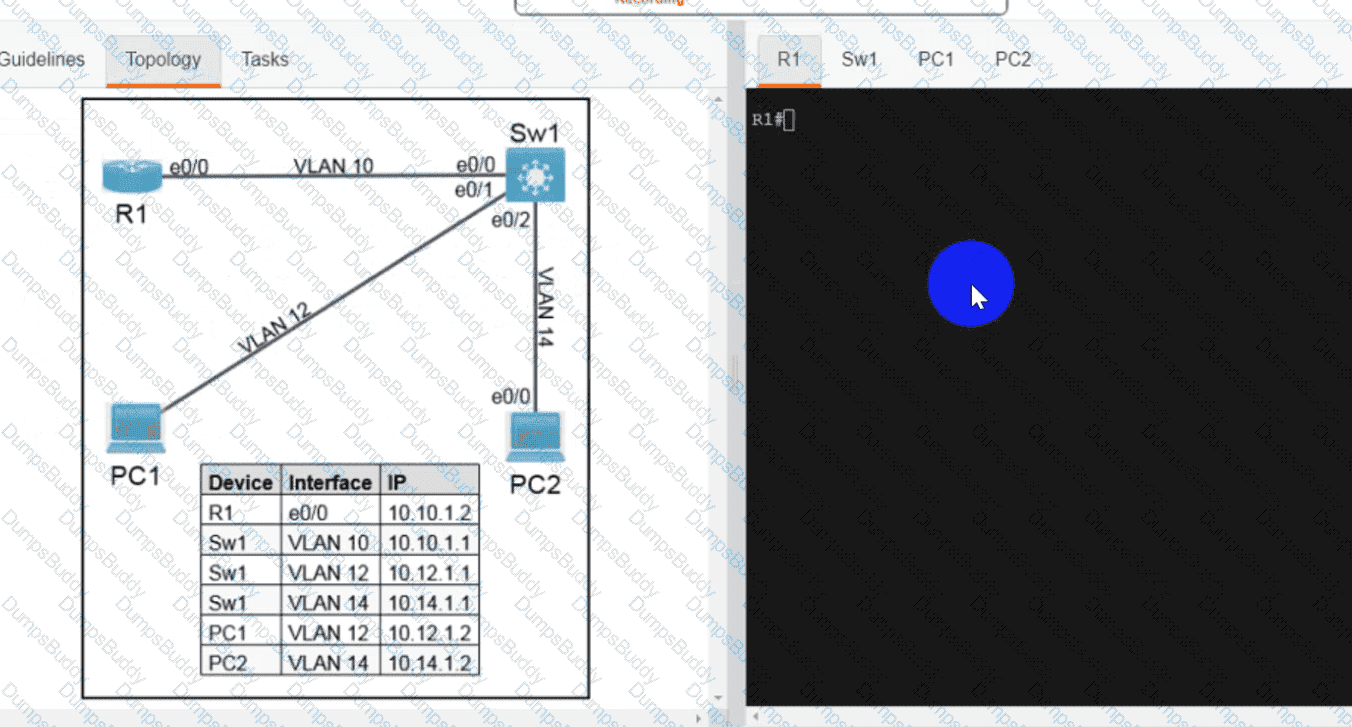
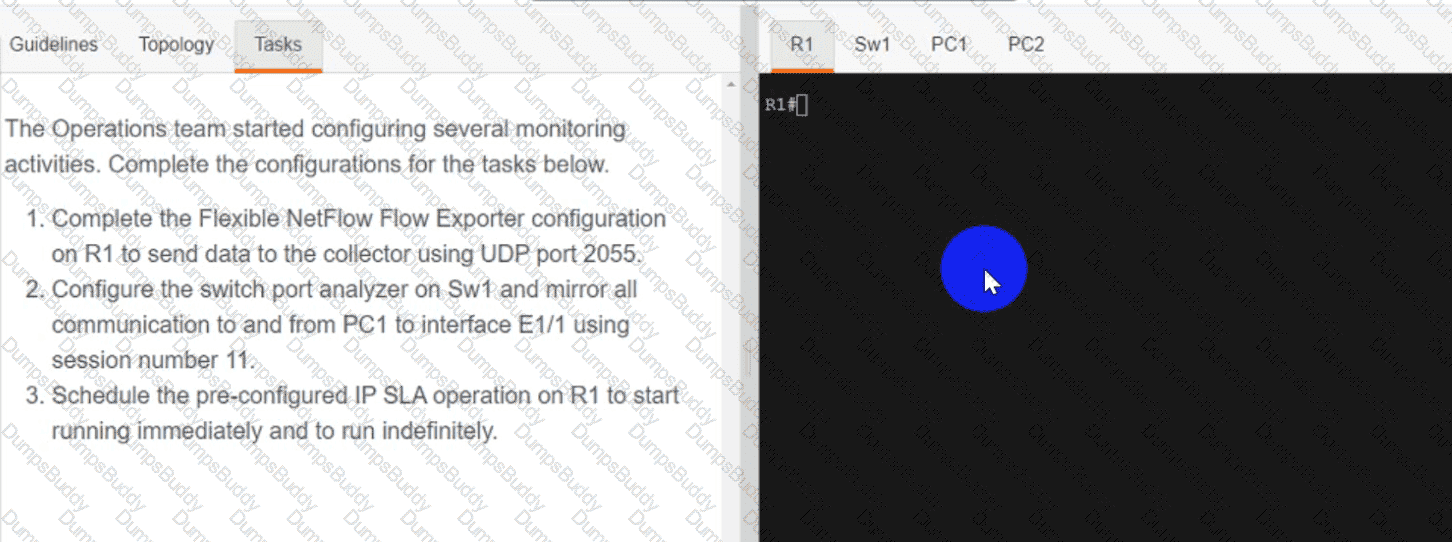
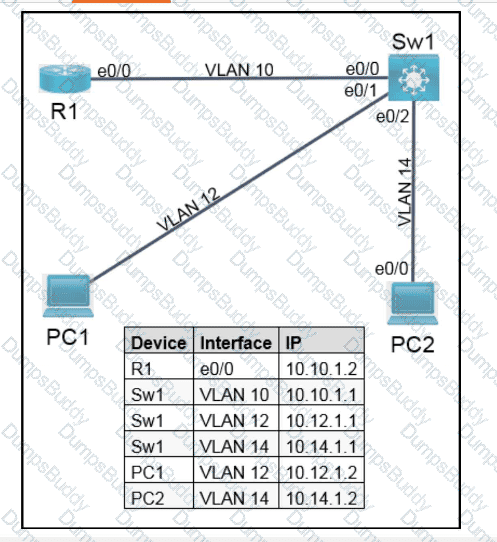
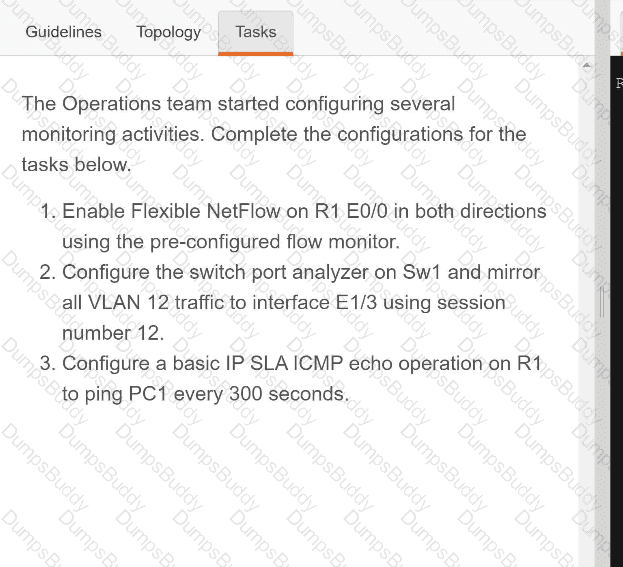
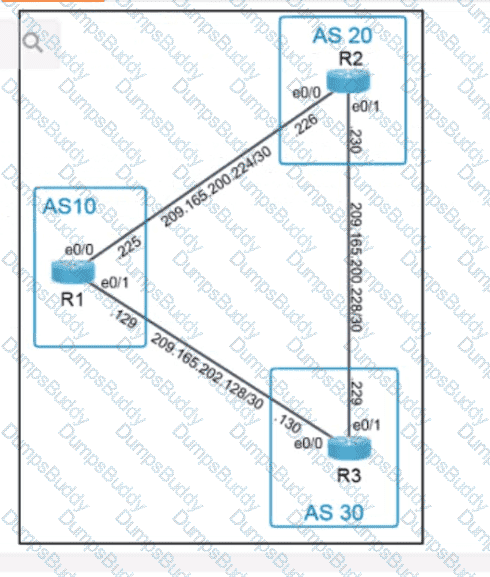
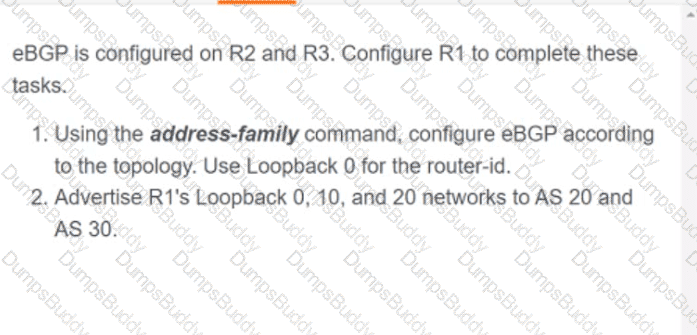
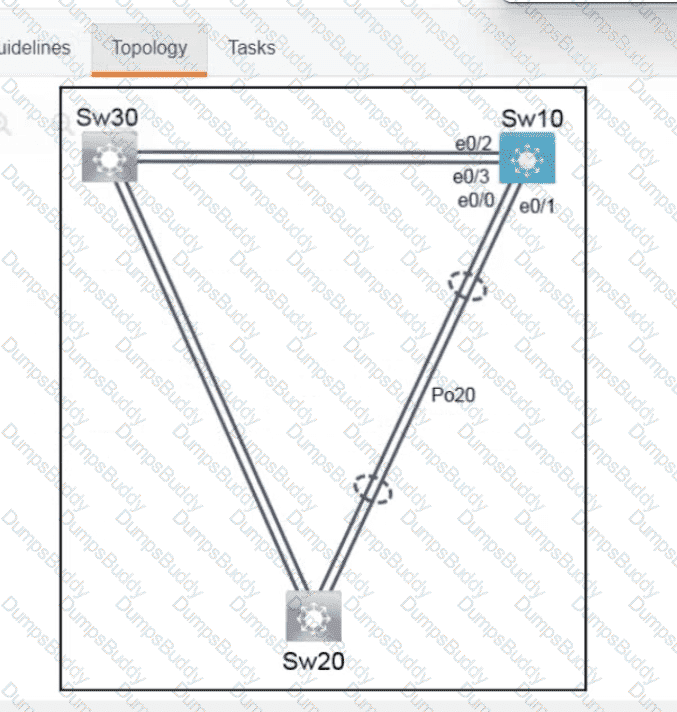
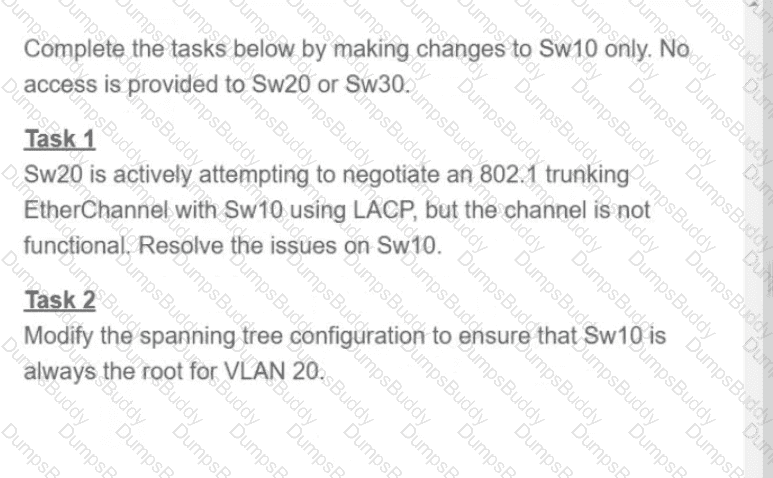
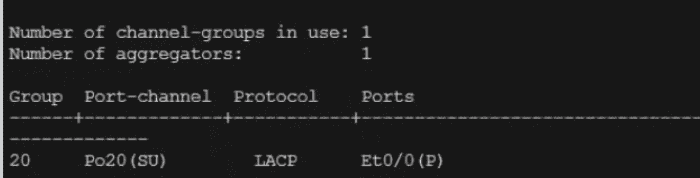
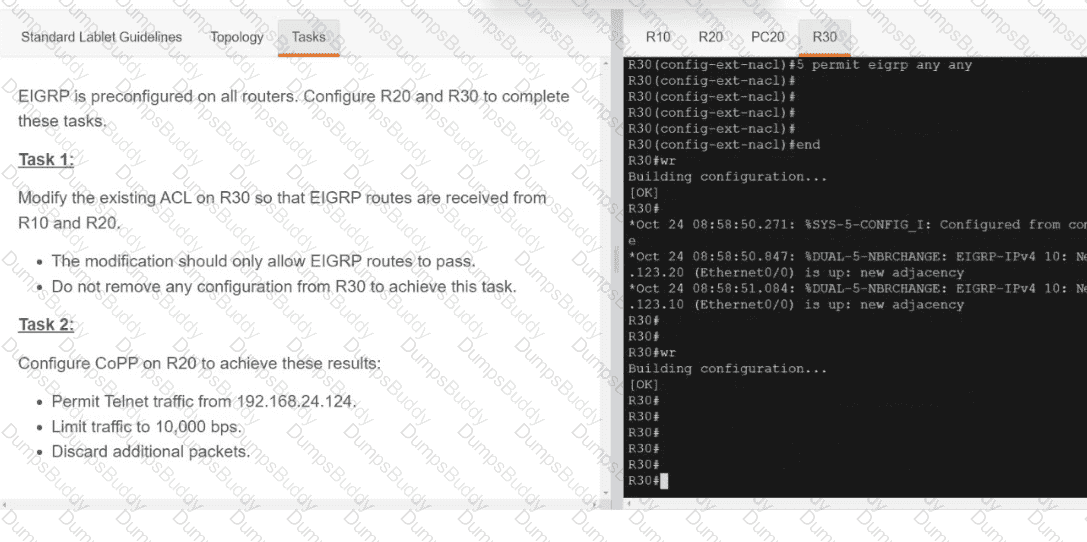
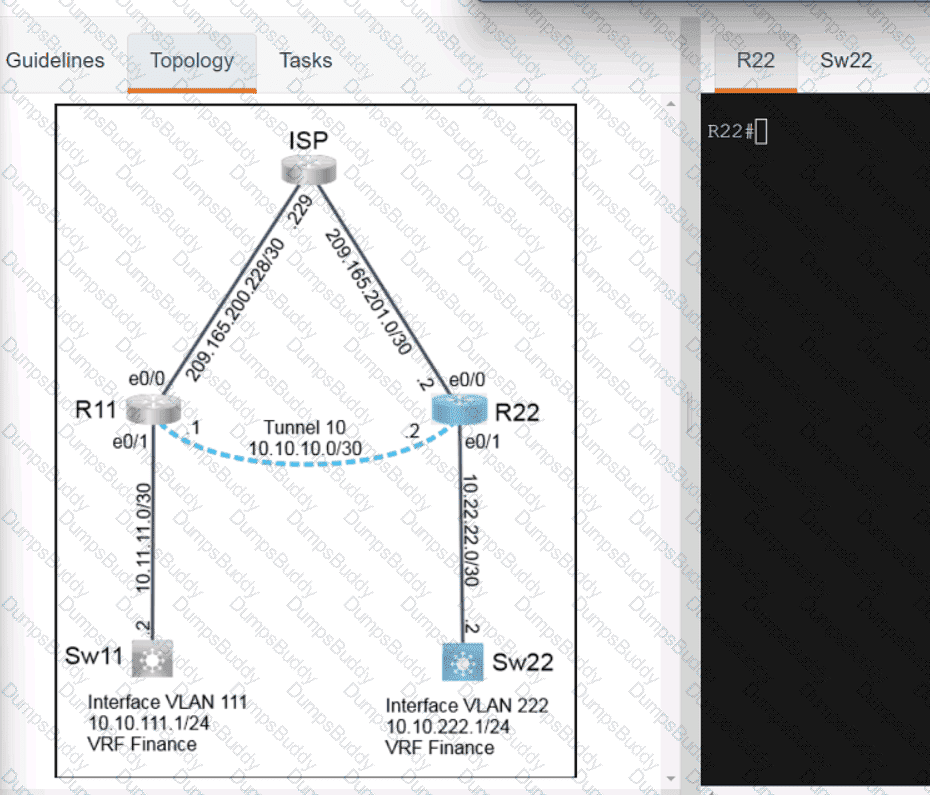
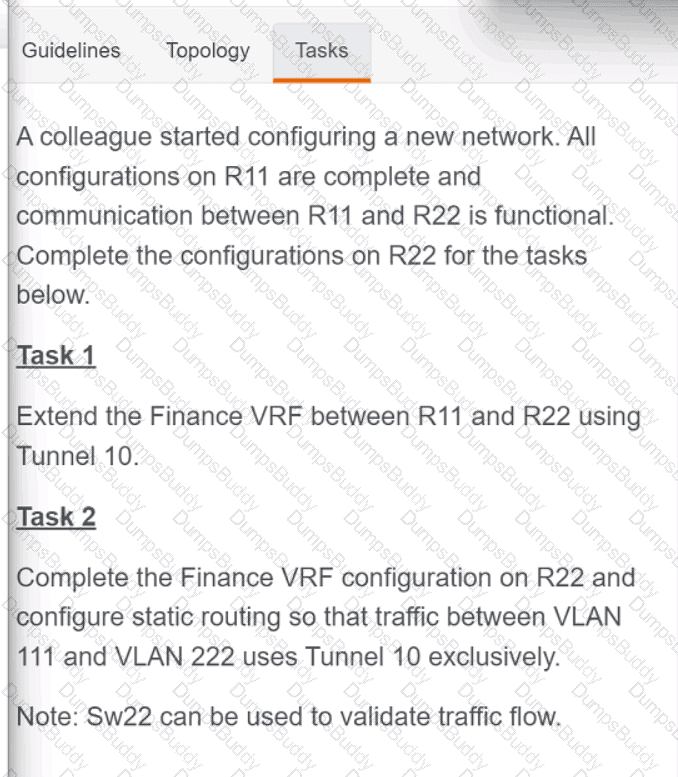
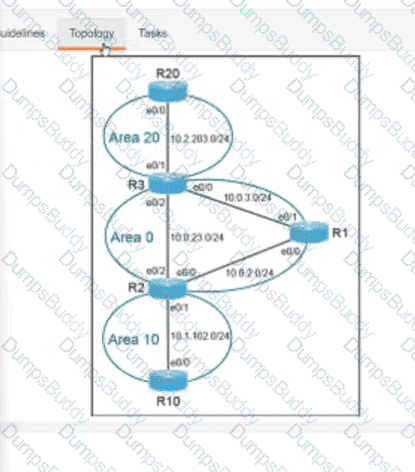
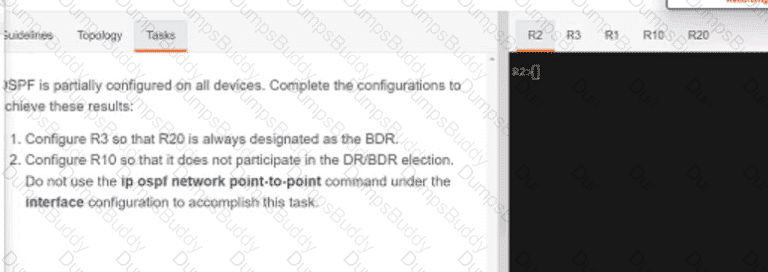
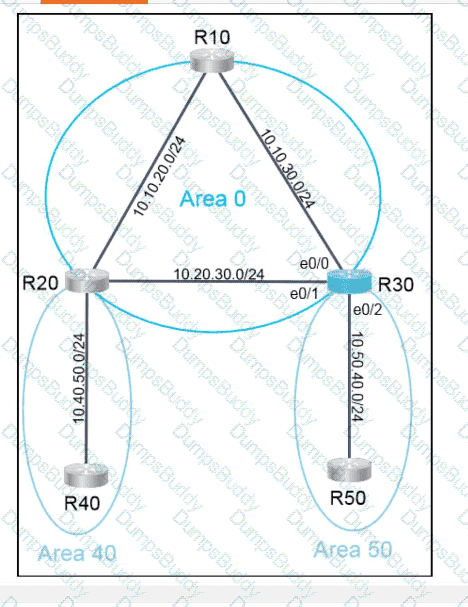
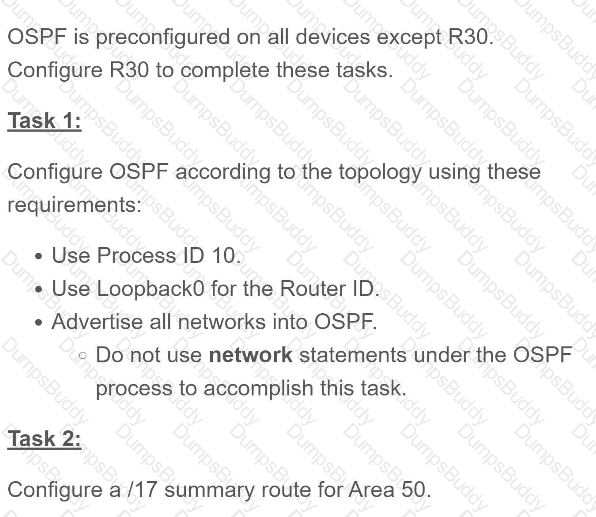
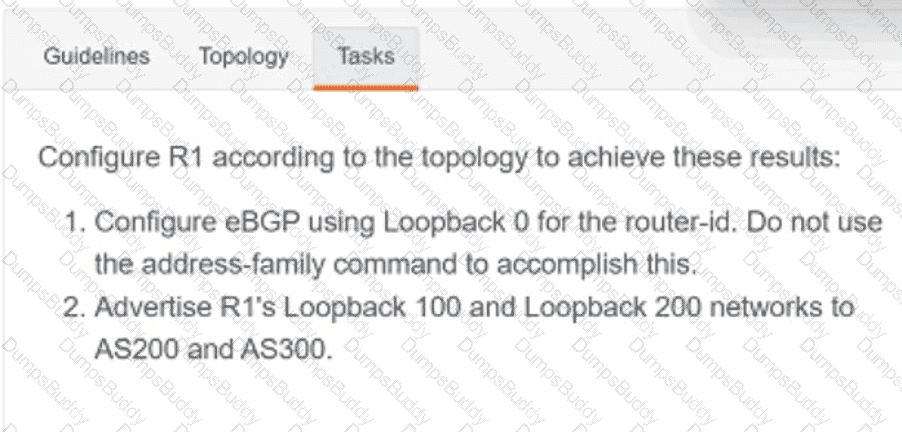
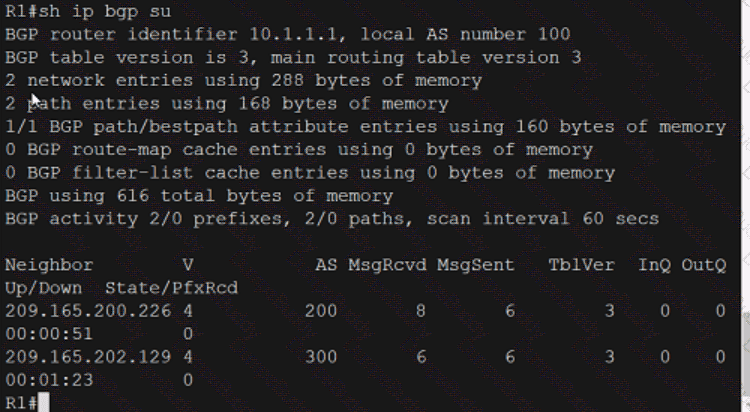
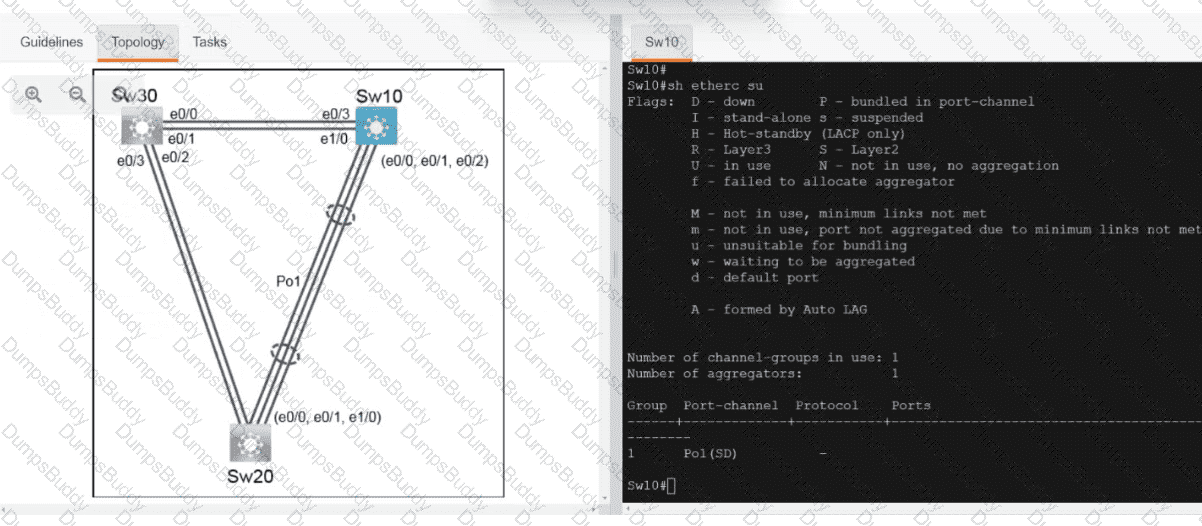
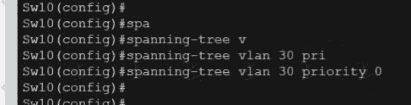
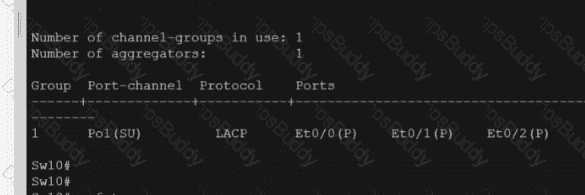
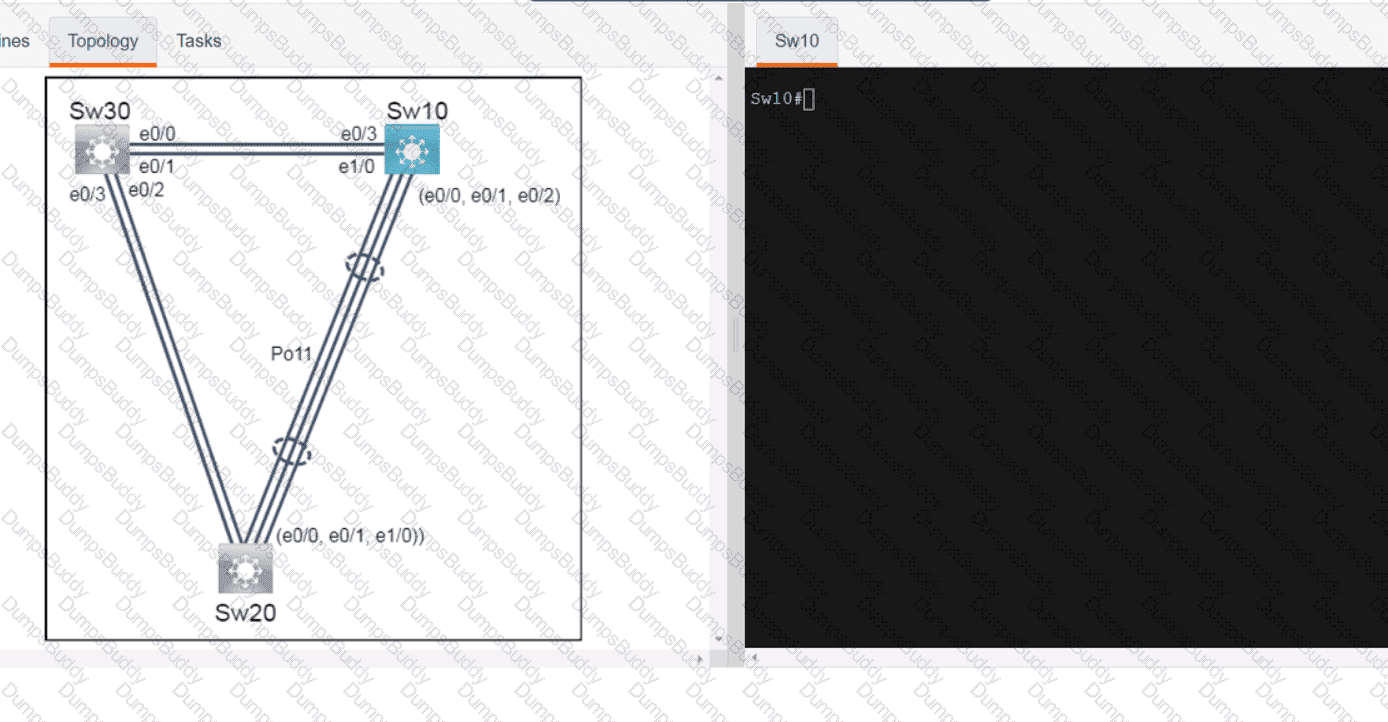
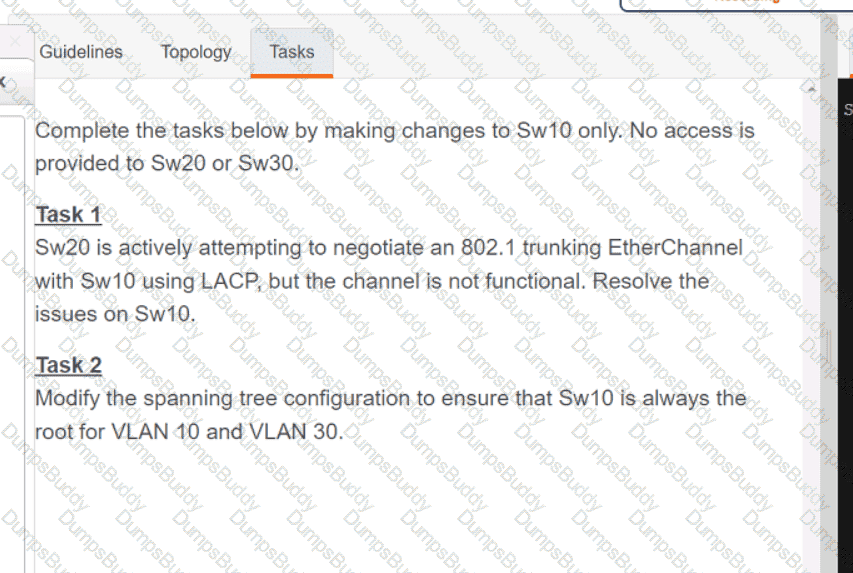
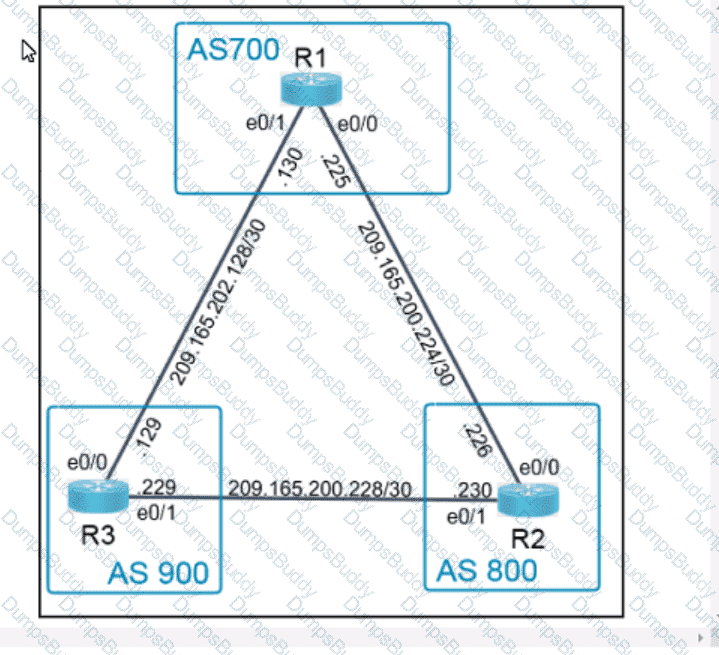
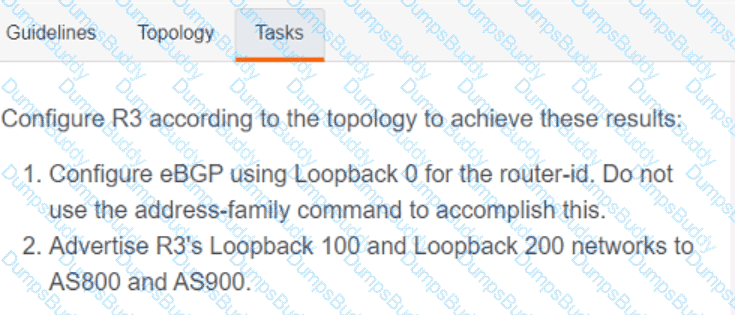
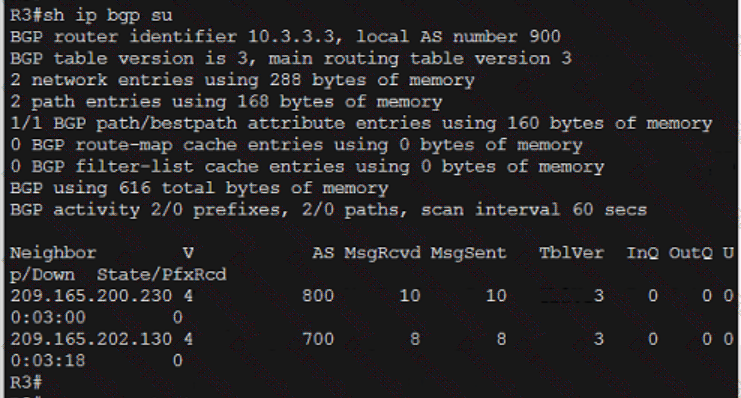
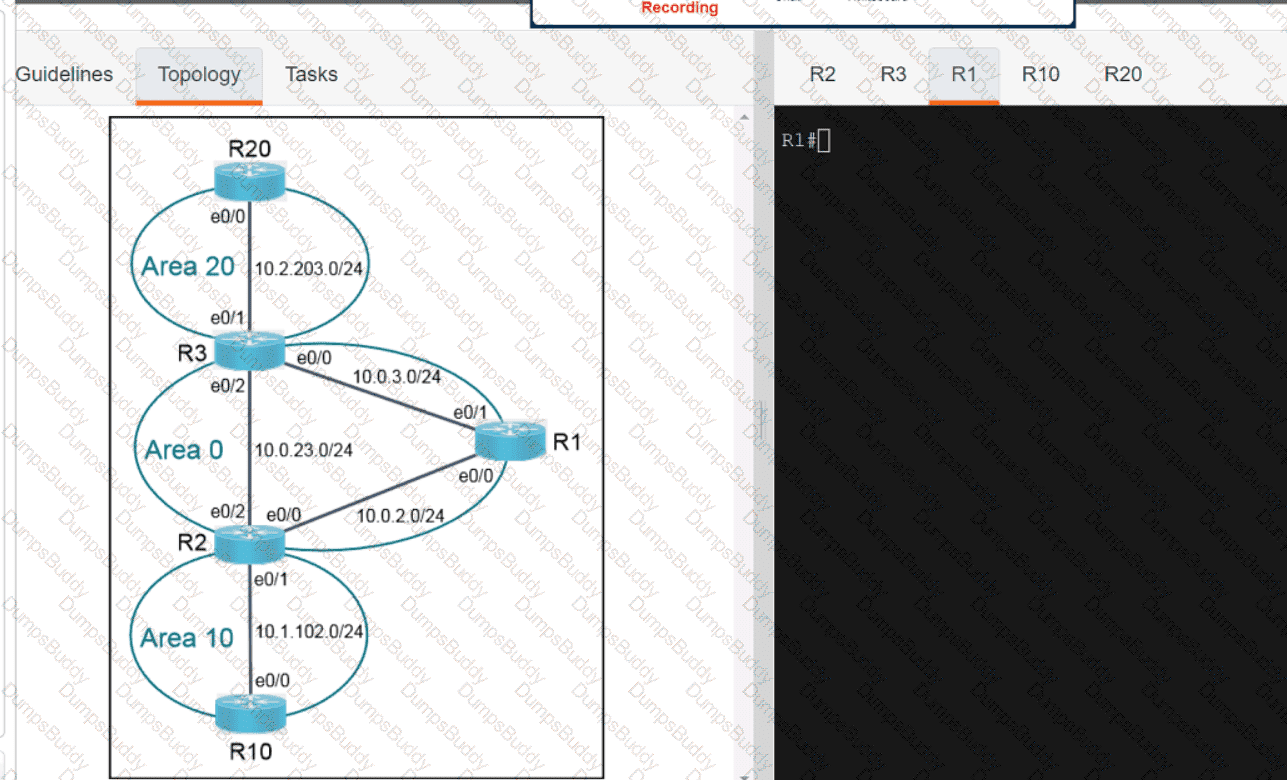
Refer to the exhibit.
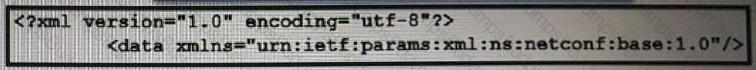
What does the error message relay to the administrator who is trying to configure a Cisco IOS device?
Which RF value represents the decline of the RF signal amplitude over a given distance"?
A company recently decided to use RESTCONF instead of NETCONF. and many of their NETCONF scripts contain the operation
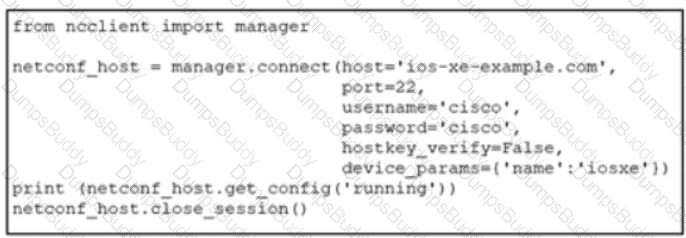
Refer to lhe exhibit. An engineer deploys a script to retrieve the running configuration from a NETCONF-capable CiscoIOSXE device that Is configured with default settings. The script fails. Which configuration must be applied to retrieve the configuration using NETCONF?
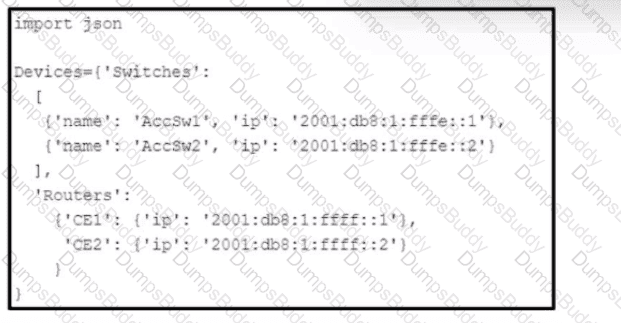
Refer to the exhibit. Which Python snippet stores the data structure of the device in JSON format?

Refer to the exhibit. POSTMAN is showing an attempt to retrieve network device information from Cisco Catalyst Center (formerly DNA Center) API. What is the issue?
In a Cisco SD-WAN solution, which two functions are performed by OMP? (Choose two.)
Which security feature does stateless authentication and authorization use for REST API calls?
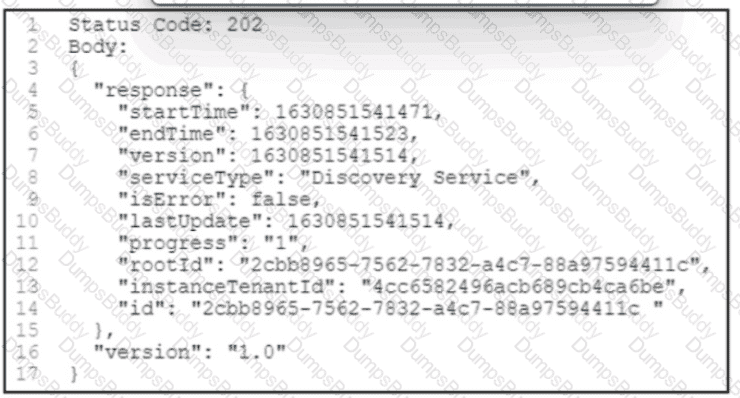
Refer to the exhibit. A POST /discovery request spawns an asynchronous task. After querying for more information about the task, the Cisco DNA Center platform returns the REST API response. What is the status of the discovery task?
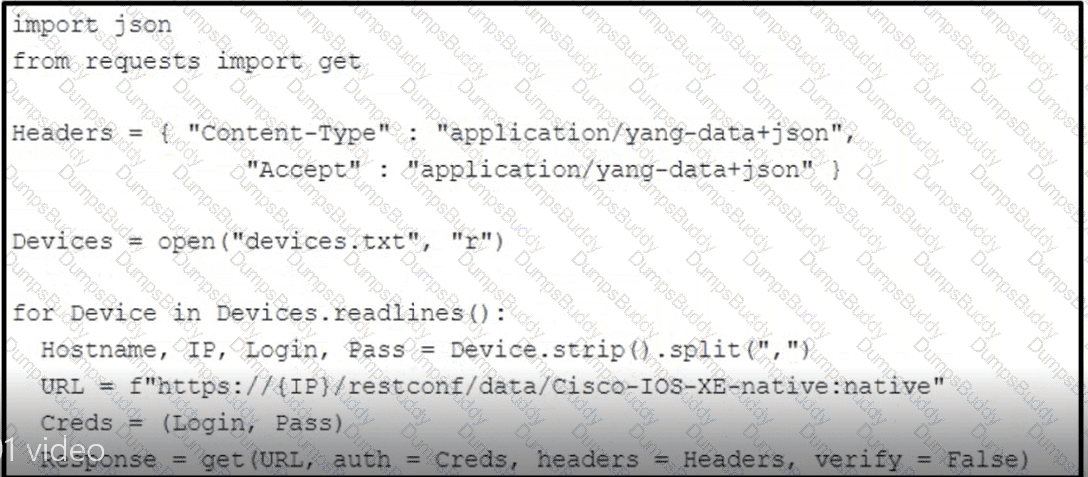
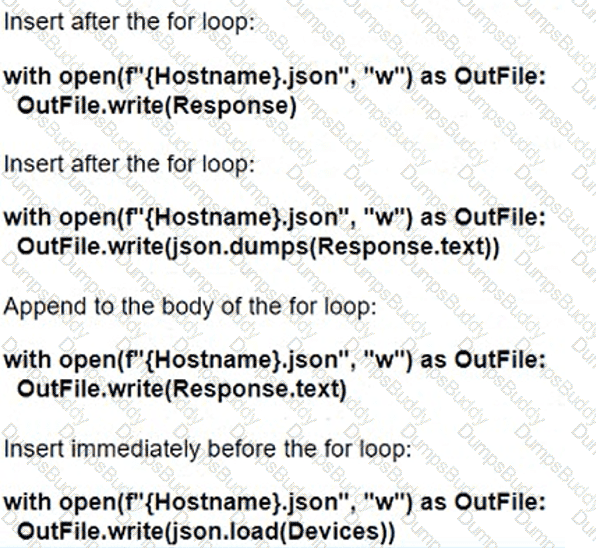
Refer to the exhibit. How should the script be completed so that each device configuration is saved into a JSON-formatted file under the device name?
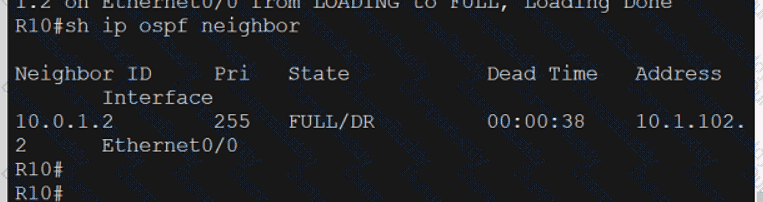
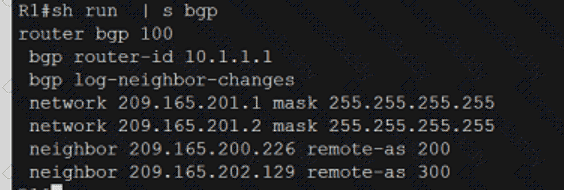
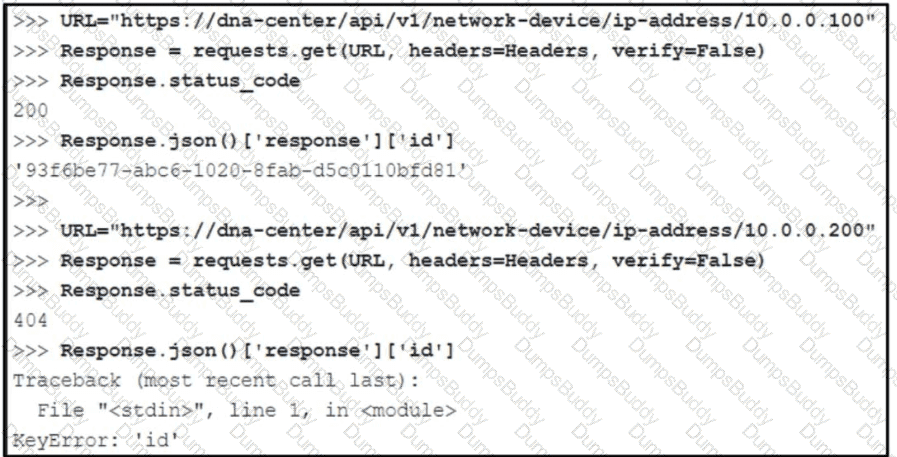
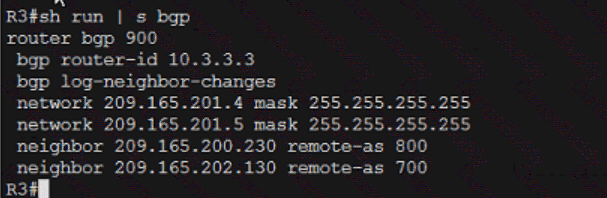
Refer to the exhibit.

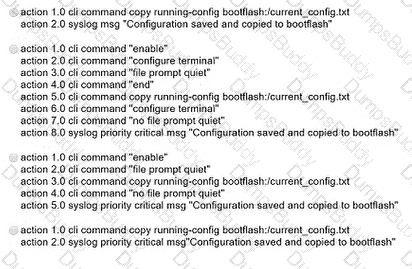
Which EEM script generates a critical-level syslog message and saves a copy of the running configuration to the bootflash when an administrator saves the running configuration to the startup configuration?
An engineer must construct an access list for a Cisco Catalyst 9800 Series WLC that will redirect wireless guest users to a splash page that is hosted on a Cisco ISE server. The Cisco ISE servers are hosted at 10.9.11.141 and 10.1.11.141. Which access list meets the requirements?
Which First Hop Redundancy Protocol maximizes uplink utilization and minimizes the amount of configuration that is necessary?
A response code of 404 is received while using the REST API on Cisco UNA Center to POST to this URI.
/dna/intent/api/v1 /template-programmer/project
What does the code mean?
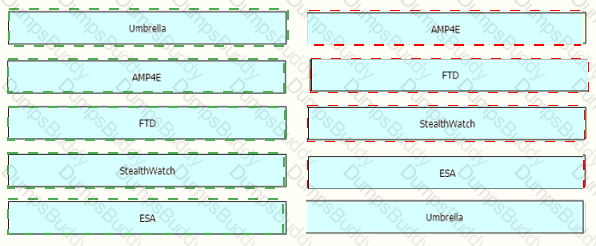
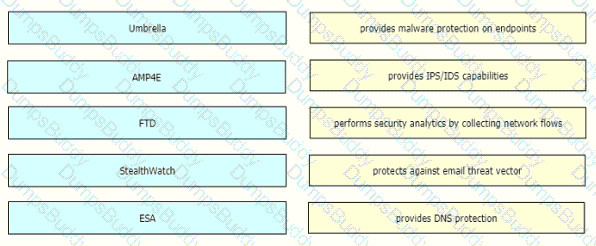
Drag and drop the threat defense solutions from the left onto their descriptions on the right.
Which mechanism is used to protect the confidentiality of sensitive information exchanged over REST APIs?
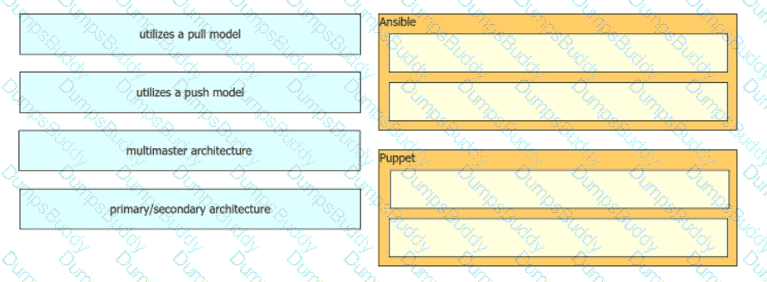
Drag and drop the characteristics from the left onto the orchestration tools they describe on the right.
Which two nodes comprise a collapsed core in a two-tier Cisco SD-Access design? (Choose two.)
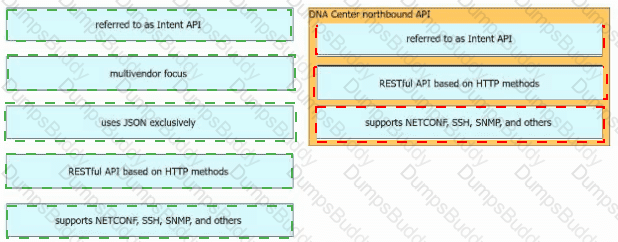
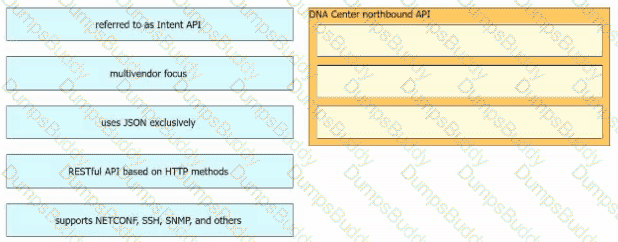
Drag and drop the Cisco Catalyst Center (formerly DNA Center) northbound API characteristics from the left to the right. Not all options are used.
An engineer measures the Wi-Fi coverage at a customer site. The RSSI values are recorded as follows:
•LocationA -72dBm
• Location B:-75 dBm
• Location C; -65 dBm
• Location D -80 dBm
Which two statements does the engineer use to explain these values to the customer? (Choose two.)
A customer has several small branches and wants to deploy a Wi-Fi solution with local management using CAPWAP. Which deployment model meets this requirement?
Which two southbound interfaces originate from Cisco Catalyst Center (formerly DNA Center) and terminate at fabric underlay switches'? (Choose two.)
What is calculated using the numerical values of the transmitter power level, cable loss, and antenna gain?
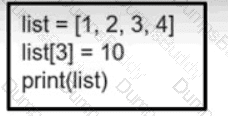
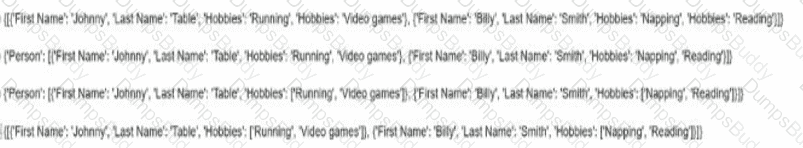
Refer to the exhibit. What is the value of the variable list after the code is run?
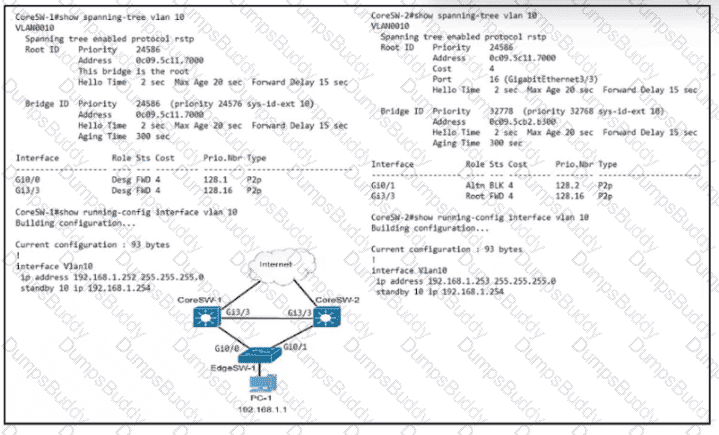
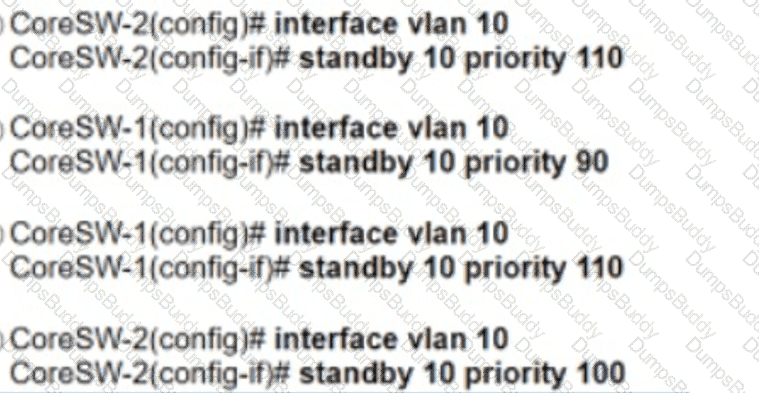
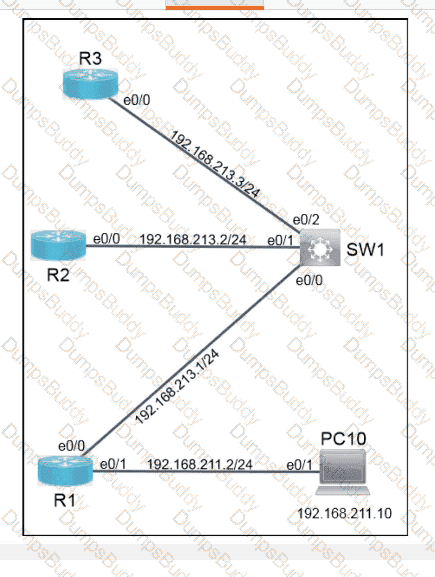
Refer to the exhibit. Which configuration causes the traffic from PC-1 to the internet to use the link between CoreSW-1 and CoreSW-2 when both switches are up?