156-315.81 Check Point Certified Security Expert R81.20 ( 156-315.81.20 ) Questions and Answers
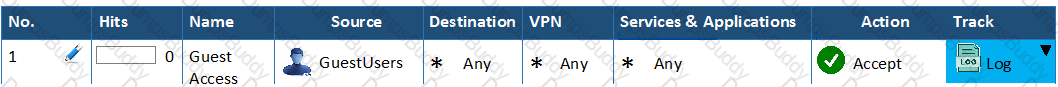
The “Hit count” feature allows tracking the number of connections that each rule matches. Will the Hit count feature work independently from logging and Track the hits if the Track option is set to “None”?
In the Check Point Security Management Architecture, which component(s) can store logs?
What is the recommended way to have a redundant Sync connection between the cluster nodes?
Kofi, the administrator of the ALPHA Corp network wishes to change the default Gaia WebUI Portal port number currently set on the default HTTPS port. Which CLISH commands are required to be able to change this TCP port?
You have created a rule at the top of your Rule Base to permit Guest Wireless access to the Internet. However, when guest users attempt to reach the Internet, they are not seeing the splash page to accept your Terms of Service, and cannot access the Internet. How can you fix this?
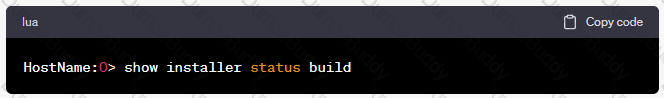
Alice wants to upgrade the current security management machine from R80.40 to R81.20 and she wants to check the Deployment Agent status over the GAIA CLISH. Which of the following GAIACLISH command is true?
Name the file that is an electronically signed file used by Check Point to translate the features in the license into a code?
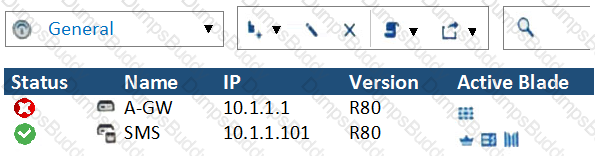
John is using Management HA. Which Security Management Server should he use for making changes?
What feature allows Remote-access VPN users to access resources across a site-to-site VPN tunnel?
There are 4 ways to use the Management API for creating host object with R81 Management API. Which one is NOT correct?
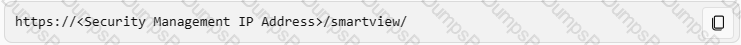
Where you can see and search records of action done by R81 SmartConsole administrators?
You have successfully backed up Check Point configurations without the OS information. What command would you use to restore this backup?
To fully enable Dynamic Dispatcher with Firewall Priority Queues on a Security Gateway, run the following command in Expert mode then reboot:
An administrator is creating an IPsec site-to-site VPN between his corporate office and branch office. Both offices are protected by Check Point Security Gateway managed by the same Security Management Server. While configuring the VPN community to specify the pre-shared secret the administrator found that the check box to enable pre-shared secret and cannot be enabled.
Why does it not allow him to specify the pre-shared secret?
In a Client to Server scenario, which inspection point is the first point immediately following the tables and rule base check of a packet coming from outside of the network?
CPM process stores objects, policies, users, administrators, licenses and management data in a database. The database is:
When requiring certificates for mobile devices, make sure the authentication method is set to one of the following, Username and Password, RADIUS or ________.
Automatic affinity means that if SecureXL is running, the affinity for each interface is automatically reset every
Fill in the blank: The command ___________________ provides the most complete restoration of a R81 configuration.
According to out of the box SmartEvent policy, which blade will automatically be correlated into events?
Which of the following statements about Site-to-Site VPN Domain-based is NOT true?
Using mgmt_cli, what is the correct syntax to import a host object called Server_1 from the CLI?
SmartConsole R81 requires the following ports to be open for SmartEvent R81 management:
The Firewall Administrator is required to create 100 new host objects with different IP addresses. What API command can he use in the script to achieve the requirement?
On R81.20 when configuring Third-Party devices to read the logs using the LEA (Log Export API) the default Log Server uses port:
Which is the least ideal Synchronization Status for Security Management Server High Availability deployment?
Selecting an event displays its configurable properties in the Detail pane and a description of the event in the Description pane. Which is NOT an option to adjust or configure?
SSL Network Extender (SNX) is a thin SSL VPN on-demand client that is installed on the remote user’s machine via the web browser. What are the two modes of SNX?
Check Pont Central Deployment Tool (CDT) communicates with the Security Gateway / Cluster Members over Check Point SIC _______ .
You are working with multiple Security Gateways enforcing an extensive number of rules. To simplify security administration, which action would you choose?
If you needed the Multicast MAC address of a cluster, what command would you run?
The CPD daemon is a Firewall Kernel Process that does NOT do which of the following?
Check Point Management (cpm) is the main management process in that it provides the architecture for a consolidated management console. It empowers the migration from legacy Client-side logic to Server-side logic. The cpm process:
Packet acceleration (SecureXL) identities connections by several attributes. Which of the attributes is NOT used for identifying connection?
In R81.20 a new feature dynamic log distribution was added. What is this for?
- Configure the Security Gateway to distribute logs between multiple active Log Servers to support a better rate of Logs and Log Servers redundancy
- In case of a Management High Availability the management server stores the logs dynamically on the member with the most available disk space in /var/log
- Synchronize the log between the primary and secondary management server in case of a Management High Availability
Which file contains the host address to be published, the MAC address that needs to be associated with the IP Address, and the unique IP of the interface that responds to ARP request?
You want to verify if your management server is ready to upgrade to R81.20. What tool could you use in this process?
Which tool provides a list of trusted files to the administrator so they can specify to the Threat Prevention blade that these files do not need to be scanned or analyzed?
Ken wants to obtain a configuration lock from other administrator on R81 Security Management Server. He can do this via WebUI or via CLI.
Which command should he use in CLI? (Choose the correct answer.)
After the initial installation on Check Point appliance, you notice that the Management-interface and default gateway are incorrect.
Which commands could you use to set the IP to 192.168.80.200/24 and default gateway to 192.168.80.1.
What kind of information would you expect to see using the sim affinity command?
Capsule Connect and Capsule Workspace both offer secured connection for remote users who are using their mobile devices. However, there are differences between the two.
Which of the following statements correctly identify each product's capabilities?
Joey wants to upgrade from R75.40 to R81 version of Security management. He will use Advanced Upgrade with Database Migration method to achieve this.
What is one of the requirements for his success?
Pamela is Cyber Security Engineer working for Global Instance Firm with large scale deployment of Check Point Enterprise Appliances using GAiA/R81.20. Company’s Developer Team is having random access issue to newly deployed Application Server in DMZ’s Application Server Farm Tier and blames DMZ Security Gateway as root cause. The ticket has been created and issue is at Pamela’s desk for an investigation. Pamela decides to use Check Point’s Packet Analyzer Tool-fw monitor to iron out the issue during approved Maintenance window.
What do you recommend as the best suggestion for Pamela to make sure she successfully captures entire traffic in context of Firewall and problematic traffic?
Fill in the blank: The “fw monitor” tool can be best used to troubleshoot ____________________.
One of major features in R81 SmartConsole is concurrent administration.
Which of the following is NOT possible considering that AdminA, AdminB and AdminC are editing the same Security Policy?
To ensure that VMAC mode is enabled, which CLI command should you run on all cluster members?
After trust has been established between the Check Point components, what is TRUE about name and IP-address changes?
Fill in the blank: Browser-based Authentication sends users to a web page to acquire identities using ________ .
What CLI command compiles and installs a Security Policy on the target’s Security Gateways?
SandBlast Mobile identifies threats in mobile devices by using on-device, network, and cloud-based algorithms and has four dedicated components that constantly work together to protect mobile devices and their data. Which component is NOT part of the SandBlast Mobile solution?
What is a feature that enables VPN connections to successfully maintain a private and secure VPN session without employing Stateful Inspection?
During inspection of your Threat Prevention logs you find four different computers having one event each with a Critical Severity. Which of those hosts should you try to remediate first?
What is the correct command to observe the Sync traffic in a VRRP environment?
Which one of these features is NOT associated with the Check Point URL Filtering and Application Control Blade?
When detected, an event can activate an Automatic Reaction. The SmartEvent administrator can create and configure one Automatic Reaction, or many, according to the needs of the system. Which of the following statement is false and NOT part of possible automatic reactions:
How many versions, besides the destination version, are supported in a Multi-Version Cluster Upgrade?
Rugged appliances are small appliances with ruggedized hardware and like Quantum Spark appliance they use which operating system?
When a packet arrives at the gateway, the gateway checks it against the rules in the hop Policy Layer, sequentially from top to bottom, and enforces the first rule that matches a packet. Which of the following statements about the order of rule enforcement is true?
What API command below creates a new host object with the name "My Host" and IP address of "192 168 0 10"?
SmartEvent uses it's event policy to identify events. How can this be customized?
Which Check Point process provides logging services, such as forwarding logs from Gateway to Log Server, providing Log Export API (LEA) & Event Logging API (EL-A) services.
Check Point Support in many cases asks you for a configuration summary of your Check Point system. This is also called:
CoreXL is NOT supported when one of the following features is enabled: (Choose three)
In the R81 SmartConsole, on which tab are Permissions and Administrators defined?
What level of CPU load on a Secure Network Distributor would indicate that another may be necessary?
What could NOT be a reason for synchronization issues in a Management HA environment?
What is the name of the secure application for Mail/Calendar for mobile devices?
: 156
VPN Link Selection will perform the following when the primary VPN link goes down?
In SmartEvent, what are the different types of automatic reactions that the administrator can configure?
When gathering information about a gateway using CPINFO, what information is included or excluded when using the “-x” parameter?
Which process is available on any management product and on products that require direct GUI access, such as SmartEvent and provides GUI client communications, database manipulation, policy compilation and Management HA synchronization?
Which web services protocol is used to communicate to the Check Point R81 Identity Awareness Web API?
Which statements below are CORRECT regarding Threat Prevention profiles in Smart Dashboard?
When simulating a problem on ClusterXL cluster with cphaprob –d STOP -s problem -t 0 register, to initiate a failover on an active cluster member, what command allows you remove the problematic state?
True or False: In R81, more than one administrator can login to the Security Management Server with write permission at the same time.
What key is used to save the current CPView page in a filename format cpview_”cpview process ID”.cap”number of captures”?
Which file gives you a list of all security servers in use, including port number?
Fill in the blank. Once a certificate is revoked from the Security Gateway by the Security Management Server, the certificate information is ________ .
In Logging and Monitoring, the tracking options are Log, Detailed Log and Extended Log. Which of the following options can you add to each Log, Detailed Log and Extended Log?
Which of the following technologies extracts detailed information from packets and stores that information in state tables?
Check Point APIs allow system engineers and developers to make changes to their organization’s security policy with CLI tools and Web Services for all the following except:
Which of the following is NOT a VPN routing option available in a star community?
In the Check Point Firewall Kernel Module, each Kernel is associated with a key, which specifies the type of traffic applicable to the chain module. For Stateful Mode configuration, chain modules marked with __________________ will not apply.
For best practices, what is the recommended time for automatic unlocking of locked admin accounts?
The ____ software blade package uses CPU-level and OS-level sandboxing in order to detect and block malware.
As an administrator, you may be required to add the company logo to reports. To do this, you would save the logo as a PNG file with the name ‘cover-company-logo.png’ and then copy that image file to which directory on the SmartEvent server?
You want to gather and analyze threats to your mobile device. It has to be a lightweight app. Which application would you use?
Which configuration file contains the structure of the Security Server showing the port numbers, corresponding protocol name, and status?
After making modifications to the $CVPNDIR/conf/cvpnd.C file, how would you restart the daemon?
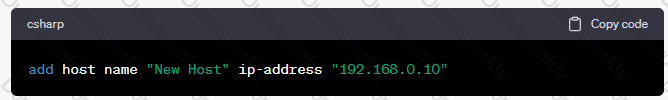
What API command below creates a new host with the name “New Host” and IP address of “192.168.0.10”?
Customer’s R81 management server needs to be upgraded to R81.20. What is the best upgrade method when the management server is not connected to the Internet?
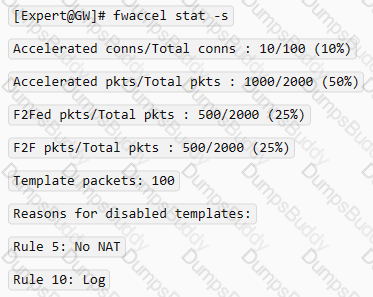
An administrator would like to troubleshoot why templating is not working for some traffic. How can he determine at which rule templating is disabled?
John is using Management HA. Which Smartcenter should be connected to for making changes?
NO: 180
What command can you use to have cpinfo display all installed hotfixes?
To enable Dynamic Dispatch on Security Gateway without the Firewall Priority Queues, run the following command in Expert mode and reboot:
You want to store the GAIA configuration in a file for later reference. What command should you use?


 Firewall
Firewall Firewall
Firewall Firewall
Firewall